Secrets Management Explained Stop Hardcoding Api Keys Passwords

12 000 Api Keys And Passwords Found In Public Datasets Used For Llm From api keys to database passwords, sensitive information should never be embedded directly into source code. instead, developers should adopt secure practices such as using secret management tools, storing secrets in environment variables, and automating secret detection in ci cd pipelines. Secrets management is your centralized system for storing, accessing, and rotating sensitive credentials like api keys, database passwords, certificates, and tokens. it prevents hardcoded secrets in code repositories, enforces least privilege access, and provides audit trails for credential usage.

12 000 Api Keys And Passwords Found In Public Datasets Used For Llm Learn how to securely handle api keys, tokens, and credentials in your code. explore secrets managers, environment variables, and best practices for devs. Stop hardcoding api keys — try this secret instead! almost every application today uses some kind of api — be it payment gateway, google maps, firebase, or openai api. and when using apis,. Learn everything about secrets management what it is, why it matters, best practices, and the tools teams use to protect api keys, passwords, certificates, and credentials. Protect cloud apps! learn secure storage of secrets & api keys. avoid hardcoding, use secret managers, rotation, encryption, & access control for robust security.
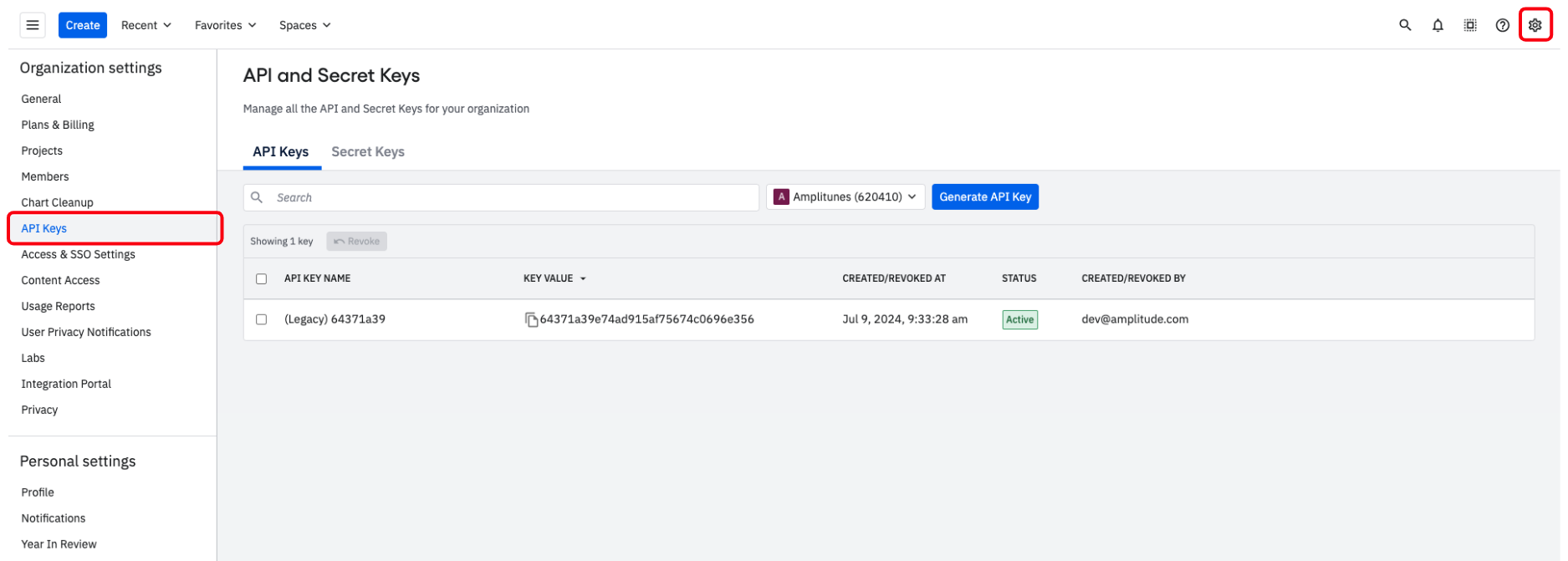
Manage Your Api Keys And Secret Keys Amplitude Learn everything about secrets management what it is, why it matters, best practices, and the tools teams use to protect api keys, passwords, certificates, and credentials. Protect cloud apps! learn secure storage of secrets & api keys. avoid hardcoding, use secret managers, rotation, encryption, & access control for robust security. Explore expert api key management best practices to prevent leaks and secure credentials. download our actionable cheat sheet to strengthen your security. Often, you can either encrypt a secret with a key managed at the secrets management service or use a key management solution from the cloud provider to encrypt the secret. Avoid embedding secrets such as api keys, passwords, or cryptographic keys directly into source code. doing so introduces significant security risks and makes your application more vulnerable to attacks. The practices outlined in this guide provide a foundation for robust api key security adapted to current threats and best practices as of 2025. success requires treating api key security as an ongoing process rather than one time implementation.
