Risk Management Under The Hipaa Security Rule

Hipaa Security Rule And Risk Management The tool’s features make it useful in assisting small and medium sized health care practices and business associates in complying with the health insurance portability and accountability act (hipaa) security rule. Download pdfs of the hipaa toolkit, faqs and other resources to understand the hipaa rule requiring physicians to protect patients' electronic health information, ensuring its confidentiality and security.

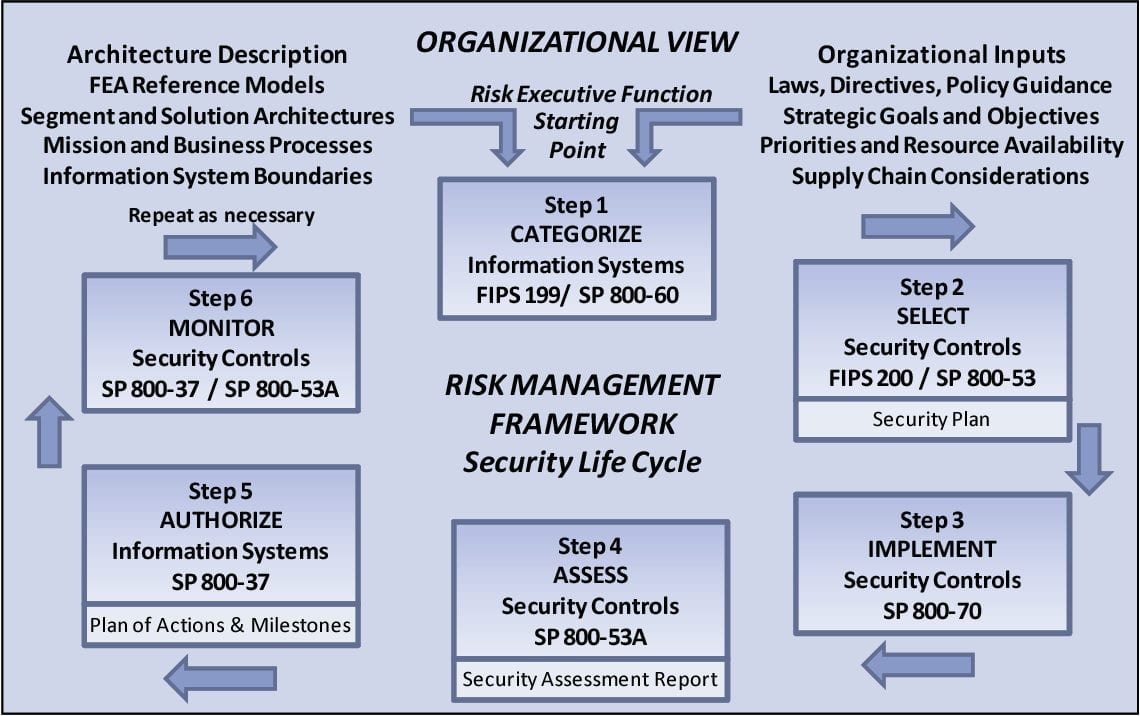
Hipaa Security Rule Risk Analysis Spider Networks A risk analysis is one of four required implementation specifications under the security management process of the administrative safeguards, the others being risk management, sanction policy, and information system activity review. This series of guidances will assist organizations2 in identifying and implementing the most effective and appropriate administrative, physical, and technical safeguards to secure electronic protected health information (e phi). Learn how to conduct a hipaa risk assessment that satisfies security rule requirements. step by step guidance for covered entities and business associates. This publication provides practical guidance and resources that can be used by regulated entities of all sizes to safeguard ephi and better understand the security concepts discussed in the hipaa security rule.

Hipaa Security Rule Explained With Key Requirements Learn how to conduct a hipaa risk assessment that satisfies security rule requirements. step by step guidance for covered entities and business associates. This publication provides practical guidance and resources that can be used by regulated entities of all sizes to safeguard ephi and better understand the security concepts discussed in the hipaa security rule. Run a hipaa risk analysis to map ephi scope, find threats, assess controls, and prioritize fixes to lower breach risk and demonstrate security rule compliance. The hhs’ office for civil rights has released a video presentation explaining the risk management requirements of the hipaa security rule, as it expands its enforcement initiative to cover risk management. Effective risk management is an essential component of both hipaa security rule compliance and broader cybersecurity preparedness. Learn how to develop and implement a hipaa compliant risk management plan. follow three essential steps: evaluate risks, implement security measures, and maintain ongoing monitoring per security rule requirements.
Hipaa Security Rule Importance And Safeguard Run a hipaa risk analysis to map ephi scope, find threats, assess controls, and prioritize fixes to lower breach risk and demonstrate security rule compliance. The hhs’ office for civil rights has released a video presentation explaining the risk management requirements of the hipaa security rule, as it expands its enforcement initiative to cover risk management. Effective risk management is an essential component of both hipaa security rule compliance and broader cybersecurity preparedness. Learn how to develop and implement a hipaa compliant risk management plan. follow three essential steps: evaluate risks, implement security measures, and maintain ongoing monitoring per security rule requirements.

Understanding Hipaa Security Rule Requirements Effective risk management is an essential component of both hipaa security rule compliance and broader cybersecurity preparedness. Learn how to develop and implement a hipaa compliant risk management plan. follow three essential steps: evaluate risks, implement security measures, and maintain ongoing monitoring per security rule requirements.
Hipaa Risk Management Plan Security Rule Plans Db Excel
Comments are closed.