Rsa Asymmetric Encryption Cryptography Essentials

Asymmetric Key Rsa Pdf Public Key Cryptography Key Cryptography The rsa algorithm is the only asymmetric algorithm that can do asymmetric encryption. This encryption and cryptography essentials course gives aspiring cybersecurity professionals job ready skills in encryption, hashing, and digital signatures—key competencies employers are looking for. you’ll master symmetric (aes) and asymmetric (rsa) encryption techniques and apply hashing methods like md5 and sha to ensure data integrity.
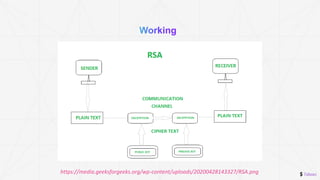
Github Rnlewis Rsa Asymmetric Key Encryption Asymmetric Key Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. Learn the main types of encryption — symmetric (aes) and asymmetric (rsa) — with side by side comparisons, real world use cases, and a decision checklist for it teams. In this handbook, we’ll begin by exploring the foundational principles of the rsa algorithm. by examining its mathematical underpinnings and historical evolution, you will gain insight into the diverse array of attacks that have emerged over the years. Unlike traditional symmetric encryption, which relies on a single shared key, rsa uses a pair of keys: a public key for encryption and a private key for decryption. this asymmetric approach eliminates the need for secure key exchanges, making it a cornerstone of modern cybersecurity.

Asymmetric Key Encryption Rsa Download Scientific Diagram In this handbook, we’ll begin by exploring the foundational principles of the rsa algorithm. by examining its mathematical underpinnings and historical evolution, you will gain insight into the diverse array of attacks that have emerged over the years. Unlike traditional symmetric encryption, which relies on a single shared key, rsa uses a pair of keys: a public key for encryption and a private key for decryption. this asymmetric approach eliminates the need for secure key exchanges, making it a cornerstone of modern cybersecurity. The module covers asymmetric and symmetric cryptography principles, including rsa and elliptic curve cryptography (ecc), with practical exercises in rsa and aes encryption. As the cornerstone of asymmetric cryptography, rsa secures everything from online banking to confidential emails. this article provides a comprehensive exploration of how rsa works, its mathematical foundations, real world applications, and future challenges. Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.

Asymmetric Encryption With Rsa Pptx The module covers asymmetric and symmetric cryptography principles, including rsa and elliptic curve cryptography (ecc), with practical exercises in rsa and aes encryption. As the cornerstone of asymmetric cryptography, rsa secures everything from online banking to confidential emails. this article provides a comprehensive exploration of how rsa works, its mathematical foundations, real world applications, and future challenges. Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.

Asymmetric Encryption With Rsa Pptx Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.
Asymmetric Encryption With Rsa Pptx
Comments are closed.