Risk Prioritization Improving Network Vulnerability Security

Enhancing Vulnerability Prioritization Pdf Vulnerability Computing Without prioritization, security teams risk wasting time patching low risk flaws while missing critical exposures that attackers could exploit. if done well, prioritization enables smarter resource allocation, faster response to urgent threats and better alignment with compliance and business goals. Learn how to effectively prioritize vulnerabilities to enhance security, reduce risks, and focus on the most critical threats.

Risk Prioritization Improving Network Vulnerability Security Staying proactive with vulnerability prioritization is essential for any organization to effectively manage and mitigate cybersecurity risks. here are some key steps and strategies to help you prioritize vulnerabilities proactively:. What is vulnerability prioritization? vulnerability prioritization is the process of evaluating and ranking discovered security vulnerabilities based on the actual risk they pose to your specific environment, so your team fixes the issues most likely to result in a breach first. Learn how to prioritize vulnerabilities by risk, exploitability, and business impact. see how security teams reduce noise and improve remediation speed. Learn essential strategies and expert tips for effective vulnerability prioritization, ensuring your cybersecurity posture is resilient.
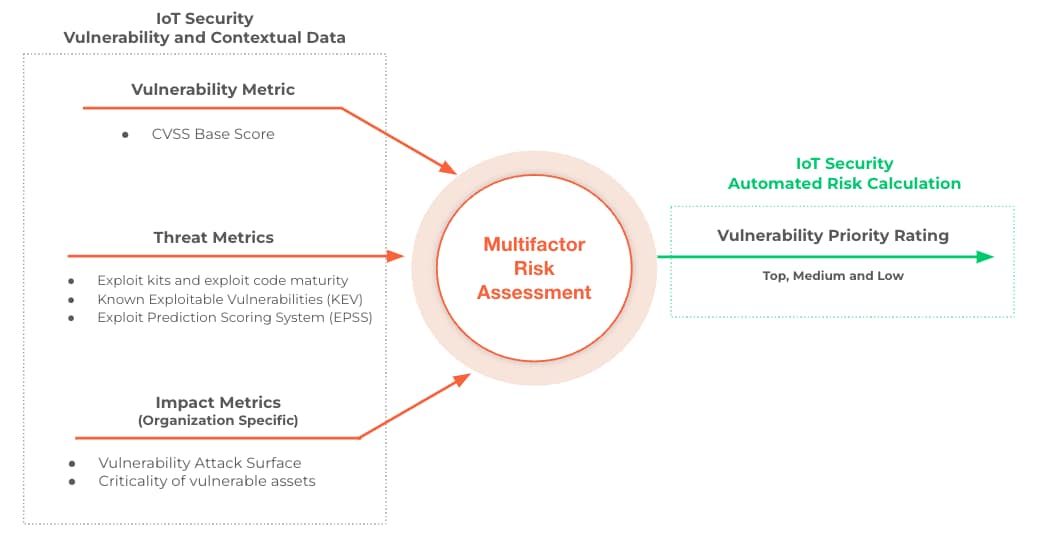
Risk Based Vulnerability Prioritization For Iot Ot And Miot Devices Learn how to prioritize vulnerabilities by risk, exploitability, and business impact. see how security teams reduce noise and improve remediation speed. Learn essential strategies and expert tips for effective vulnerability prioritization, ensuring your cybersecurity posture is resilient. Existing solutions struggle to efficiently patch thousands of vulnerabilities on a network. this article presents illation, a proof of concept model that provides network specific vulnerability risk prioritization to support efficient patching. What does successful vulnerability prioritization look like? it looks like fewer tickets, faster patching where it matters, better alignment with business priorities, and reduced exposure to exploited vulnerabilities—all with clear reporting and defensible decision making. Vulnerability prioritization frameworks are essential for maintaining robust cybersecurity. by adopting a risk based approach and leveraging automation tools, organizations can significantly enhance their security posture. With the application of asset criticality and effectiveness of security controls, organizations can properly calculate their vulnerability risk and properly prioritize and plan vulnerability remediation.
Comments are closed.