Role Based Access Control Erd Darwin Biler

Erd Access Role Pdf Role based access control (rbac) is an approach of restricting access to authorized users. the primary goal of this approach is making it easy to change and group permissions without going through all the users and adding it one by one. How to design an rbac (role based access control) system detailed explanation of rbac system's core concepts, design patterns, and implementation methods, with nocobase practical cases to help you build a secure and efficient permission system.
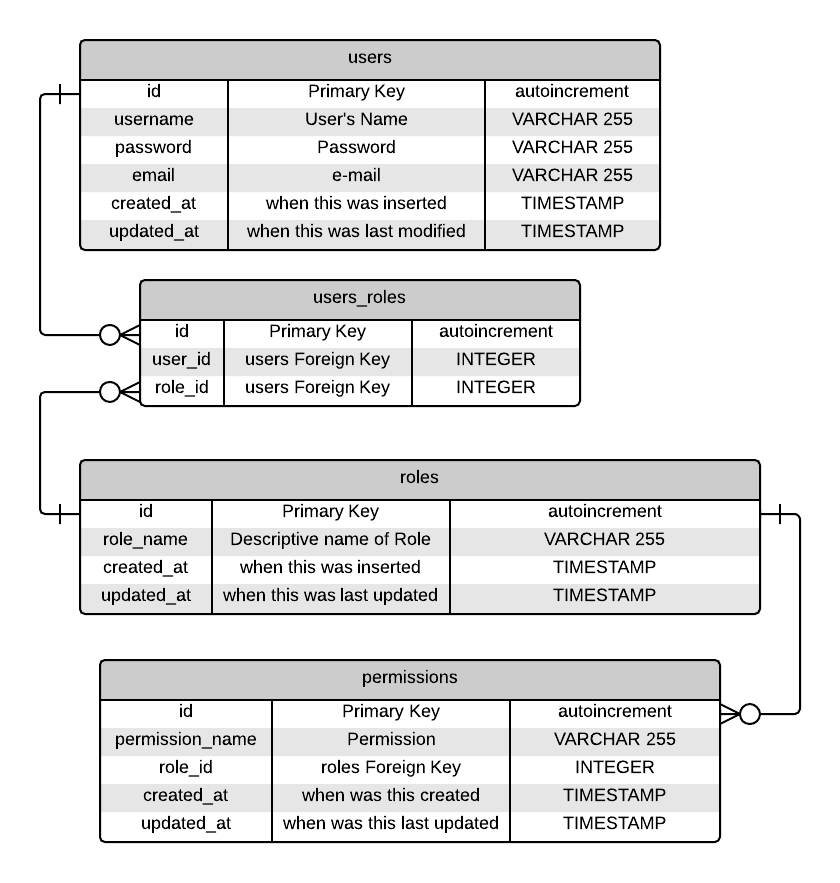
Role Based Access Control Erd Darwin Biler You are assuming that it must be necessary to "identify which role to use" for the user, but (1) it isn't absolutely necessary and (2) that (which role am i going to play) can be a piece of information that the user is required to enter during logon and then stored in his session context. In any modern application, access control is a fundamental security requirement. a well designed role based access control (rbac) system ensures that users have the appropriate. When a user logs in the system, he she establishes a session and, during this session, can request to activate a subset of the roles he she is authorized to play. This guide will demystify role based access control (rbac) with concrete examples and practical pseudocode to help you bridge the gap from theory to implementation.
