Secure Access By Duo
Duo Single Sign On For Cisco Secure Access Duo Security Duo security offers solutions to protect organizations from identity threats. explore duo identity security, phishing resistant mfa, and other solutions. Cisco duo, a pioneer in identity security and authentication, focuses on verifying user identity to ensure that only authorized individuals gain access, enhancing security without introducing friction.
Duo Single Sign On For Cisco Secure Access Cisco Duo When setting up multi factor authentication using duo, there are some considerations to be made for how the authentication interacts with absolute secure access. there are 3 different ways that customers can use duo to integrate with secure access. Cisco duo, the industry leading solution for identity security with end to end phishing resistance, security first iam, multi factor authentication (mfa) and more. Duo single sign on adds two factor authentication and flexible security policies to cisco secure access sso logins, complete with inline self service enrollment and duo prompt. Duo access gateway is an on premises solution that secures access to cloud applications with your users’ existing directory credentials (like microsoft active directory or google workspace accounts) using the security assertion markup language (saml) 2.0 authentication standard.
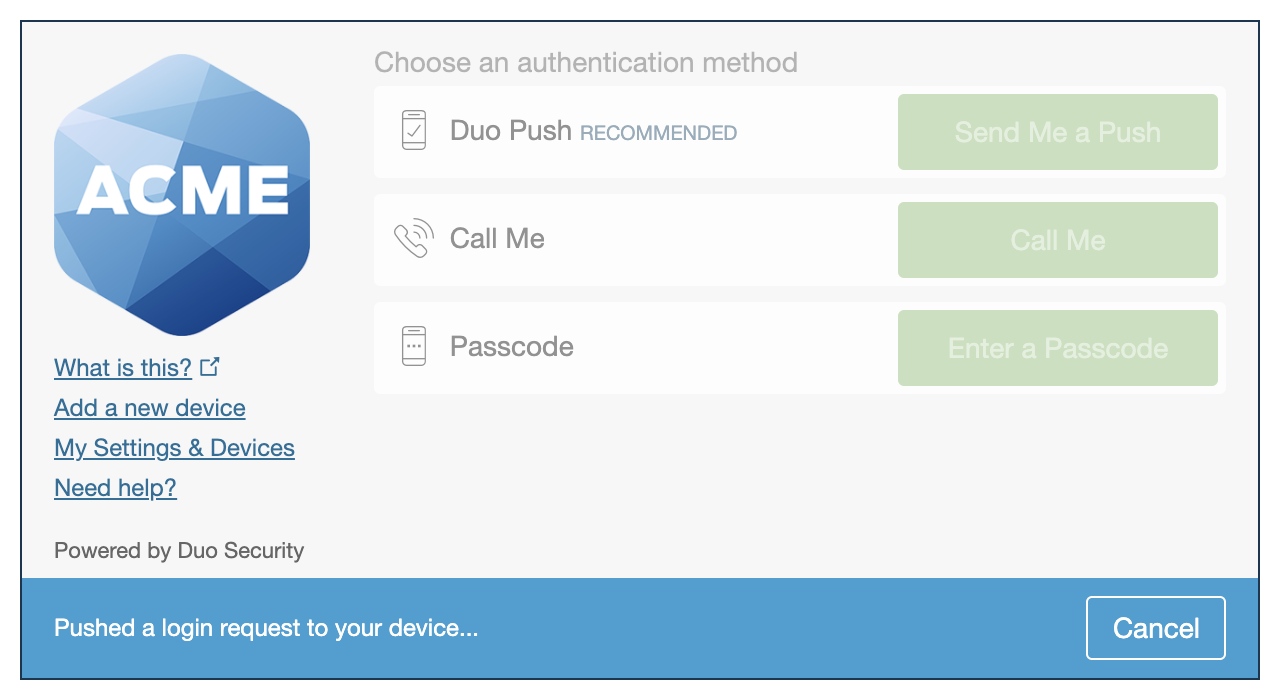
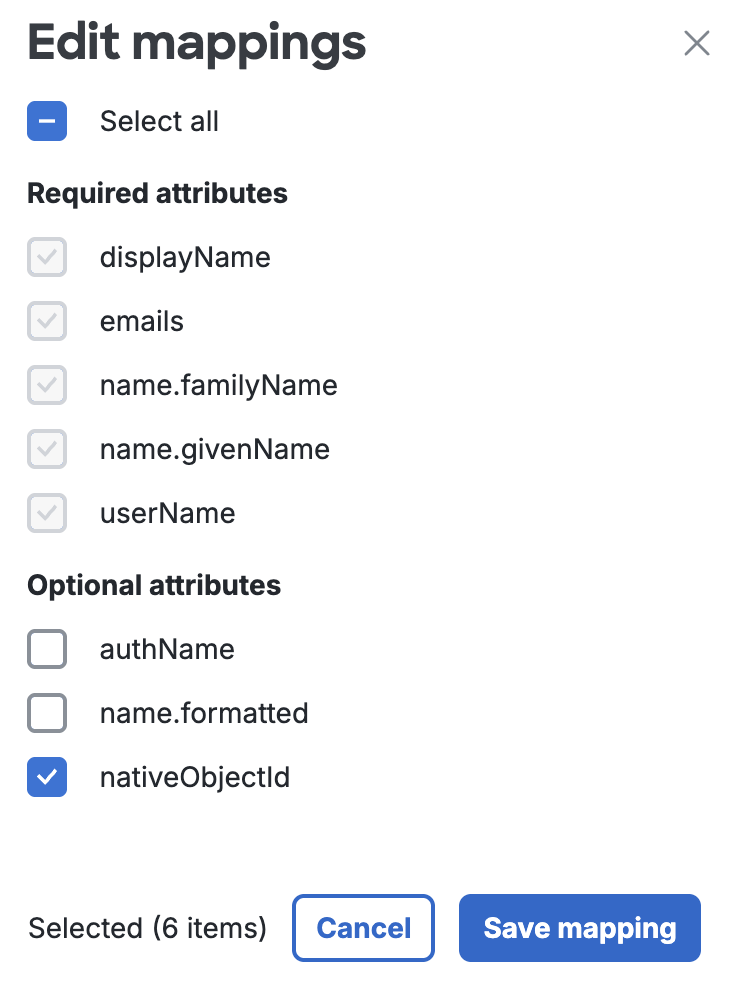
Duo Single Sign On For Cisco Secure Access Cisco Duo Duo single sign on adds two factor authentication and flexible security policies to cisco secure access sso logins, complete with inline self service enrollment and duo prompt. Duo access gateway is an on premises solution that secures access to cloud applications with your users’ existing directory credentials (like microsoft active directory or google workspace accounts) using the security assertion markup language (saml) 2.0 authentication