Reverse Engineering Reagan Becker

Reverse Engineering Reagan Becker This undertaking is particularly challenging as it depends on non trivial technical steps as well as on cognitive factors of the human reverse engineer. to the best of our knowledge, it is the first time such a study based on observing a group of reverse engineers has been conducted. Reverse engineering (re) is defined as the process of transforming real objects back into engineering concepts or models, typically employed when product documentation is lost or when duplicating physical products without technical details.

Reverse Engineering Tkpitsirikos Applying such methods in a complex biological context remains challenging. we use reverse engineering to study post transcriptional regulation in pattern formation. as a case study, we analyse expression of the gap genes krüppel, knirps, and giant in drosophila melanogaster. Although the process is specific to the object on which it is being performed, all reverse engineering processes consist of three basic steps: information extraction, modeling, and review. information extraction is the practice of gathering all relevant information for performing the operation. Apple refers to this fpga as maggie. by reverse engineering the proprietary signal processing algorithm implemented on maggie, we generate novel insights into the actual efforts required to commit fpga ip theft and the challenges an attacker faces on the way. Reverse engineering is a vast subject, and we have only been able to present a conceptual overview of many of the topics in this chapter, together with a little more detail in some places to give insight into a few problems of particular significance.

Online At The Reagan Library With Jean Becker 2024 The Ronald Reagan Apple refers to this fpga as maggie. by reverse engineering the proprietary signal processing algorithm implemented on maggie, we generate novel insights into the actual efforts required to commit fpga ip theft and the challenges an attacker faces on the way. Reverse engineering is a vast subject, and we have only been able to present a conceptual overview of many of the topics in this chapter, together with a little more detail in some places to give insight into a few problems of particular significance. In this chapter we discuss three lenses, namely (1) requirements for reverse engineering tools, (2) construction of reverse engineering tools, and (3) evaluation of reverse engineering tools. To determine whether reverse engineering falls within the limits of legality, the paper explores first the trade secrets (their meaning and forms, their regulation and legal protection). Reverse engineering (re) is a method employed to understand the physical and functional details of a product with the intention of replication, re creation, or redesign by discovering both the dimensions and the design decisions that were made to arrive at the final product. We evaluate these techniques on six benchmarks that are representative of different fpga applications and have been synthesized for xilinx and lattice fpgas, as well as in an end to end white box case study.
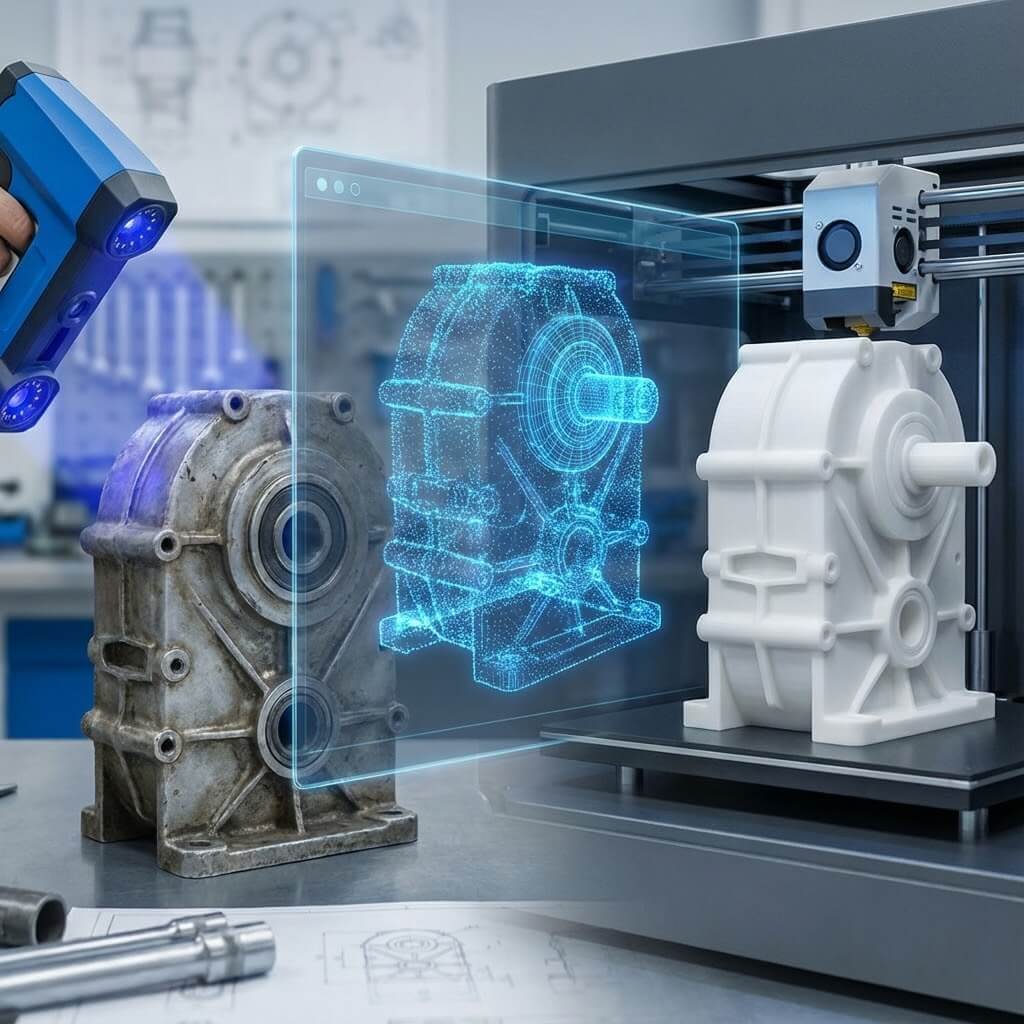
Reverse Engineering What It Is How It Works When To Use Guide 2026 In this chapter we discuss three lenses, namely (1) requirements for reverse engineering tools, (2) construction of reverse engineering tools, and (3) evaluation of reverse engineering tools. To determine whether reverse engineering falls within the limits of legality, the paper explores first the trade secrets (their meaning and forms, their regulation and legal protection). Reverse engineering (re) is a method employed to understand the physical and functional details of a product with the intention of replication, re creation, or redesign by discovering both the dimensions and the design decisions that were made to arrive at the final product. We evaluate these techniques on six benchmarks that are representative of different fpga applications and have been synthesized for xilinx and lattice fpgas, as well as in an end to end white box case study.

Reverse Engineering Software What Is Reverse Engineering Autodesk Reverse engineering (re) is a method employed to understand the physical and functional details of a product with the intention of replication, re creation, or redesign by discovering both the dimensions and the design decisions that were made to arrive at the final product. We evaluate these techniques on six benchmarks that are representative of different fpga applications and have been synthesized for xilinx and lattice fpgas, as well as in an end to end white box case study.

Reverse Engineering Cube3
Comments are closed.