Role Based Access Control For Creators Guide

Dashboard Role Based Access Control Guide Pdf Public Key Discover how role based access control (rbac) enhances content security, streamlines management, and protects your creative work. Master rbac implementation with comprehensive examples, diagrams, and best practices for secure access control in modern operating systems and applications.

Role Based Access Control For Creators Guide Learn what rbac is, how it works, and why it’s vital for cybersecurity. discover rbac models and best practices for secure access control. What is role based access control? learn more about rbac, including definitions, principles, and best practices. Learn how rbac strengthens security, ensures compliance, and simplifies access management in this practical design and implementation guide. Below is a practical, build ready way to design and implement role based access control (rbac) in your product. you will get a simple data model, concrete examples, and the common failure points that cause security incidents.
Github Sumaya110 Role Based Access Control Learn how rbac strengthens security, ensures compliance, and simplifies access management in this practical design and implementation guide. Below is a practical, build ready way to design and implement role based access control (rbac) in your product. you will get a simple data model, concrete examples, and the common failure points that cause security incidents. Introduction role based access control (rbac) is widely used in organizations to prevent unauthorized access to protected resources. in rbac, we define roles, and each role has a set of permissions. One of the most widely used and practical models for this purpose is rbac — role based access control. the core idea behind rbac is simple: permissions are assigned to roles, and users gain. How to design an rbac (role based access control) system detailed explanation of rbac system's core concepts, design patterns, and implementation methods, with nocobase practical cases to help you build a secure and efficient permission system. This article provides a comprehensive overview of role based access control (rbac) along with a guided approach to implementing, maintaining, and extending rbac to suit the needs of your organization.
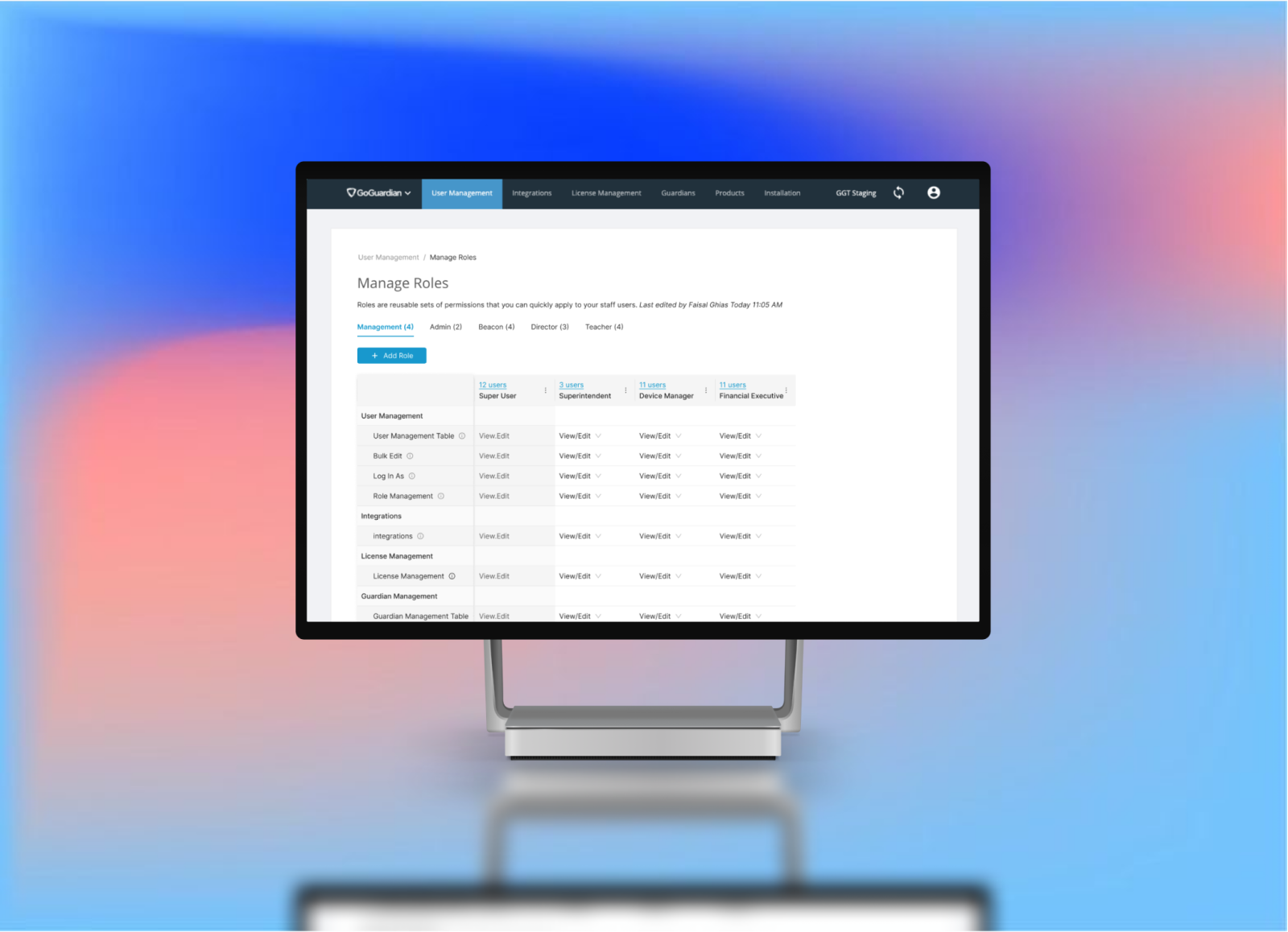
Role Based Access Control By Yoonah Bae On Dribbble Introduction role based access control (rbac) is widely used in organizations to prevent unauthorized access to protected resources. in rbac, we define roles, and each role has a set of permissions. One of the most widely used and practical models for this purpose is rbac — role based access control. the core idea behind rbac is simple: permissions are assigned to roles, and users gain. How to design an rbac (role based access control) system detailed explanation of rbac system's core concepts, design patterns, and implementation methods, with nocobase practical cases to help you build a secure and efficient permission system. This article provides a comprehensive overview of role based access control (rbac) along with a guided approach to implementing, maintaining, and extending rbac to suit the needs of your organization.
