Scada System Vulnerabilities
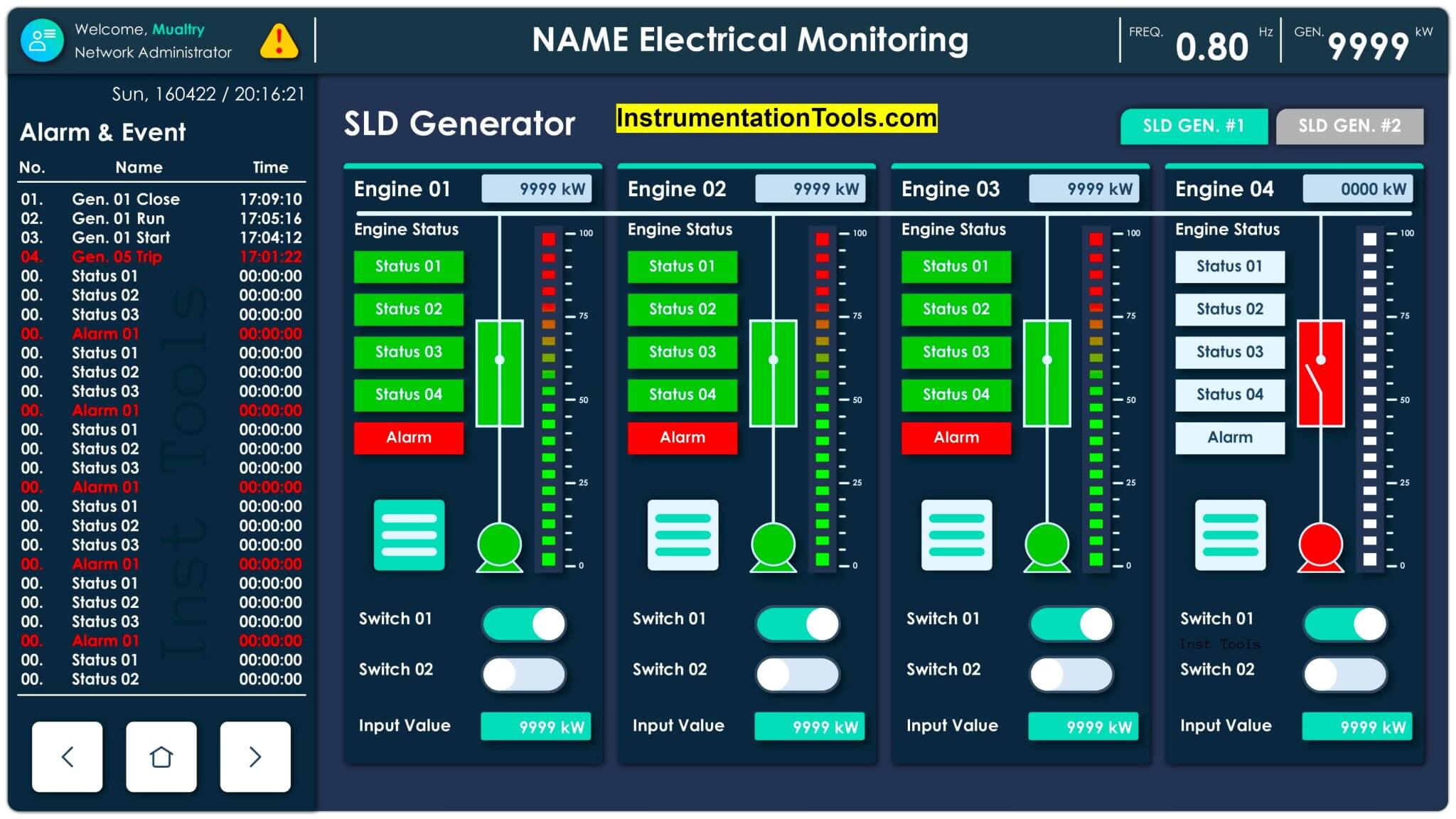
Scada System Vulnerabilities The goal of this survey is to explore the security vulnerabilities of scada systems and classify the threats accordingly. in this project, we initially reviewed scada systems from different scopes, including architecture, vulnerabilities, attacks, intrusion detection techniques (ids) and testbeds. This blog post presents nine common scada system vulnerabilities as well as a few strategies to secure them. supervisory control and data acquisition (scada) systems are pivotal in managing and monitoring industrial operations across sectors such as energy, water and manufacturing.

Scada System Vulnerabilities Term As a basis for identifying opportunities to close the gap on scada vulnerabilities, this research explored areas of scada systems that should be subjected to more focused vulnerability analysis to guide the development of methodologies that can be useful to better secure them. Scada security is the practice of protecting supervisory control and data acquisition systems from unauthorized access, tampering, and cyberattacks. scada systems monitor and control physical processes across large geographic areas — power grids, water pipelines, oil and gas networks, and transportation systems. By identifying and understanding the various cyber attack vectors and vulnerabilities specific to scada systems, organizations can develop robust defence mechanisms to protect critical infrastructure. This post covers what security measures teams need to understand and how time series monitoring can help turn scada's weaknesses into a security advantage.

Multiple Scada Vulnerabilities Let Attackers Trigger Dos Elevate By identifying and understanding the various cyber attack vectors and vulnerabilities specific to scada systems, organizations can develop robust defence mechanisms to protect critical infrastructure. This post covers what security measures teams need to understand and how time series monitoring can help turn scada's weaknesses into a security advantage. This article explores vulnerabilities in supervisory control and data acquisition (scada) systems used in both transmission and distribution substations across the electric grid. Protect your critical infrastructure with comprehensive scada security. learn best practices and safeguard against cyberattacks. Scada systems connected to unaudited dial up lines or remote access servers give attackers convenient backdoor access to the ot network as well as the corporate lan. security gaps are created when it and ot personnel differ in their approach to securing industrial controls. Learn how scada systems work, why they’re difficult to secure, and a practical framework for scada cyber security including segmentation, monitoring, and safe testing using digital twins.

Scada Vulnerabilities Royalty Free Images Stock Photos Pictures This article explores vulnerabilities in supervisory control and data acquisition (scada) systems used in both transmission and distribution substations across the electric grid. Protect your critical infrastructure with comprehensive scada security. learn best practices and safeguard against cyberattacks. Scada systems connected to unaudited dial up lines or remote access servers give attackers convenient backdoor access to the ot network as well as the corporate lan. security gaps are created when it and ot personnel differ in their approach to securing industrial controls. Learn how scada systems work, why they’re difficult to secure, and a practical framework for scada cyber security including segmentation, monitoring, and safe testing using digital twins.

Scada Vulnerabilities Innovirtuoso Scada systems connected to unaudited dial up lines or remote access servers give attackers convenient backdoor access to the ot network as well as the corporate lan. security gaps are created when it and ot personnel differ in their approach to securing industrial controls. Learn how scada systems work, why they’re difficult to secure, and a practical framework for scada cyber security including segmentation, monitoring, and safe testing using digital twins.
Comments are closed.