Rmf Step Implement Tasks And Publications Course Hero

Rmf Introductory Course V2 Download Pdf This course is provided by the national institute of standards and technology and is available free of charge at nist.gov rmf rmf step: implement supporting publications 87 the following nist publications support this step: • nist sp 800 128, guide for security focused configuration management of information systems • nist sp 800 34. In this lesson, you will learn the defining aspects of the implement step, and the associated policies and guidelines.

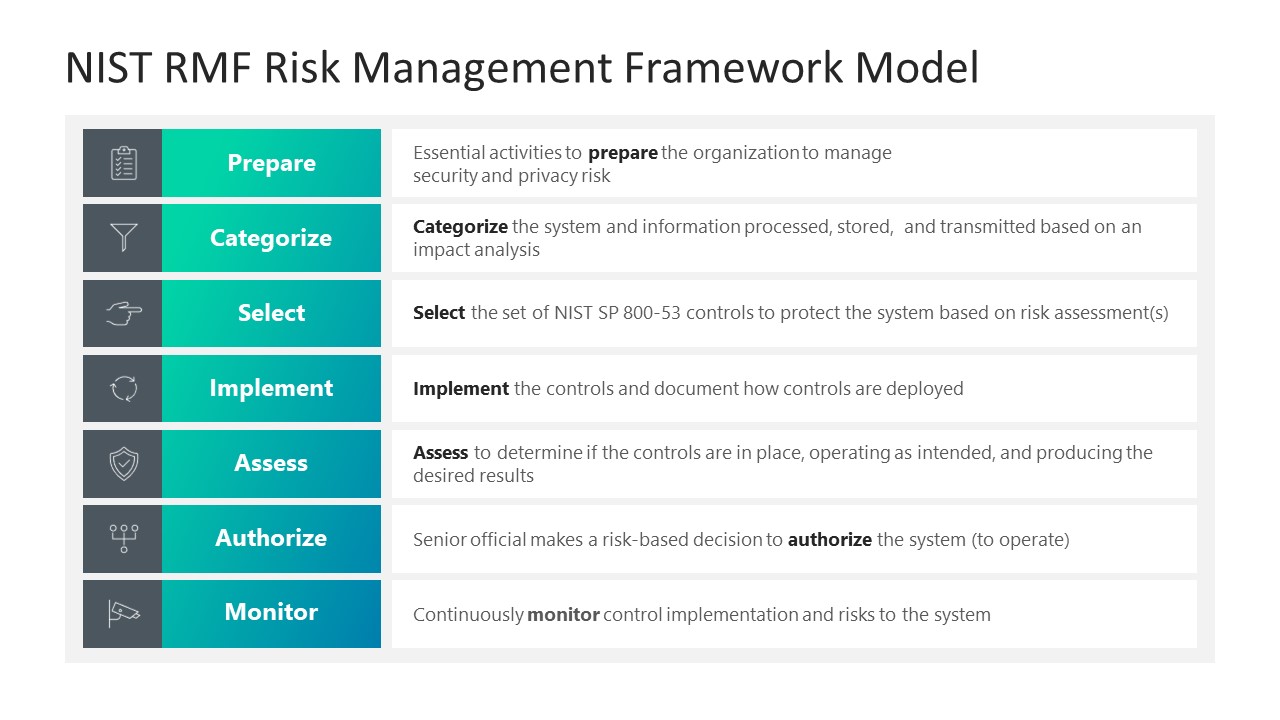
Fyt Task 1 Rmf To Do List Ctnsrpf 4 Version2 Rmf To Do List Rmf Tasks Guidelines on establishing an effective incident response program, and detecting, analyzing, prioritizing, and handling incidents. Nist's risk management framework or rmf there are seven steps in the rmf: prepare, categorize, select, implement, assess, authorize, and monitor. 1 prepare refers to activities that are necessary to manage security and privacy risks before a breach occurs. Task 6.7 information system removal and decommissioning (sdlc disposal) implement an information system decommissioning strategy, when needed, which executes required actions when a system is removed from service. All seven steps are essential for the successful execution of the rmf. the steps are: • prepare to execute the rmf from an organization level and a system level perspective by establishing a context and priorities for managing security and privacy risk.

Rmf Web Programming Multiple Robots With Ros 2 Task 6.7 information system removal and decommissioning (sdlc disposal) implement an information system decommissioning strategy, when needed, which executes required actions when a system is removed from service. All seven steps are essential for the successful execution of the rmf. the steps are: • prepare to execute the rmf from an organization level and a system level perspective by establishing a context and priorities for managing security and privacy risk. I can provide you with a general outline of the steps and their typical deliverables, but for accurate and up to date information, you should refer to the relevant nist special publications or authoritative sources on the topic. The roles and responsibilities charts summarize the major roles involved in the risk management framework as they pertain to each step in the framework. the quick start guides are designed to provide an introduction to the nist materials that support each step in the risk management framework. Individual tasks within each step of the risk management framework, and their associated outcomes learn with flashcards, games, and more — for free. What is the implement step? the purpose of the implement step is to carry out the controls in the security and privacy plans for the system and for the organization and to document in a baseline configuration, the specific details of a control implementation.
Rmf Ssp Template Astra Edu Pl I can provide you with a general outline of the steps and their typical deliverables, but for accurate and up to date information, you should refer to the relevant nist special publications or authoritative sources on the topic. The roles and responsibilities charts summarize the major roles involved in the risk management framework as they pertain to each step in the framework. the quick start guides are designed to provide an introduction to the nist materials that support each step in the risk management framework. Individual tasks within each step of the risk management framework, and their associated outcomes learn with flashcards, games, and more — for free. What is the implement step? the purpose of the implement step is to carry out the controls in the security and privacy plans for the system and for the organization and to document in a baseline configuration, the specific details of a control implementation.
Comments are closed.