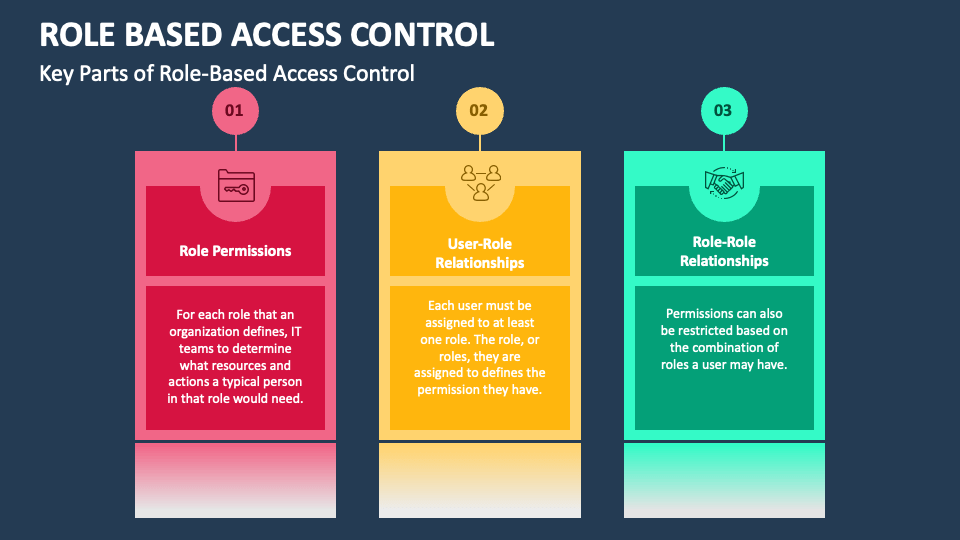
Role Based Access Control Powerpoint And Google Slides Template Ppt How to design an rbac (role based access control) system detailed explanation of rbac system's core concepts, design patterns, and implementation methods, with nocobase practical cases to help you build a secure and efficient permission system. This article provides a comprehensive overview of role based access control (rbac) along with a guided approach to implementing, maintaining, and extending rbac to suit the needs of your organization.
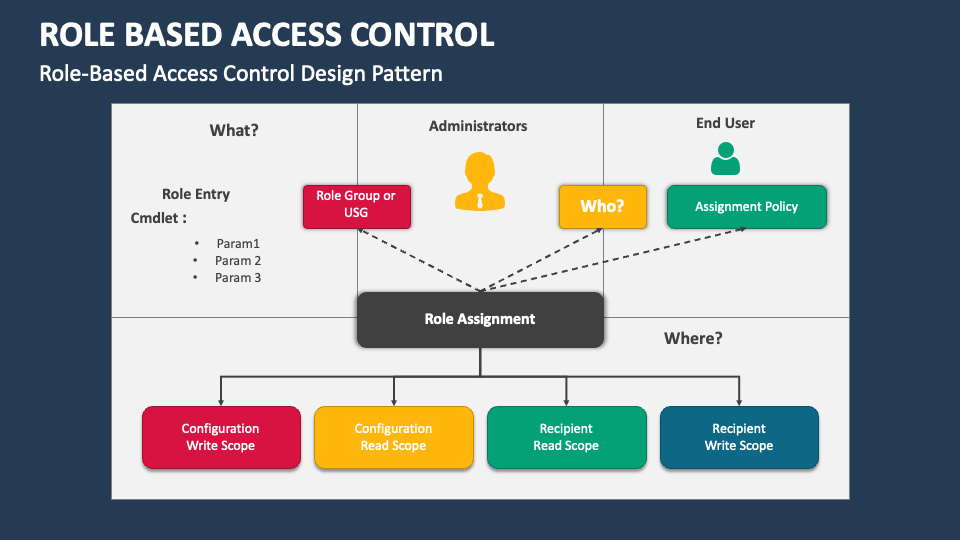
Role Based Access Control Powerpoint And Google Slides Template Ppt
Comments are closed.