Role Based Access Control A Guide For Security Professionals

Dashboard Role Based Access Control Guide Pdf Public Key Unlock your understanding of role based access control: a guide for security professionals. arm yourself with key insights to bolster your security strategy today. Learn how rbac strengthens security, ensures compliance, and simplifies access management in this practical design and implementation guide.

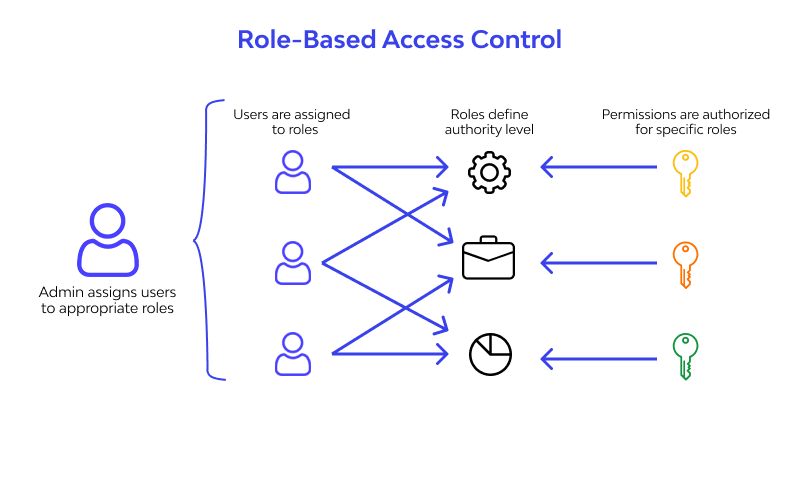
Role Based Access Control A Practical Guide Discover the power of role based access control (rbac) and enhance your organization's security. explore rbac solutions with searchinform for robust access management. Learn how role based access control boosts security, ensures compliance, and scales access management for modern enterprises. discover key benefits and strategies. Learn what rbac is, how it works, and why it’s vital for cybersecurity. discover rbac models and best practices for secure access control. Rbac, meaning role based access control, is a widely used access control model for security that restricts access and authorization to systems based on employees’ roles and responsibilities within the organization.

Role Based Access Control A Guide For Security Professionals Learn what rbac is, how it works, and why it’s vital for cybersecurity. discover rbac models and best practices for secure access control. Rbac, meaning role based access control, is a widely used access control model for security that restricts access and authorization to systems based on employees’ roles and responsibilities within the organization. Rbac has evolved from a basic it practice into a strategic necessity powering secure, compliant, and efficient digital ecosystems. here’s a complete breakdown of why rbac matters, how it works. This article provides a comprehensive overview of role based access control (rbac) along with a guided approach to implementing, maintaining, and extending rbac to suit the needs of your organization. Learn what rbac is, how it works, and best practices for implementation. enhance security and access management today. In today's distributed, cloud first world, role based access control (rbac) has evolved from a convenient administrative tool to a critical security control within zero trust architectures.