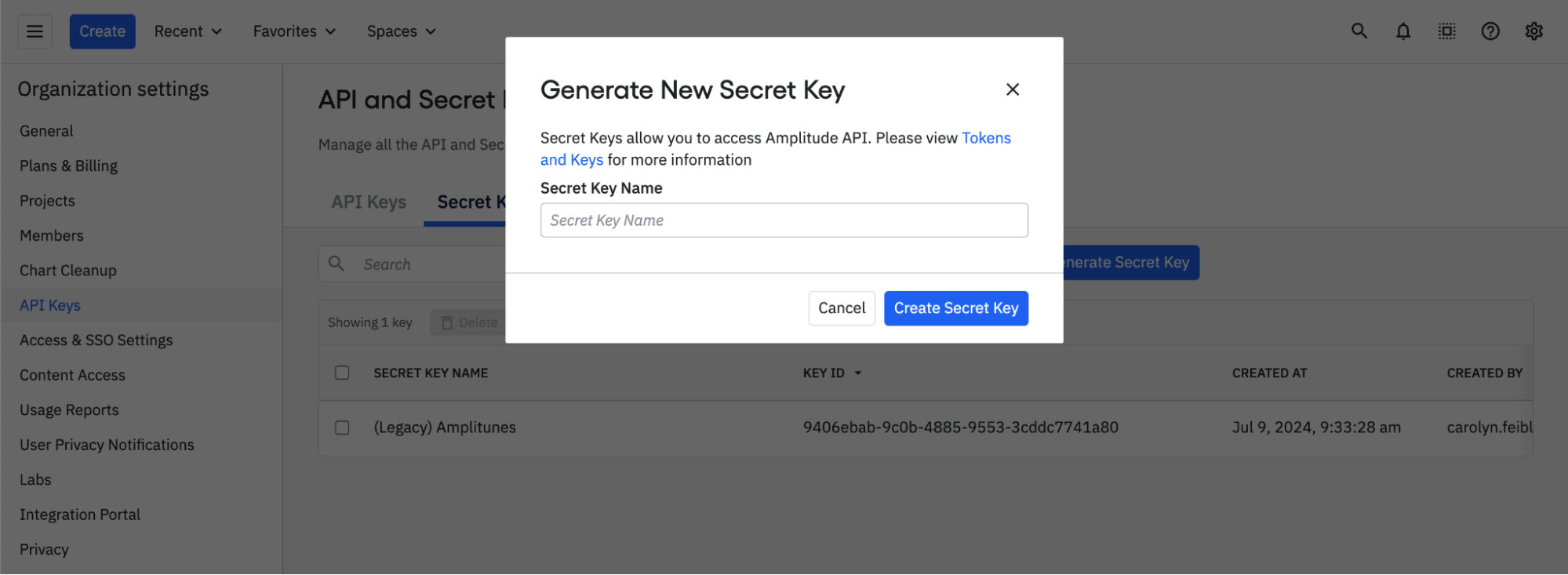
Manage Your Api Keys And Secret Keys Amplitude Explore expert api key management best practices to prevent leaks and secure credentials. download our actionable cheat sheet to strengthen your security. Often, you can either encrypt a secret with a key managed at the secrets management service or use a key management solution from the cloud provider to encrypt the secret. Avoid embedding secrets such as api keys, passwords, or cryptographic keys directly into source code. doing so introduces significant security risks and makes your application more vulnerable to attacks. The practices outlined in this guide provide a foundation for robust api key security adapted to current threats and best practices as of 2025. success requires treating api key security as an ongoing process rather than one time implementation.
Comments are closed.