Section 3 7 Modular Arithmetic And Ciphers

Exploring Modular Arithmetic An Introduction To Congruences So we count 3 months back from april and get january we want to create a new arithmetic based on remainders we always have to keep in mind the number that we’re dividing by to get the remainders this number is called the modulus if we are talking about a “days of the week problem,” the modulus is 7 the possible remainders we can get are 0. Learn the basics of modular arithmetic and how it's used in cryptography. a beginner friendly guide with examples, explanations, and interactive tools.
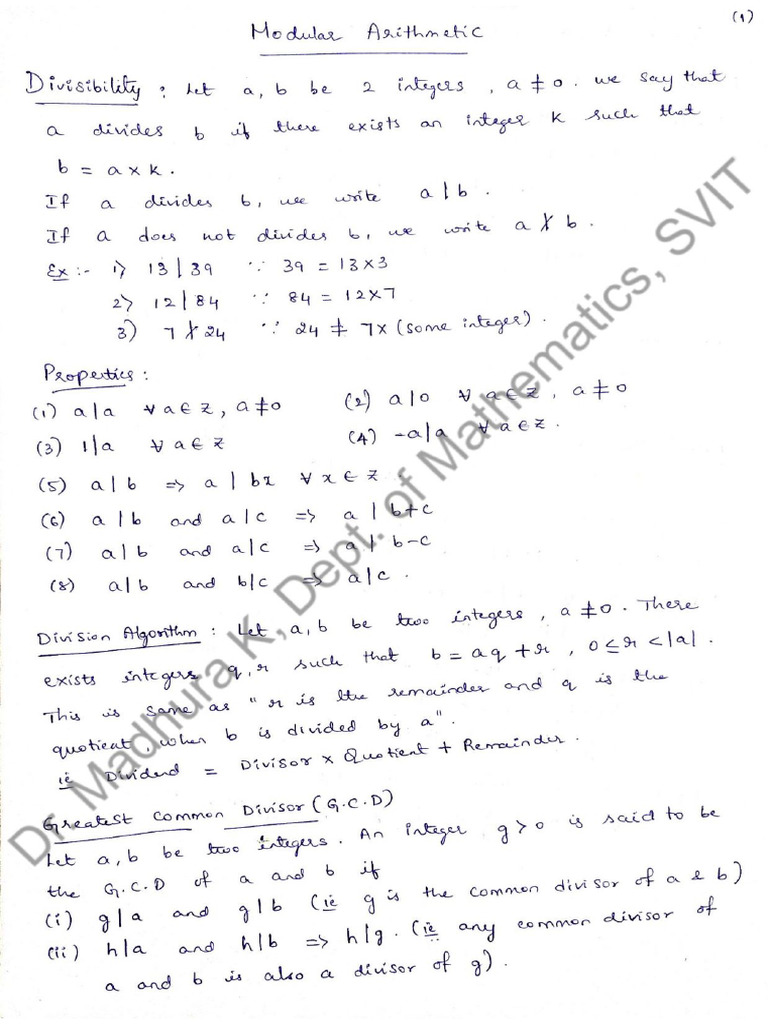
Module 4 Modular Arithmetic Pdf When we studied id numbers, we found that many of these systems use remainders to compute the check digits. remainders have many applications beyond check digit systems. counting remainders. suppose today is monday, and you want to know what day of the week it will be 72 days from now. Math for liberal studies. section 3.7: modular arithmetic and ciphers. counting remainders. when we studied id numbers, we found that many of these systems use remainders to compute the check digits remainders have many applications beyond check digit systems. counting remainders. slideshow. Discover the fundamentals of modular arithmetic and its applications in cryptography, including examples like the caesar and affine ciphers. Modular arithmetic and cryptography! what is modular arithmetic? in modular arithmetic, we select an integer, n, to be our \modulus". then our system of numbers only includes the numbers 0, 1, 2, 3, , n 1. in order to have arithmetic make sense, we have the numbers \wrap around" once they reach n.

