Risk Based Authentication Transaction
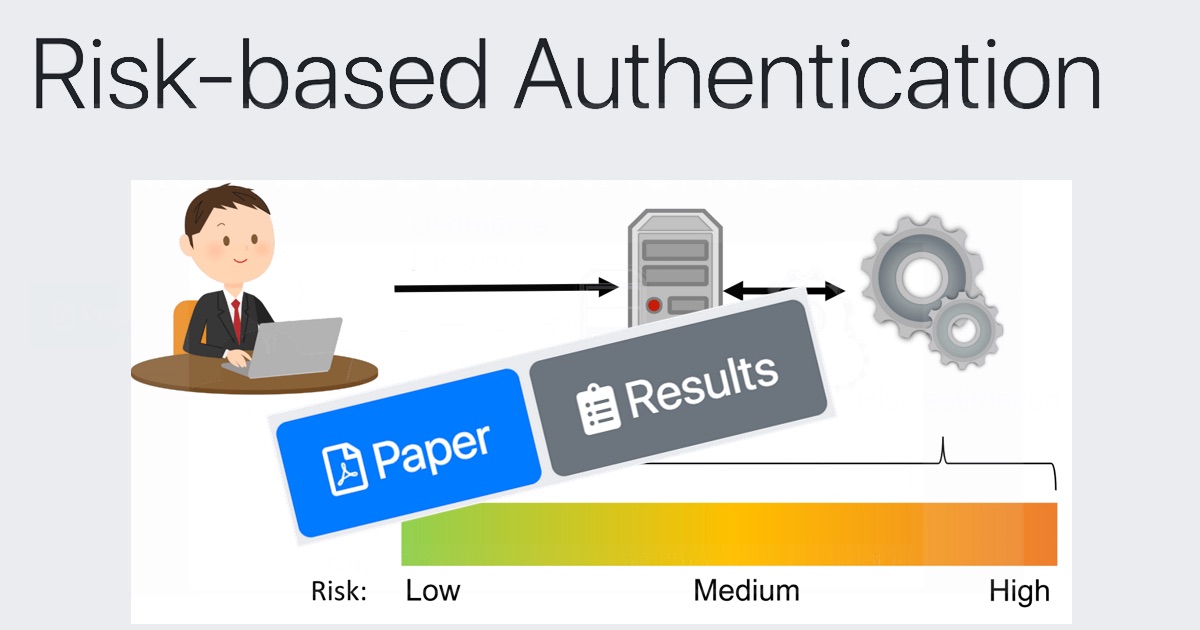
Risk Based Authentication Improves Password Security Without Risk based authentication helps keep transactions secure without introducing delays into the user experience. protection of both user and platform from fraud: higher risk transactions are challenged or blocked, reducing the risk of fraud for both the platform and potential victims. Risk based authentication (rba) extends authentication mechanisms to make them more robust against account takeover attacks, such as those using stolen passwords.
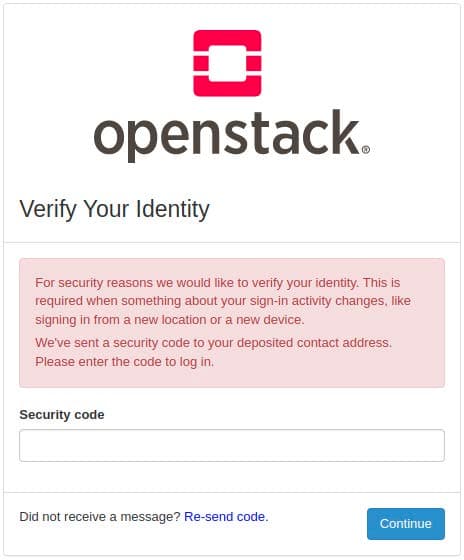
Open Source Risk Based Authentication In a risk based authentication system, the institution decides if additional authentication is necessary. if the risk is deemed appropriate, enhanced authentication will be triggered, such as a one time password delivered via an out of band communication. Risk based authentication is controlled by sets of rules, also known as policies, that categorize how risky a specific transaction is. every time a request is received, these policies analyze the various risk signals and weigh them against each other to calculate a risk score. Risk based authentication (rba) is an authentication method in which varying levels of stringency are applied to a system's authentication process based on the likelihood that access to that system could result in its compromise. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience.
Rba Risk Based Authentication Github Risk based authentication (rba) is an authentication method in which varying levels of stringency are applied to a system's authentication process based on the likelihood that access to that system could result in its compromise. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience. To mitigate these complex, conflicting challenges, organizations are adopting various forms of rba. this method of dynamic authentication assesses the level of risk associated with a user's access request and adjusts the authentication requirements in real time. Learn risk based authentication strategies and best practices to strengthen identity security, reduce fraud, and improve user experience. Risk based authentication proves a verified person is accessing an account, but adapts login requirements using signals like device, location, and ip address. this also includes transaction amounts for banks and financial institutions. Risk based authentication (rba) is a dynamic security approach that adapts the authentication process based on the perceived risk level of a user’s login attempt or transaction.
Cover To mitigate these complex, conflicting challenges, organizations are adopting various forms of rba. this method of dynamic authentication assesses the level of risk associated with a user's access request and adjusts the authentication requirements in real time. Learn risk based authentication strategies and best practices to strengthen identity security, reduce fraud, and improve user experience. Risk based authentication proves a verified person is accessing an account, but adapts login requirements using signals like device, location, and ip address. this also includes transaction amounts for banks and financial institutions. Risk based authentication (rba) is a dynamic security approach that adapts the authentication process based on the perceived risk level of a user’s login attempt or transaction.
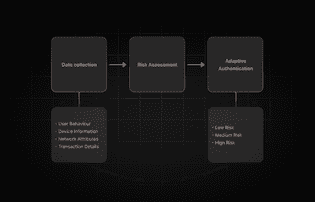
Data Collection Risk based authentication proves a verified person is accessing an account, but adapts login requirements using signals like device, location, and ip address. this also includes transaction amounts for banks and financial institutions. Risk based authentication (rba) is a dynamic security approach that adapts the authentication process based on the perceived risk level of a user’s login attempt or transaction.
Comments are closed.