Saas Security Api Setup And Configuration
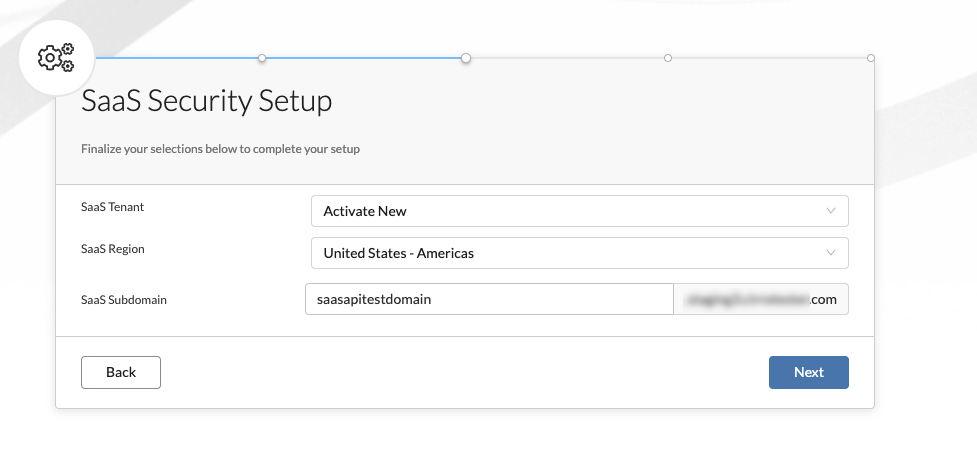
Saas Security Api Lab Define internal domains, add trusted users and domains, configure acceptable levels of asset exposure, and set the time zone and language for saas security. This guide describes the benefits of using saas security and the steps necessary for configuring zscaler internet access (zia) to add saas security to your security posture.
Activate Data Security That’s why protecting apis has become a cornerstone of modern saas ecosystem security. this guide outlines the essential strategies and controls for building api resilience: how to prevent common vulnerabilities, monitor for misuse, and align your api governance with compliance frameworks like gdpr, hipaa, and soc 2. Casb (cloud access security broker) solutions can enforce security policies based on user behavior and configuration settings. with sap s 4hana cloud public edition 2402, sap provides apis to enable customers to gain insights into their security configuration settings. From encryption protocols to access controls, this comprehensive guide delves into the intricate realm of securing restful apis within saas products. by choosing the right tech stack for saas, teams can handle authentication, data validation, and authorization more effectively. You can protect your api using strategies like generating ssl certificates, configuring a web application firewall, setting throttling targets, and only allowing access to your api from a virtual private cloud (vpc). in this section you can learn how to enable these capabilities using api gateway.

Api Security Best Practices For Saas Platforms From encryption protocols to access controls, this comprehensive guide delves into the intricate realm of securing restful apis within saas products. by choosing the right tech stack for saas, teams can handle authentication, data validation, and authorization more effectively. You can protect your api using strategies like generating ssl certificates, configuring a web application firewall, setting throttling targets, and only allowing access to your api from a virtual private cloud (vpc). in this section you can learn how to enable these capabilities using api gateway. In this guide, we’ll explore the 10 best practices for api security in saas, explain why they matter, and provide real world strategies to help you secure your platform and customers. Learn how to secure api authentication and authorization in saas apps with oauth 2.0, jwt best practices, and multi layered security strategies. The definitive guide to understanding saas security. learn about saas security including challenges, benefits, and more. This blog explores the essential steps for ensuring your saas platform remains protected by implementing robust api security practices, especially in offshore software development environments.
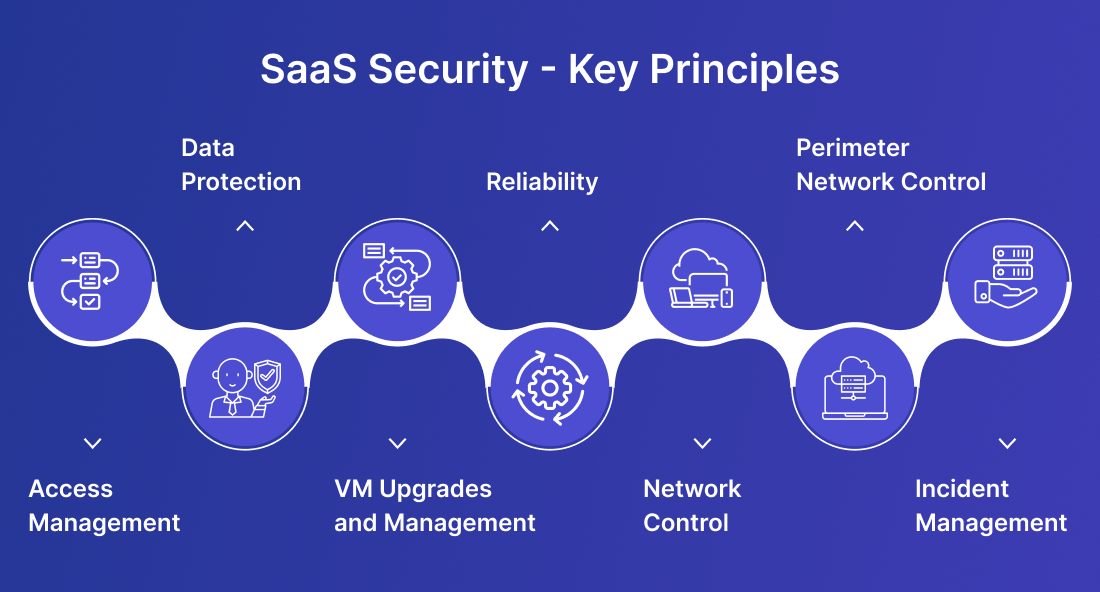
Understanding Saas Security Api Scan Schedules Czaj In this guide, we’ll explore the 10 best practices for api security in saas, explain why they matter, and provide real world strategies to help you secure your platform and customers. Learn how to secure api authentication and authorization in saas apps with oauth 2.0, jwt best practices, and multi layered security strategies. The definitive guide to understanding saas security. learn about saas security including challenges, benefits, and more. This blog explores the essential steps for ensuring your saas platform remains protected by implementing robust api security practices, especially in offshore software development environments.

Saas Security Api Deployment Operations Checklist Pdf The definitive guide to understanding saas security. learn about saas security including challenges, benefits, and more. This blog explores the essential steps for ensuring your saas platform remains protected by implementing robust api security practices, especially in offshore software development environments.
Comments are closed.