Modular Arithmetic Part 1 Pdf Pdf Discover the fundamentals of modular arithmetic and its applications in cryptography, including examples like the caesar and affine ciphers. Modular arithmetic and cryptography! what is modular arithmetic? in modular arithmetic, we select an integer, n, to be our \modulus". then our system of numbers only includes the numbers 0, 1, 2, 3, , n 1. in order to have arithmetic make sense, we have the numbers \wrap around" once they reach n. Almost any cipher from the caesar cipher to the rsa cipher use it. thus, i will show you here how to perform mod addition, mod subtraction, mod multiplication, mod division and mod exponentiation. Master the mathematics behind the affine cipher. learn modular arithmetic, modular inverses, the encryption formula e (x) = (ax b) mod 26, and how to crack affine ciphers step by step. It includes exercises on congruences, operations in modular arithmetic, and methods for encrypting and decrypting messages using ciphers like the caesar and vigenère ciphers. Messages are first converted to numbers (e.g., a becomes 1, b becomes 2, etc.) and then the numbers are transformed using modular arithmetic. the steps of this procedure are described on the next page. the keys for the rsa public key cryptosystem are numbers constructed by the receiver.
Section 3 7 Modular Arithmetic And Ciphers Almost any cipher from the caesar cipher to the rsa cipher use it. thus, i will show you here how to perform mod addition, mod subtraction, mod multiplication, mod division and mod exponentiation. Master the mathematics behind the affine cipher. learn modular arithmetic, modular inverses, the encryption formula e (x) = (ax b) mod 26, and how to crack affine ciphers step by step. It includes exercises on congruences, operations in modular arithmetic, and methods for encrypting and decrypting messages using ciphers like the caesar and vigenère ciphers. Messages are first converted to numbers (e.g., a becomes 1, b becomes 2, etc.) and then the numbers are transformed using modular arithmetic. the steps of this procedure are described on the next page. the keys for the rsa public key cryptosystem are numbers constructed by the receiver.
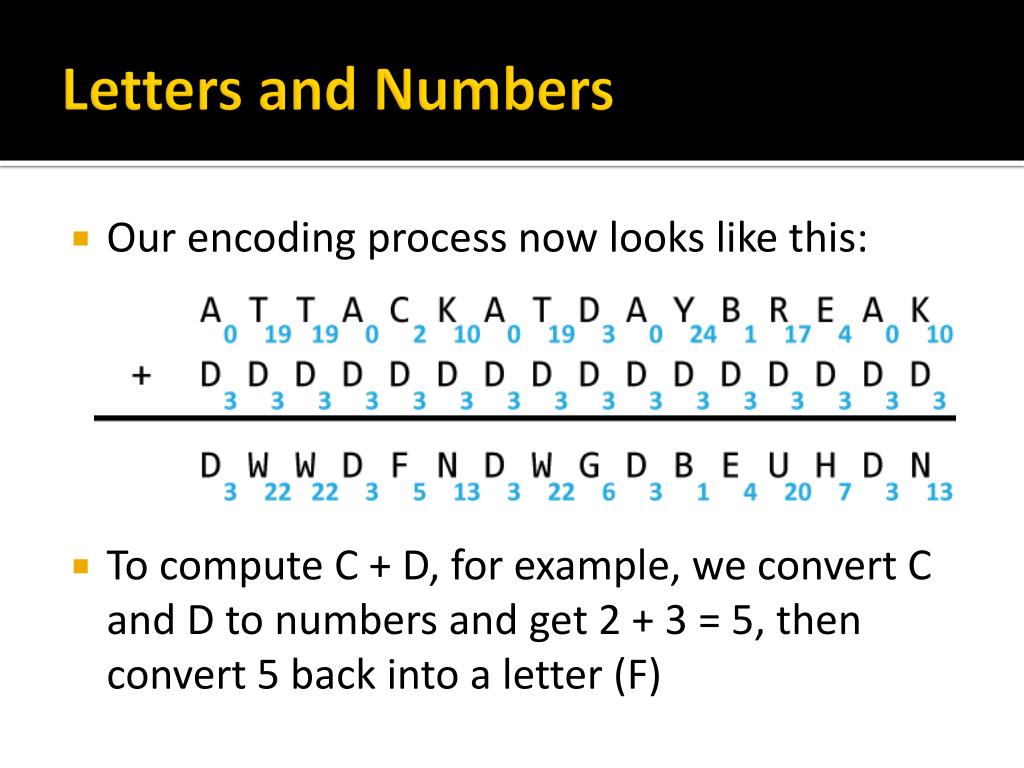
Ppt Section 3 7 Modular Arithmetic And Ciphers Powerpoint It includes exercises on congruences, operations in modular arithmetic, and methods for encrypting and decrypting messages using ciphers like the caesar and vigenère ciphers. Messages are first converted to numbers (e.g., a becomes 1, b becomes 2, etc.) and then the numbers are transformed using modular arithmetic. the steps of this procedure are described on the next page. the keys for the rsa public key cryptosystem are numbers constructed by the receiver.

Ppt Section 3 7 Modular Arithmetic And Ciphers Powerpoint
Comments are closed.