Safeguarding Iot Ecosystem
Safeguarding Iot Ecosystem This chapter explores the essential concerns of security, privacy, and interoperability within the iot ecosystem, examining the challenges, potential risks, and innovative solutions that aim to address these concerns. Our findings underscore the necessity for a multi faceted approach that combines technical, organizational, and regulatory measures to safeguard iot ecosystems.

Iot Ecosystem Gateway Security Challenges Iot Security And Privacy The rapid expansion of iot technology presents significant security challenges that must be carefully addressed to establish a secure iot ecosystem. this article comprehensively examines security issues across different layers of iot and proposes corresponding countermeasures. To address these pressing security concerns, researchers and industry leaders have developed a range of innovative approaches that aim to enhance the resilience of iot ecosystems. these cutting edge techniques prioritize the protection of sensor data integrity and the preservation of user privacy. Discover iot security best practices and strategies to safeguard your iot ecosystem. learn how to secure devices, networks, and data with a robust iot security strategy. Hyperconnected iot ecosystems have become crucial for organizational operations; yet, existing governance structures remain fragmented, are technology centric, and not well equipped to manage the risks, compliance pressures, and resilience needs of iot. this paper presents an integrated, theory based information security governance model that is tailored for iot driven organizations. a.
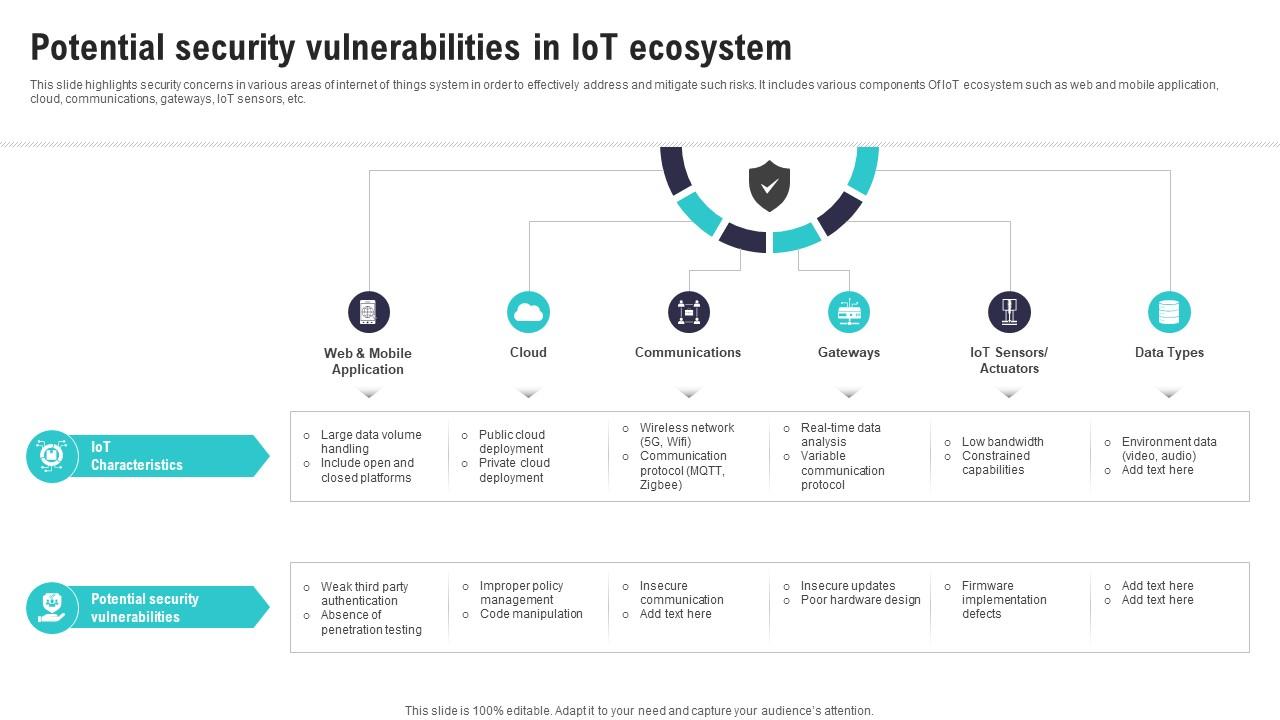
Potential Security Vulnerabilities In Iot Ecosystem Iot Security And Discover iot security best practices and strategies to safeguard your iot ecosystem. learn how to secure devices, networks, and data with a robust iot security strategy. Hyperconnected iot ecosystems have become crucial for organizational operations; yet, existing governance structures remain fragmented, are technology centric, and not well equipped to manage the risks, compliance pressures, and resilience needs of iot. this paper presents an integrated, theory based information security governance model that is tailored for iot driven organizations. a. Discover how to protect iot data privacy: encryption, firmware updates, privacy by design, and regulatory compliance. secure your connected devices confidently in 2025. Building security into iot from the start is key to trust, resilience, and long term success. from connected cars and wearable medical devices to smart meters and industrial sensors, the internet of things (iot) is embedded in nearly every aspect of daily life. To protect iot devices from being hacked, it is essential to use strong, unique passwords and regularly update the firmware. it is also recommended to use encryption and secure communication protocols, such as https or ssl, to prevent unauthorized access to the device or its network. This article will explore the security challenges in the iot landscape and discuss promising ways to protect against these emerging threats, offering a hopeful outlook for the future of iot security.

Icons Slide For Iot Security And Privacy Safeguarding The Digital Discover how to protect iot data privacy: encryption, firmware updates, privacy by design, and regulatory compliance. secure your connected devices confidently in 2025. Building security into iot from the start is key to trust, resilience, and long term success. from connected cars and wearable medical devices to smart meters and industrial sensors, the internet of things (iot) is embedded in nearly every aspect of daily life. To protect iot devices from being hacked, it is essential to use strong, unique passwords and regularly update the firmware. it is also recommended to use encryption and secure communication protocols, such as https or ssl, to prevent unauthorized access to the device or its network. This article will explore the security challenges in the iot landscape and discuss promising ways to protect against these emerging threats, offering a hopeful outlook for the future of iot security.
Comments are closed.