Risk Based Vulnerability Management Pdf

Risk Based Vulnerability Management Pdf As we’ve seen, vulnerability management isn’t just an aspect of it hygiene, but an essential part of it risk and compliance management, and key to establishing and maintaining trust in it services. Using a risk based approach to remediating vulnerabilities is revolutionizing the way organizations traditionally approach vulnerability management with an all or nothing strategy of remediation.

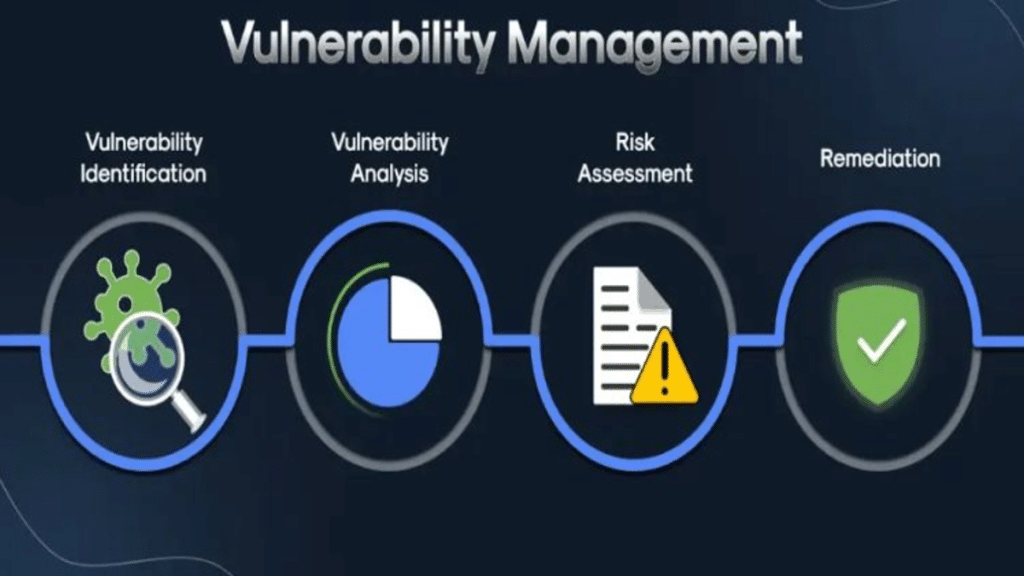
Vulnerability Management Pdf Vulnerability Computing Security Risk based vulnerability management offers a smarter approach to protecting the business based on machine learning–generated risk models. this approach assesses vulnerabilities in the context of business risk. Vulnerability management is a key component in planning for and determining the appropriate implementation of controls and the management of risk. it is reasonable to say that vulnerability management is central to cyber resilience. This guide proposes a more effective risk based vulnerability management (rbvm) approach. businesses can maximize their security investments by prioritizing vulnerabilities according to their likelihood of being exploited and potential damage. Introduction & prework vulnerability management (“vm”) is a proactive method of enterprise security, and this whitepaper provides a structured approach to vm’s best practices.

What Is Business Risk Oriented Vulnerability Management This guide proposes a more effective risk based vulnerability management (rbvm) approach. businesses can maximize their security investments by prioritizing vulnerabilities according to their likelihood of being exploited and potential damage. Introduction & prework vulnerability management (“vm”) is a proactive method of enterprise security, and this whitepaper provides a structured approach to vm’s best practices. This paper explores a comprehensive vulnerability management framework that organizations can utilize as a starting point to build their programs, ensuring robust security and resilience against emerging threats. As a de facto industry standard, vulnerabilities are risk rated by level of severity, along with the general time period by which they need to be patched. the risk rating scheme (critical, high, medium, low) discussed above in table 1 is determined using risk scores. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. Risk based vulnerability management: modern vulnerability management: predictive cybersecurity michael roytman,ed bellis,2023 03 31 this book comprehensively covers the principles of risk based vulnerability management rbvm one of the most challenging tasks in cybersecurity from the foundational mathematical models to building your own decision.

Risk Based Vulnerability Management Frogman This paper explores a comprehensive vulnerability management framework that organizations can utilize as a starting point to build their programs, ensuring robust security and resilience against emerging threats. As a de facto industry standard, vulnerabilities are risk rated by level of severity, along with the general time period by which they need to be patched. the risk rating scheme (critical, high, medium, low) discussed above in table 1 is determined using risk scores. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. Risk based vulnerability management: modern vulnerability management: predictive cybersecurity michael roytman,ed bellis,2023 03 31 this book comprehensively covers the principles of risk based vulnerability management rbvm one of the most challenging tasks in cybersecurity from the foundational mathematical models to building your own decision.

Risk Based Vulnerability Management Rbvm Seconize This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program. Risk based vulnerability management: modern vulnerability management: predictive cybersecurity michael roytman,ed bellis,2023 03 31 this book comprehensively covers the principles of risk based vulnerability management rbvm one of the most challenging tasks in cybersecurity from the foundational mathematical models to building your own decision.
Demystifying Risk Based Vulnerability Management
Comments are closed.