Sap Security Pdf Computer Security Security

Sap Security Pdf Our sap cyber security assessment looks beyond the traditional lens of financial and regulatory compliance and provides a holistic view of security for the entire sap technology stack. Sap cyber security free download as pdf file (.pdf), text file (.txt) or read online for free. this document discusses kpmg's sap cyber security services. it describes the increasing threats to sap systems from cyber attackers and the need to secure the entire sap technology stack.

Sap Cybersecurity 2018 Pdf Security Computer Security It covers various authentication methods, database security, network and communication security and protecting standard users and other best practices that should be followed in maintaining your sap environment. Owing to the particularly sensitive nature of the work carried out at sap, we have established a list of special security measures, summarized as “golden rules” for sap staf and customers. Those lagging in cybersecurity posture are focused on training end users to protect credentials (53%), conducting regular audits and security assessments (47%), and integrating sap system data with security operations (47%). To assist you in securing sap s 4hana, we provide this security guide. the secure operations map is a reference model to structure the broad area of security for content, discussions, and as a basis for a 360° view on security.

Computer Security Pdf Those lagging in cybersecurity posture are focused on training end users to protect credentials (53%), conducting regular audits and security assessments (47%), and integrating sap system data with security operations (47%). To assist you in securing sap s 4hana, we provide this security guide. the secure operations map is a reference model to structure the broad area of security for content, discussions, and as a basis for a 360° view on security. Traditionally, best practices were to keep business critical sap systems on premises and to install layers of security around them, creating a theoretical and impenetrable fortress of castle walls and moats. This paper discusses the critical importance of security within the sap ecosystem, particularly in the context of increasing collaboration between businesses and the transition of applications and data to the internet. Key security best practices identified include strong user access management, segregation of duties, timely patching, encryption, and continuous monitoring using sap's grc tools. these measures help organizations reduce vulnerabilities, block unauthorized access, and ensure integrity. Design and develop a process for using accelerators like sap grc in security build and maintenance phases to maximize efficiency. underpin technical aspects of the design with a robust sap security governance framework.
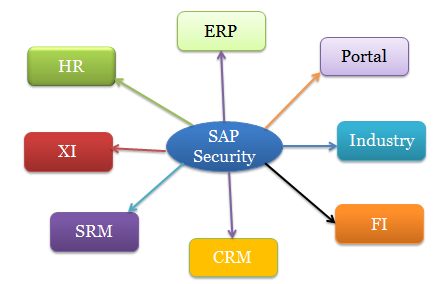
What Is Sap Security An Overview Of Sap Security Module Sap Tutorials Traditionally, best practices were to keep business critical sap systems on premises and to install layers of security around them, creating a theoretical and impenetrable fortress of castle walls and moats. This paper discusses the critical importance of security within the sap ecosystem, particularly in the context of increasing collaboration between businesses and the transition of applications and data to the internet. Key security best practices identified include strong user access management, segregation of duties, timely patching, encryption, and continuous monitoring using sap's grc tools. these measures help organizations reduce vulnerabilities, block unauthorized access, and ensure integrity. Design and develop a process for using accelerators like sap grc in security build and maintenance phases to maximize efficiency. underpin technical aspects of the design with a robust sap security governance framework.
Comments are closed.