Risk Assessment For Access Control System Installation Pdf Risk
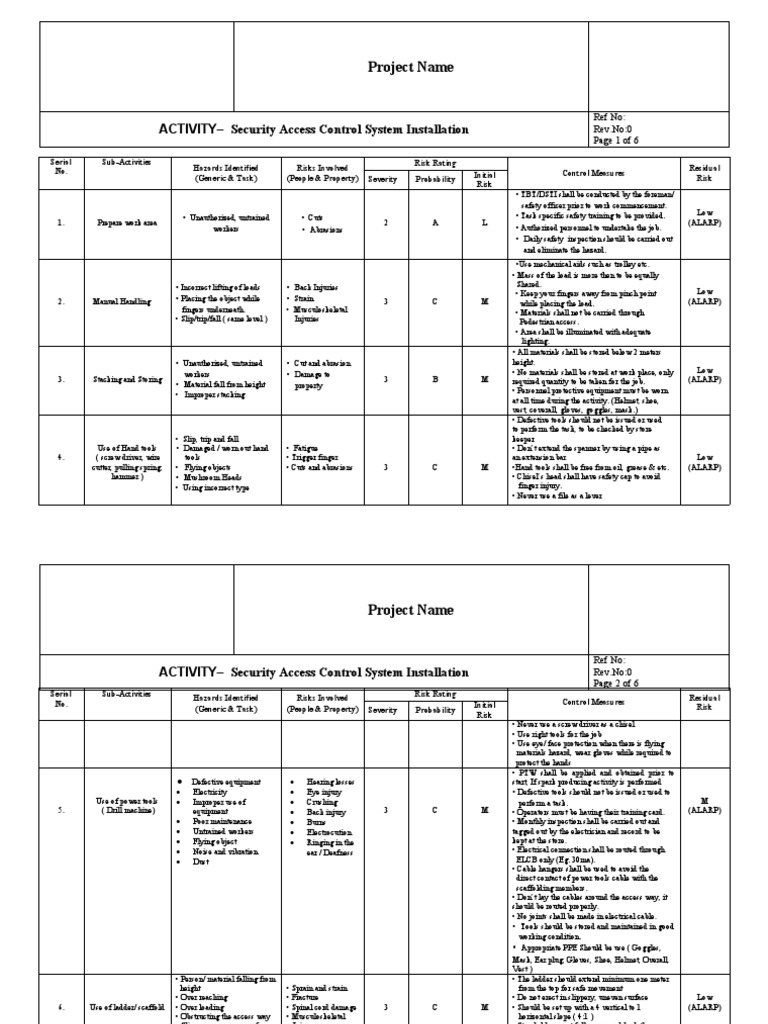
Risk Assessment For Access Control System Installation Pdf Risk This document provides a risk assessment for a security access control system installation project. it identifies five main activities (preparing the work area, manual handling, stacking storing, using hand tools, and using power tools) and associated hazards and risks. Installation procedure shall be followed as per manufacturer recommendation. avoid over reaching the cables to reduce from strain and pain. proper communication to be maintained between the workers while doing the installation. maintain a good housekeeping policy to prevent from slip, trip, and fall hazards.
