Sd Access
Sd Access Wireless Design And Deployment Guide Cisco Software defined access (sd access) helps organizations enable policy based network automation by automating user and device policy, aiding onboarding, secure segmentation, iot integration, and guest access. Webex spaces will be moderated by the speaker until february 28, 2025. traffic should be explicitly permitted with the use of security group access lists (sgacls). fair understanding of traffic flows within their network.

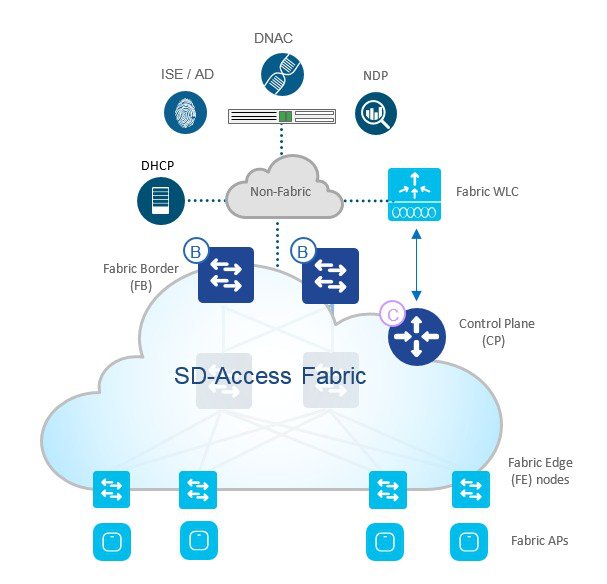
Sd Access Wireless Design And Deployment Guide Cisco Learn about cisco software defined access (sda), a technology that extends virtualization to the network’s access layer. see the four layers of the sda architecture and the main components of the cisco campus fabric solution. Cisco sd access is a network access control method that uses cisco dna center, ise, ndp, and network infrastructure to create a virtual overlay over the physical network. it provides user mobility, security, segmentation, and automation based on user identity and intent. With cisco sd access, you can manage and secure internet of things (iot) devices and user network access through zero trust workplace capabilities. implement zero trust security and secure access for all users and devices—from any location, to all of your applications and network. This lesson explains the components of cisco's sd access: complete automation of your campus network, similar to how sdn or cloud solutions work.
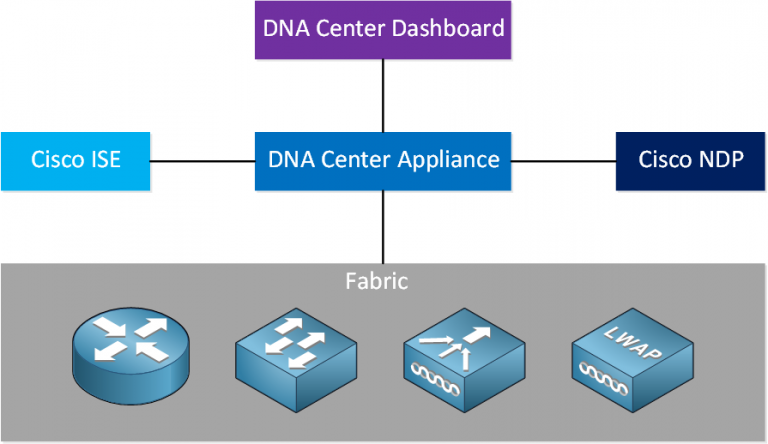
Introduction To Sd Access With cisco sd access, you can manage and secure internet of things (iot) devices and user network access through zero trust workplace capabilities. implement zero trust security and secure access for all users and devices—from any location, to all of your applications and network. This lesson explains the components of cisco's sd access: complete automation of your campus network, similar to how sdn or cloud solutions work. Sd access, or software defined access, is an innovative networking solution from cisco that leverages automation and virtualization technologies to streamline network operations. Software defined access, or sd access, applies the principles of software defined networking, or sdn, to the access edge of the network. sd access puts the access edge under the management of a centralized network controller instead of managing each access switch as an independent entity. One of its core software packages is sd access, which simplifies network design, automates provisioning, and strengthens security across campus environments. Sd access automates user and device policy for any application across the wireless and wired network via a single network fabric. it is a transformational shift. it allows it to set network access in minutes for any user, device, or application, without compromising on security.

The Who And How Of Sd Access Sd access, or software defined access, is an innovative networking solution from cisco that leverages automation and virtualization technologies to streamline network operations. Software defined access, or sd access, applies the principles of software defined networking, or sdn, to the access edge of the network. sd access puts the access edge under the management of a centralized network controller instead of managing each access switch as an independent entity. One of its core software packages is sd access, which simplifies network design, automates provisioning, and strengthens security across campus environments. Sd access automates user and device policy for any application across the wireless and wired network via a single network fabric. it is a transformational shift. it allows it to set network access in minutes for any user, device, or application, without compromising on security.
Comments are closed.