Role Based Access Control Pdf Systems Engineering Computer Data

Role Based Access Control Pdf Systems Engineering Computer Data It explores the fundamental concepts of rbac, including its core principle of assigning access rights based on organizational roles rather than individual users. the article delves into the. Rating the principles we used in developing it; we give complete speci ̄cation of hierarchical rbac, with an ad ditional option for managing the relationship on roles; we describe a speci ̄cation of constrained rbac, maki.

Pdf Role Based Access Control 9781580533249 Roles with different privileges and responsibilities are a central feature of most organizations, and some computer applications dating back to at least the 1970s had limited forms of access control based on the user’s role in an organization. The paper describes a type of non discretionary access control role based access control (rbac) that is more central to the secure processing needs of non military systems than dac. Abstract role engineering is the process of designing an rbac system. a promising approach to role engineering is role mining, which uses data mining techniques to find an rbac system from existing per mission assignment data. To enable system integrators to integrate rbac into the various it infrastructures found in an enterprise like web applications, such as java and federated database systems, the book provides an analysis of research ideas and prototypes built so far.
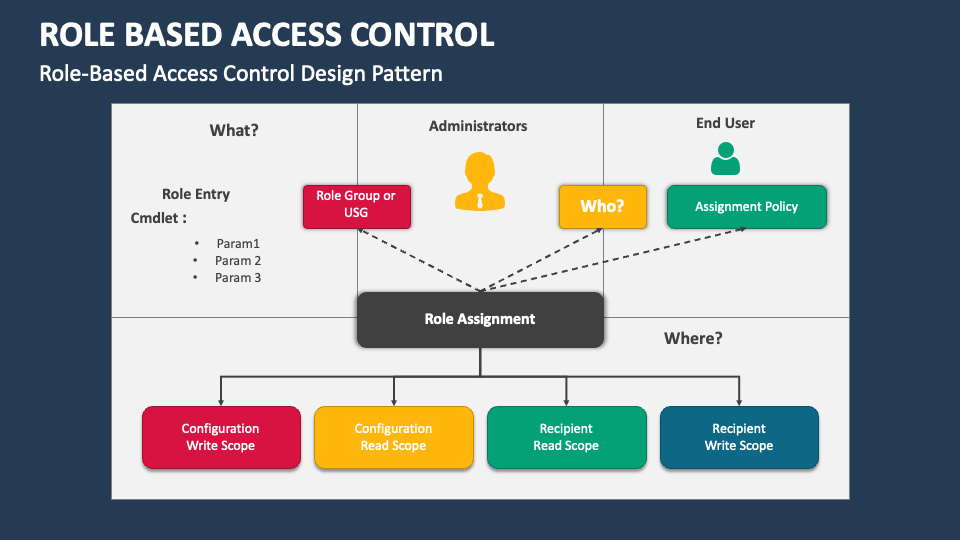
Role Based Access Control Powerpoint And Google Slides Template Ppt Abstract role engineering is the process of designing an rbac system. a promising approach to role engineering is role mining, which uses data mining techniques to find an rbac system from existing per mission assignment data. To enable system integrators to integrate rbac into the various it infrastructures found in an enterprise like web applications, such as java and federated database systems, the book provides an analysis of research ideas and prototypes built so far. This paper aims to review the computational results of employing rbac to enhance the security features and reduce the level of administrative cost, as well as weigh the advantages and disadvantages of this resource access management system. Unlike access control policies that assign permissions to subjects, rbac associates permissions with functions jobs roles within an organization. a role is a collection of job functions. roles within a bank might include: president, manager, trainer, teller, auditor, janitor, etc. Role based access control(rbac) provides more efficiency in access control than traditional access control. a reference model is presenting the basic concept policies and behaviors of role based access control. One of the most used ac paradigms is role based access control (rbac), in which access rights are determined based on the user’s role. many different types of rbac policies have been proposed in the literature, each one accompanied by the corresponding extension of the original rbac model.
Comments are closed.