Reversing A Net Executable
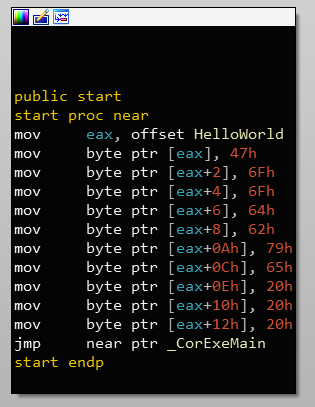
How Net Executables Are Loaded Low Level Pleasure Audio tracks for some languages were automatically generated. learn more. Run "ildasm" from the resulting command prompt. in the tool, select file > open and open your executable or dll.
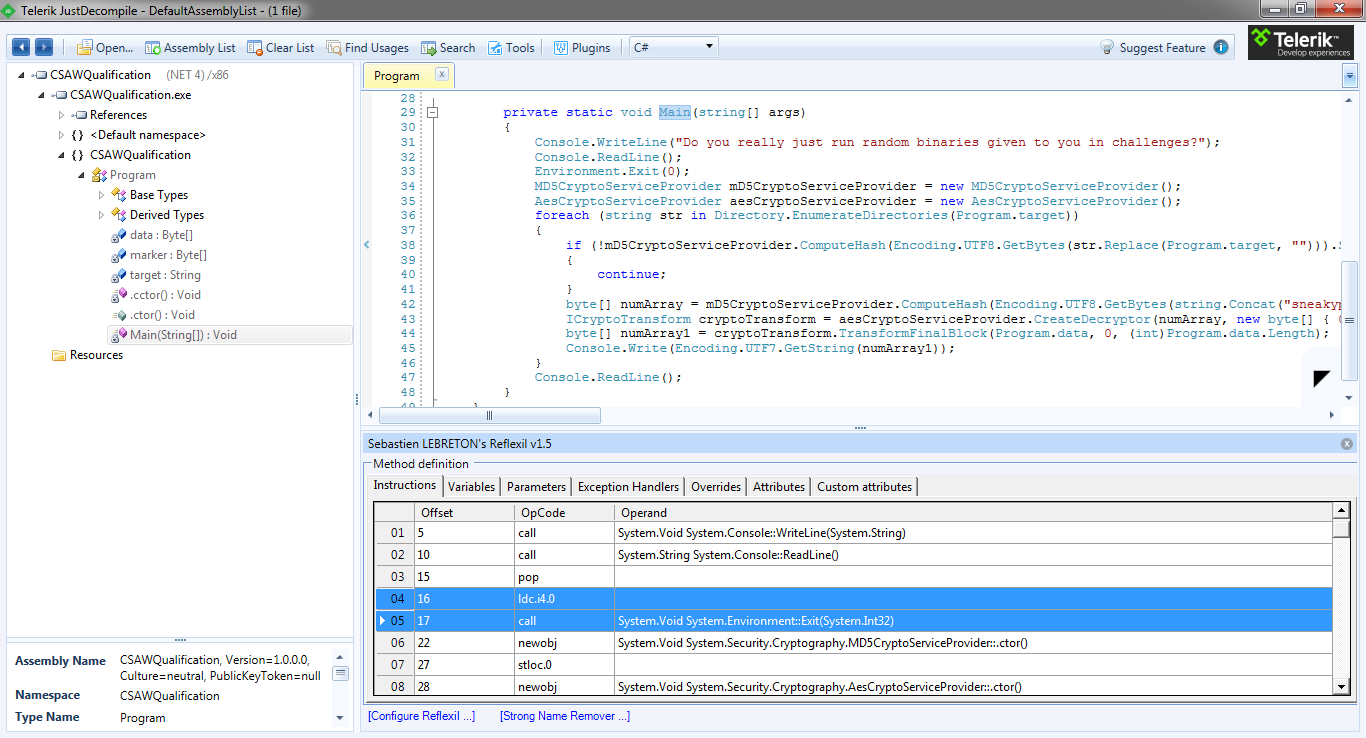
Intro To Net Reversing While many might associate reverse engineering with delving into complex assembler code, it’s possible to reverse engineer applications without touching assembler at all. In this blog post i showed the basic tooling and process necessary for reverse engineering and modify in binary form a application. it should be noted this same flow will work for c# and vb as they both compile down to msil. Unlike native code (e.g., c ), il retains high level metadata (class names, method signatures, and even variable names in debug builds), making it feasible to reverse engineer back to readable c#. in this guide, we’ll walk you through the entire process of decompiling a exe to recover lost c# source code. Here we will try to talk a little about how to adapt reverse engineering to new conditions. i will repeat the idea from the introduction: native aot compilation does not work with the file formats that are used in clr virtual machines to store a program and its metadata.
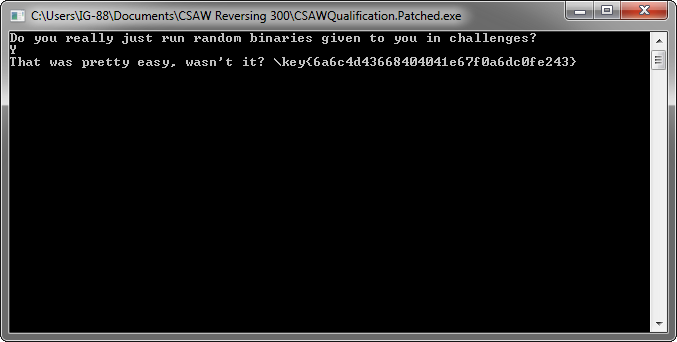
Intro To Net Reversing Unlike native code (e.g., c ), il retains high level metadata (class names, method signatures, and even variable names in debug builds), making it feasible to reverse engineer back to readable c#. in this guide, we’ll walk you through the entire process of decompiling a exe to recover lost c# source code. Here we will try to talk a little about how to adapt reverse engineering to new conditions. i will repeat the idea from the introduction: native aot compilation does not work with the file formats that are used in clr virtual machines to store a program and its metadata. Purpose to understand how files are constructed and practice reversing them. we'll use a file from the first flare on challenge in 2014. Revens is a windows based and ai powered reverse engineering toolkit "all in one", built for security purposes (malware analysis, penetration testing) and educational use only. This leaves us with tools used for reverse engineering arbitrary native code such as native debuggers (windbg vs x64dbg on windows, lldb gdb on unix like systems) and native code analysis frameworks (ghidra, ida, binary ninja, etc.). You’ve got your hands on a binary that you want to reverse engineer. what do you do? you can’t just open in the ghidra codebrowser like you’d normally do with an executable.
Comments are closed.