standard. Duo multi factor authentication protects your organization's data at every access attempt, from any device, and from any location. it verifies user trust, establishes device trust, and provides secure access to company apps and networks from wherever users are logging in. Learn how to integrate duo’s security solutions with a wide range of devices & apps. browse detailed how to & set up guides on authentication & secure data. Configure the duo security saml idp with secure access by uploading the duo security xml metadata file to secure access, or alternatively add the duo security metadata in secure access manually. Duo's access management provides a flexible and powerful way to secure access in today's hybrid and multi cloud environments. it ensures that every access attempt is verified for both user identity and device trustworthiness, significantly reducing the risk of unauthorized access and data breaches.

Duo Single Sign On For Cisco Secure Access Cisco Duo Duo multi factor authentication protects your organization's data at every access attempt, from any device, and from any location. it verifies user trust, establishes device trust, and provides secure access to company apps and networks from wherever users are logging in. Learn how to integrate duo’s security solutions with a wide range of devices & apps. browse detailed how to & set up guides on authentication & secure data. Configure the duo security saml idp with secure access by uploading the duo security xml metadata file to secure access, or alternatively add the duo security metadata in secure access manually. Duo's access management provides a flexible and powerful way to secure access in today's hybrid and multi cloud environments. it ensures that every access attempt is verified for both user identity and device trustworthiness, significantly reducing the risk of unauthorized access and data breaches.
Comments are closed.