Risk Based Authentication
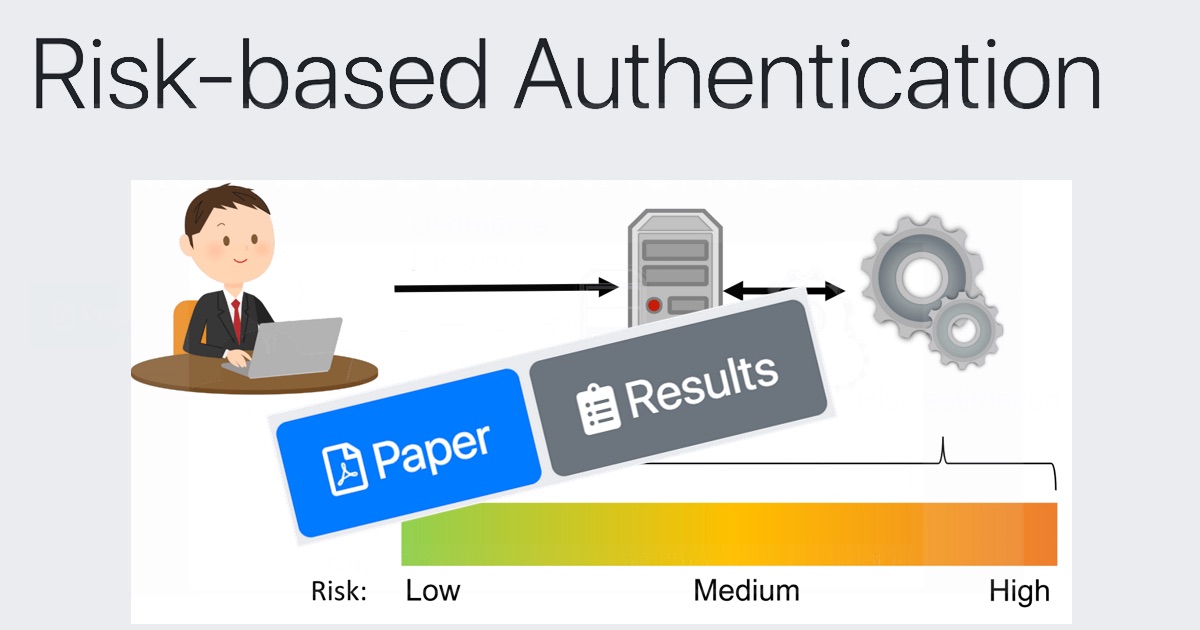
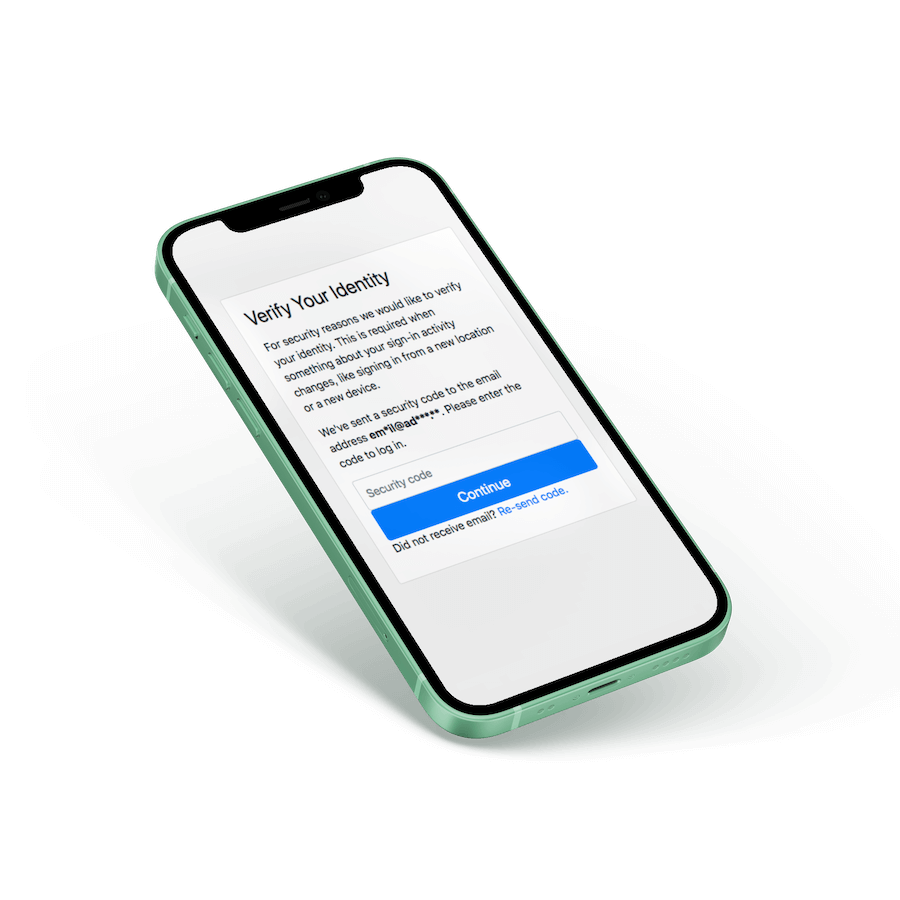
Risk Based Authentication Improves Password Security Without During login, rba estimates a risk score based on the login behavior. on a low risk (e.g. same device as always), access to the website is granted. on a medium risk (e.g. unknown device), the website asks for additional information to confirm the claimed identity (e.g. confirmation of email address). on a high risk, access is denied. who uses rba?. What is risk based authentication (rba)? risk based authentication (rba) is an authentication method in which varying levels of stringency are applied to a system's authentication process based on the likelihood that access to that system could result in its compromise.
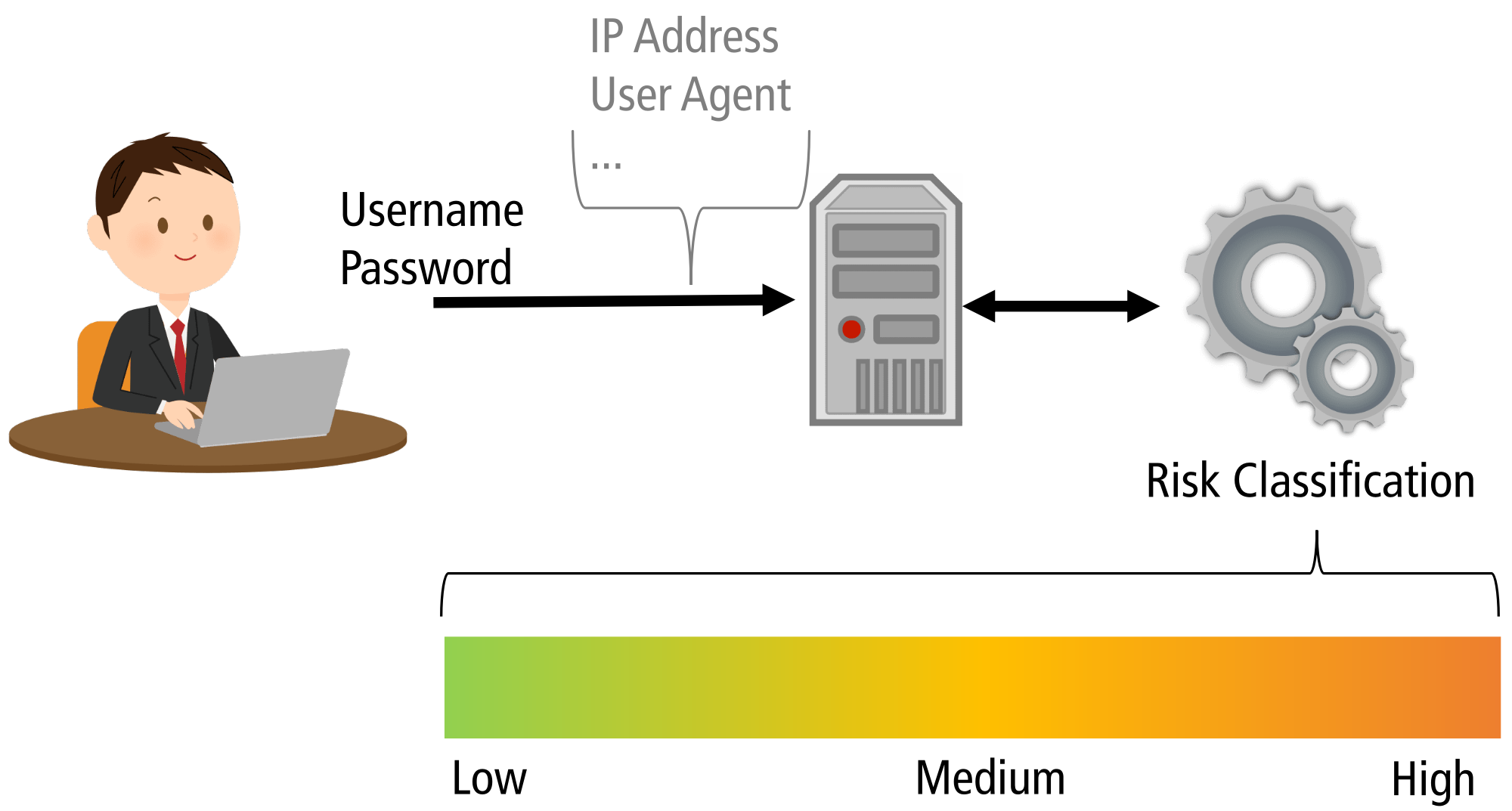
Media Risk Based Authentication Learn about risk based authentication, a non static system that adapts the challenge complexity to the risk profile of the user. find out how it works, its benefits, its criticism and its examples. Risk based authentication (rba) extends authentication mechanisms to make them more robust against account takeover attacks, such as those using stolen passwords. What is risk based authentication? risk based authentication helps prevent fraud, insider threats, and other attacks by