Roles Permissions

301 Moved Permanently Learn about administrator roles, such as the global administrator role, or the service administrator role. roles map to specific business functions and give permissions to do specific tasks in the microsoft 365 admin center. This page helps you find iam roles and permissions for google cloud services. use the filter to search for roles, permissions, or services by name to get more details about them.
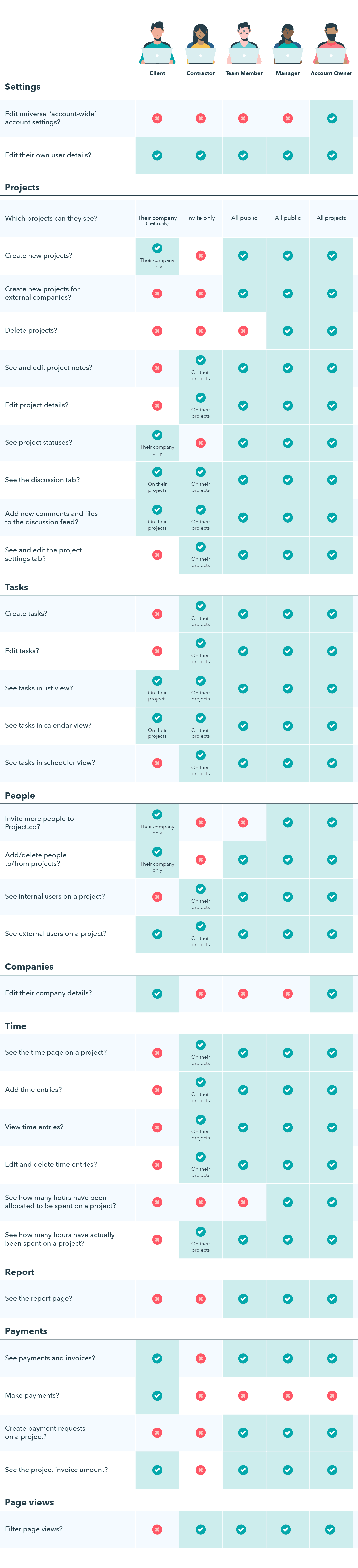
Roles Permissions Project Co Learn Roles & permissions zia agents uses role based access control to manage what users can see and do within the platform. every user is assigned one of four default roles, each with a predefined set of permissions across agents, knowledge base, tools, workflows, billing, and integrations. these roles are not customizable. you cannot create custom roles or modify the permissions assigned to. Microsoft entra id has roles and permissions that are identified as privileged. these roles and permissions can be used to delegate management of directory resources to other users, modify credentials, authentication or authorization policies, or access restricted data. Learn to assign and manage user roles for granular access permissions. control commenting, view assigned users, and simplify privileges for your organization. Roles and permissions combine to form access control. assigning a user the “teacher” role in a school system might grant permissions to view student records and assign grades, while the “student” role only allows viewing personal grades.
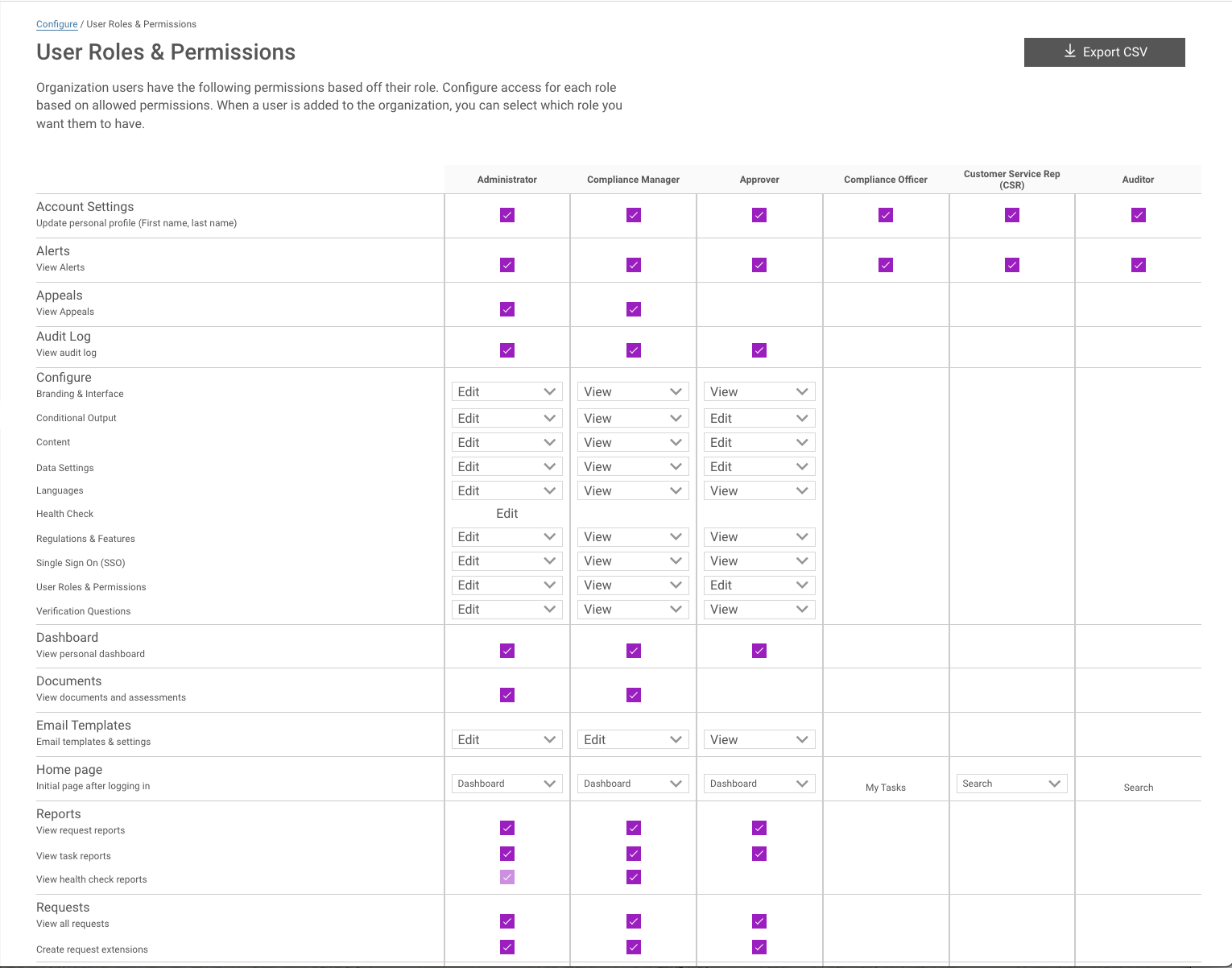
User Roles And Permissions Truyo Releases Learn to assign and manage user roles for granular access permissions. control commenting, view assigned users, and simplify privileges for your organization. Roles and permissions combine to form access control. assigning a user the “teacher” role in a school system might grant permissions to view student records and assign grades, while the “student” role only allows viewing personal grades. Understand user roles & permissions, the foundation of security. learn about rbac, rebac, and see real world examples to implement effective control. Role based access control (rbac) is widely used in organizations to prevent unauthorized access to protected resources. in rbac, we define roles, and each role has a set of permissions. To make sure your custom roles are effective, you can create custom roles based on predefined roles with similar permissions. predefined roles are designed with specific tasks in mind and. For accessing and completing tasks users require specific roles and permissions. review the different available roles, permissions, and the associated tasks that users can complete with the roles and permissions.
Comments are closed.