Rsa Cipher Initialization Pdf Encryption Computing

Rsa Encryption Pdf Public Key Cryptography Cryptography It is important to note that any message being sent may have the risk of being intercepted by eve, so not only the modulus n, encryption exponent e are known, the ciphertext c may be known to eve as well. Rsa free download as pdf file (.pdf), text file (.txt) or read online for free.

Paper Original Rsa Pdf Public Key Cryptography Computing A popular and fundamental public key cryptography system for safe data transfer is the rsa algorithm. this study examines the rsa encryption and decryption procedures, providing both. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Despite the fact that you are not likely to use rsa for content encryption, it’s nonetheless educational to reflect on how it could be used for that purpose in the form of a block cipher. We are now ready to state the rsa scheme. the ingredients are the following: p,q, two prime numbers (private, chosen).
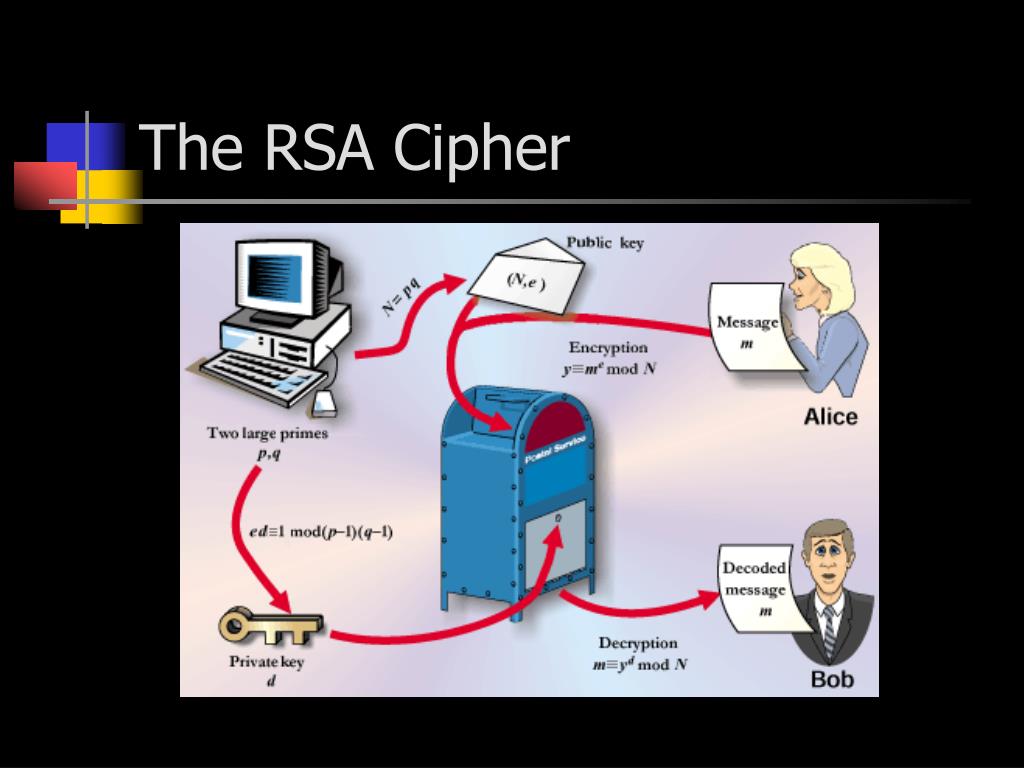
Ppt Rsa Encryption Cryptography Powerpoint Presentation Free Despite the fact that you are not likely to use rsa for content encryption, it’s nonetheless educational to reflect on how it could be used for that purpose in the form of a block cipher. We are now ready to state the rsa scheme. the ingredients are the following: p,q, two prime numbers (private, chosen). To carry out a probabilistic algorithm to find primes and inverses, and to generate the initialization vector in cipher block chaining mode, we need a source of random data, a random number generator. Basics) that asymmetric crypto systems need a reasonably hard problem at the core of preventing easy computation of the private key given the public key . in rsa algorithm, the core problem is just prime factorization. The rsa technique can be used to publicly decide on keys going both ways! it can also be used to establish identity (since the enemy might crack the code, then send something else). The best factorization algorithm known today requires excessively long time (e.g., a month) to factor a large n even on the fastest computer. however, nobody has ever proved that the hypothesis is correct.
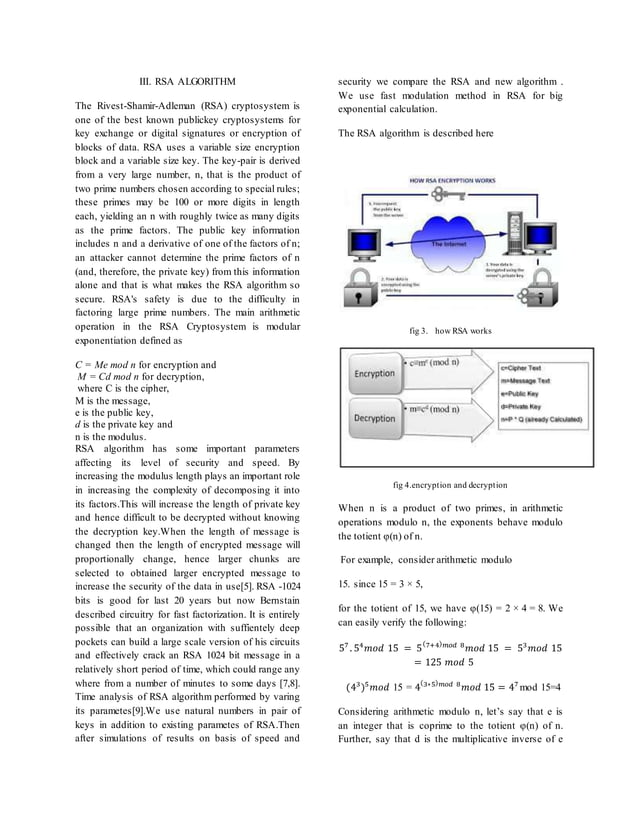
Rsa Encryption Algorithm Cryptography Docx To carry out a probabilistic algorithm to find primes and inverses, and to generate the initialization vector in cipher block chaining mode, we need a source of random data, a random number generator. Basics) that asymmetric crypto systems need a reasonably hard problem at the core of preventing easy computation of the private key given the public key . in rsa algorithm, the core problem is just prime factorization. The rsa technique can be used to publicly decide on keys going both ways! it can also be used to establish identity (since the enemy might crack the code, then send something else). The best factorization algorithm known today requires excessively long time (e.g., a month) to factor a large n even on the fastest computer. however, nobody has ever proved that the hypothesis is correct.

Rsa Public Key Encryption And Signature Lab Pdf Encryption Public The rsa technique can be used to publicly decide on keys going both ways! it can also be used to establish identity (since the enemy might crack the code, then send something else). The best factorization algorithm known today requires excessively long time (e.g., a month) to factor a large n even on the fastest computer. however, nobody has ever proved that the hypothesis is correct.

12 Implementation Of Rsa Algorithm Pdf Public Key Cryptography
Comments are closed.