comparing the actions of users to a baseline of normal activity. What is risk based authentication (rba)? risk based authentication proves that a verified user is accessing an account, adapting how that proof is requested based on context. it analyzes factors like device, location, and network to determine if a login attempt looks typical or suspicious.
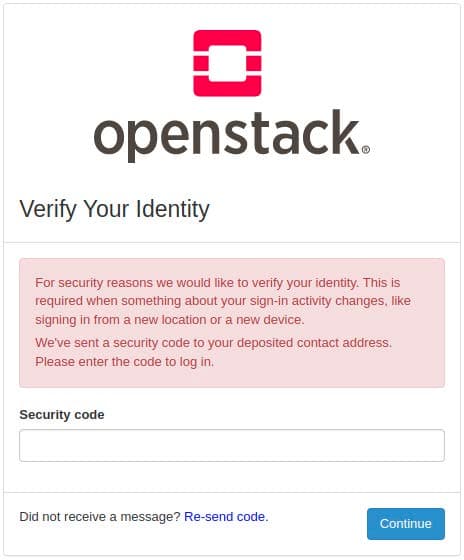
Open Source Risk Based Authentication What is risk based authentication? risk based authentication helps prevent fraud, insider threats, and other attacks by comparing the actions of users to a baseline of normal activity. What is risk based authentication (rba)? risk based authentication proves that a verified user is accessing an account, adapting how that proof is requested based on context. it analyzes factors like device, location, and network to determine if a login attempt looks typical or suspicious. Risk based authentication (also known as context based authentication) is the process of verifying a user as they sign on and scoring them against a set of policies that grant or deny access to resources based on the perceived risk. Risk based authentication is a dynamic access control approach that adjusts authentication strength and steps according to assessed risk at the time of access. it is not a single authentication mechanism; rather it orchestrates multiple signals, policies, and controls to make per request decisions. Risk based authentication (rba) is a dynamic approach to security that adjusts authentication requirements based on the level of perceived risk. learn how rba works, how it differs from context based authentication, and see real world examples of rba in action. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience.
Privacy Considerations For Risk Based Authentication Systems Risk Risk based authentication (also known as context based authentication) is the process of verifying a user as they sign on and scoring them against a set of policies that grant or deny access to resources based on the perceived risk. Risk based authentication is a dynamic access control approach that adjusts authentication strength and steps according to assessed risk at the time of access. it is not a single authentication mechanism; rather it orchestrates multiple signals, policies, and controls to make per request decisions. Risk based authentication (rba) is a dynamic approach to security that adjusts authentication requirements based on the level of perceived risk. learn how rba works, how it differs from context based authentication, and see real world examples of rba in action. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience.
Comments are closed.