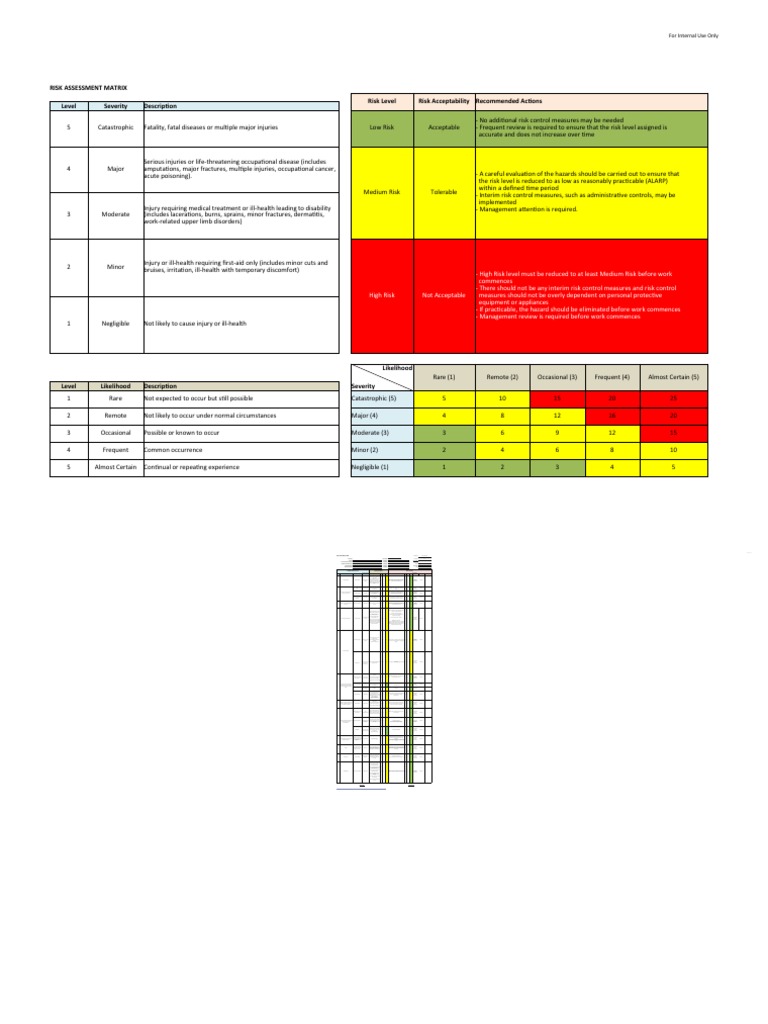
Samplee Risk Assessment Air Conditioning Installation Pdf Risk To download complete word file in editable format, click the link given below. We show that risk estimates for access requests actually differ based on the threat assessment approach that has been chosen. therefore, organizations must make prudent judgement while selecting a threat assessment function for risk based access control systems. Designed for hse professionals, project managers, engineers, and supervisors, it identifies potential hazards, evaluates risks, and outlines control measures to ensure safety during these activities. Ensure to have an emergency management plan in place as well as adequate numbers of trained first aid staff with easy access to fully stocked first aid kits, rescue equipment, material safety data sheets, adequate access to emergency communication equipment and fire fighting equipment suitable for all classes of fire and ignition sources.

Access Control System Pdf Access Control Door Designed for hse professionals, project managers, engineers, and supervisors, it identifies potential hazards, evaluates risks, and outlines control measures to ensure safety during these activities. Ensure to have an emergency management plan in place as well as adequate numbers of trained first aid staff with easy access to fully stocked first aid kits, rescue equipment, material safety data sheets, adequate access to emergency communication equipment and fire fighting equipment suitable for all classes of fire and ignition sources. Concerning the quantification of access risks, the proposed approaches deal mainly with the assessment of risks associated to access requests and authorizing accesses with regards to risk. A security risk assessment is a step by step process designed to evaluate the security risks associated with access control systems. this assessment model follows four key steps: identification, assessment, mitigation, and prevention. We describe a framework for risk assessment specifically within the context of risk based access control systems, which make authorization decisions by determining the security risk associated with access requests and weighing such security risk. Ysical security & risk vulnerability assessment a good facility management design and today’s state of the art access control technol. gy can significantly reduce security incidents. the firestorm physical security and risk vulnerability assessment is comprised of two parts, a t.

Access Control Systems Installation Best Practices Concerning the quantification of access risks, the proposed approaches deal mainly with the assessment of risks associated to access requests and authorizing accesses with regards to risk. A security risk assessment is a step by step process designed to evaluate the security risks associated with access control systems. this assessment model follows four key steps: identification, assessment, mitigation, and prevention. We describe a framework for risk assessment specifically within the context of risk based access control systems, which make authorization decisions by determining the security risk associated with access requests and weighing such security risk. Ysical security & risk vulnerability assessment a good facility management design and today’s state of the art access control technol. gy can significantly reduce security incidents. the firestorm physical security and risk vulnerability assessment is comprised of two parts, a t.
Comments are closed.