Reverse Engineering X86 Assembly

X64 Assembly Language And Reverse Engineering Practicals Scanlibs Reverse engineering x86 is a core technique that allows analysts to break down compiled code into assembly, exposing how malware manipulates registers, memory, and apis. Learn the basics of x86 assembly code for use in dissemblers like ghidra, ida, and binary ninja, and debuggers like x64dbg.

X86 64 Reverse Engineering Assembly Finding Addresses Stack Overflow This chapter covers dynamic reverse engineering analysis, hacking, the windows api createdirectoryw and removedirectoryw functions in x86 assembly. > click here to read the free pdf book. Welcome to the comprehensive roadmap for mastering reverse engineering and malware analysis. this roadmap is designed to guide individuals from beginner to expert level in the field of reverse engineering and malware analysis. Dive into the free, all in one reverse engineering tutorial by mytechnotalent. learn x86, arm, risc v, and more with hands on lessons, projects, and ctfs. What is assembly language? assembly is the lowest form of language which the cpu understand, it consists of sets of human readable instruction which are called opcode such as add, mov, etc.
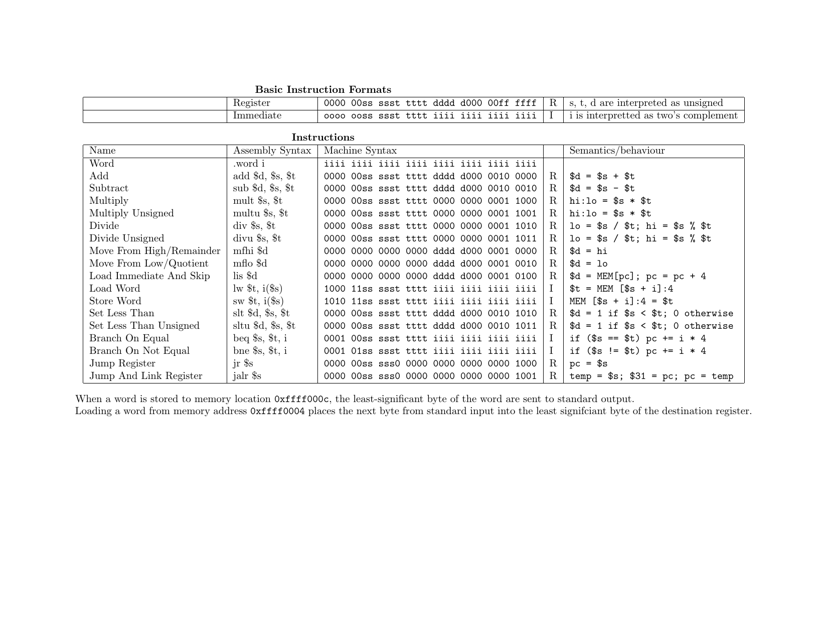
X86 Win32 Reverse Engineering Cheat Sheet Assembly Dive into the free, all in one reverse engineering tutorial by mytechnotalent. learn x86, arm, risc v, and more with hands on lessons, projects, and ctfs. What is assembly language? assembly is the lowest form of language which the cpu understand, it consists of sets of human readable instruction which are called opcode such as add, mov, etc. You should now have enough information (and hopefully, motivation) to start your journey reverse engineering executables. start by writing dummy c code, compiling it, and debugging it while single stepping through the disassembly instructions (visual studio allows you to do this, by the way). Before we can get started with reverse engineering, we need to understand the language required for reverse engineering: the language of the processor. in this section, we will focus on learning this language and also perform some reverse engineering. This article is not designed to teach you how to code using assembly language, the aim is introducing you the most common instructions you will meet when practicing reverse code engineering and handling dissemblers debuggers, and providing you only a very basic introduction. Learning how x86 works and common instruction formats is essential to success. this chapter takes a hands‐on approach to reverse engineering and software cracking. it introduces gdb, a powerful debugger, and explores some important tips and tricks for software reverse engineering and cracking.

X86 Win32 Reverse Engineering Cheat Sheet Assembly You should now have enough information (and hopefully, motivation) to start your journey reverse engineering executables. start by writing dummy c code, compiling it, and debugging it while single stepping through the disassembly instructions (visual studio allows you to do this, by the way). Before we can get started with reverse engineering, we need to understand the language required for reverse engineering: the language of the processor. in this section, we will focus on learning this language and also perform some reverse engineering. This article is not designed to teach you how to code using assembly language, the aim is introducing you the most common instructions you will meet when practicing reverse code engineering and handling dissemblers debuggers, and providing you only a very basic introduction. Learning how x86 works and common instruction formats is essential to success. this chapter takes a hands‐on approach to reverse engineering and software cracking. it introduces gdb, a powerful debugger, and explores some important tips and tricks for software reverse engineering and cracking.

X86 Win32 Reverse Engineering Cheat Sheet Assembly This article is not designed to teach you how to code using assembly language, the aim is introducing you the most common instructions you will meet when practicing reverse code engineering and handling dissemblers debuggers, and providing you only a very basic introduction. Learning how x86 works and common instruction formats is essential to success. this chapter takes a hands‐on approach to reverse engineering and software cracking. it introduces gdb, a powerful debugger, and explores some important tips and tricks for software reverse engineering and cracking.
Comments are closed.