Role Based Access Control A Guide For Security Professionals Rbac has evolved from a basic it practice into a strategic necessity powering secure, compliant, and efficient digital ecosystems. here’s a complete breakdown of why rbac matters, how it works. This article provides a comprehensive overview of role based access control (rbac) along with a guided approach to implementing, maintaining, and extending rbac to suit the needs of your organization. Learn what rbac is, how it works, and best practices for implementation. enhance security and access management today. In today's distributed, cloud first world, role based access control (rbac) has evolved from a convenient administrative tool to a critical security control within zero trust architectures.
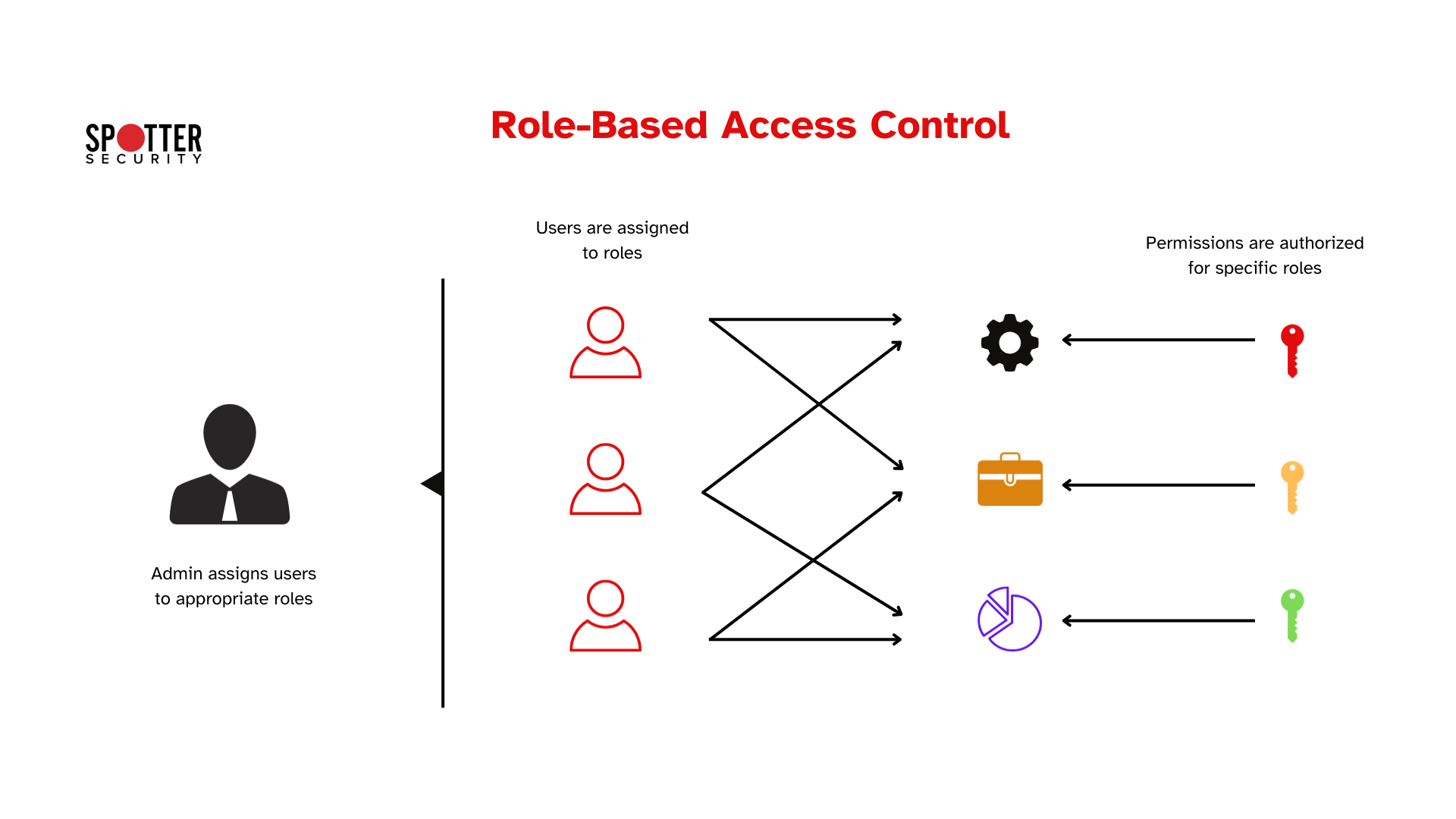
What Is Role Based Access Control Rbac Spotter Security Learn what rbac is, how it works, and best practices for implementation. enhance security and access management today. In today's distributed, cloud first world, role based access control (rbac) has evolved from a convenient administrative tool to a critical security control within zero trust architectures.
Guide To Role Based Access Control Rbac With Sap Security
Comments are closed.