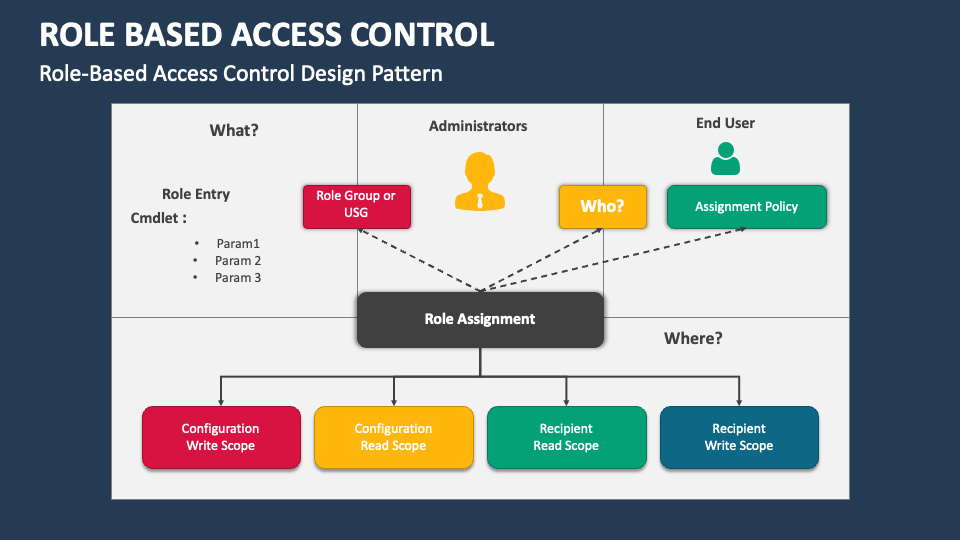
Role Based Access Control Powerpoint And Google Slides Template Ppt When a user logs in the system, he she establishes a session and, during this session, can request to activate a subset of the roles he she is authorized to play. This guide will demystify role based access control (rbac) with concrete examples and practical pseudocode to help you bridge the gap from theory to implementation. Rbac (role based access control): is an access control method where users are given roles and the roles determine what privileges they have. operational privileges are grouped into roles and each user is assigned a role. the role, instead of the individual, is the basis of access checks. This study investigates the effectiveness of role based access control (rbac) systems in mitigating insider threats to database security within various organizational environments. Explore practical examples of role based access control (rbac) to streamline security management and ensure appropriate access to sensitive data. learn how to implement rbac effectively for improved organisational safety. Master rbac implementation with comprehensive examples, diagrams, and best practices for secure access control in modern operating systems and applications.
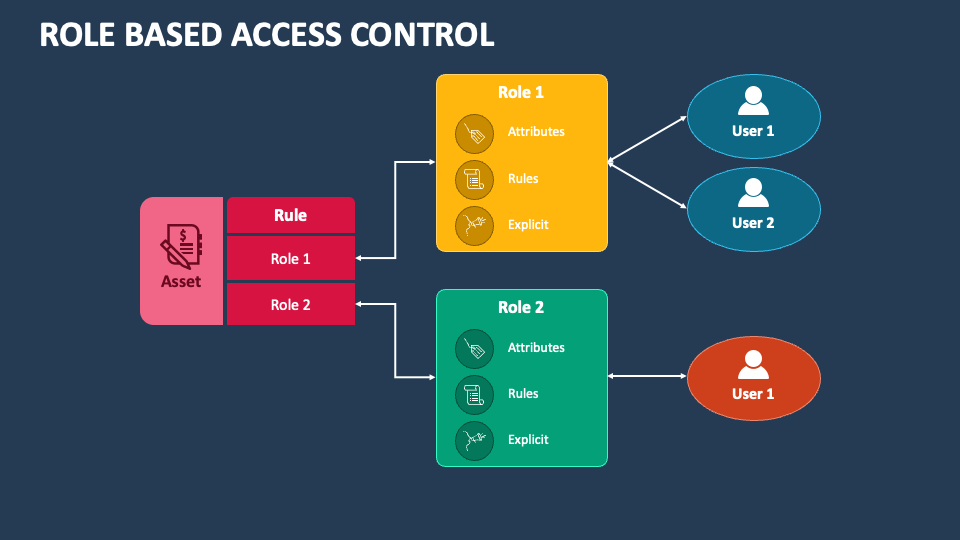
Role Based Access Control Powerpoint And Google Slides Template Ppt Rbac (role based access control): is an access control method where users are given roles and the roles determine what privileges they have. operational privileges are grouped into roles and each user is assigned a role. the role, instead of the individual, is the basis of access checks. This study investigates the effectiveness of role based access control (rbac) systems in mitigating insider threats to database security within various organizational environments. Explore practical examples of role based access control (rbac) to streamline security management and ensure appropriate access to sensitive data. learn how to implement rbac effectively for improved organisational safety. Master rbac implementation with comprehensive examples, diagrams, and best practices for secure access control in modern operating systems and applications.
Comments are closed.