Reverse Engineering Malware With Ida Part 1
Anti Reverse Engineering Malware Vs Antivirus Software In this video, we take a simple windows 32bits malware and reverse engineer it in ida. we cover topics such as: debugging malware with bochs self modifying. Now we can proceed to advanced topics like kernel mode malware, rootkit analysis, and related techniques. this comprehensive roadmap provides a step by step guide for mastering reverse engineering and malware analysis.

Malware Reverse Engineering For Beginners Explained Welcome to the comprehensive roadmap for mastering reverse engineering and malware analysis. this roadmap is designed to guide individuals from beginner to expert level in the field of reverse engineering and malware analysis. This series will provide re basics for malware researchers, analysts and ir experts who have no reverse engineering experience but wish to learn how. in part 1, you will learn about basic computing terms and assembly language. In this blog post we’ll lay down the foundations of analyzing and reverse engineering windows malicious files. we’ll see various mechanisms malware uses to achieve their main objectives, and emphasize main key points to keep in mind for future investigations. This class picks up where the introduction to reverse engineering software course left off, exploring how static reverse engineering techniques can be used to understand what a piece of malware does and how it can be removed.

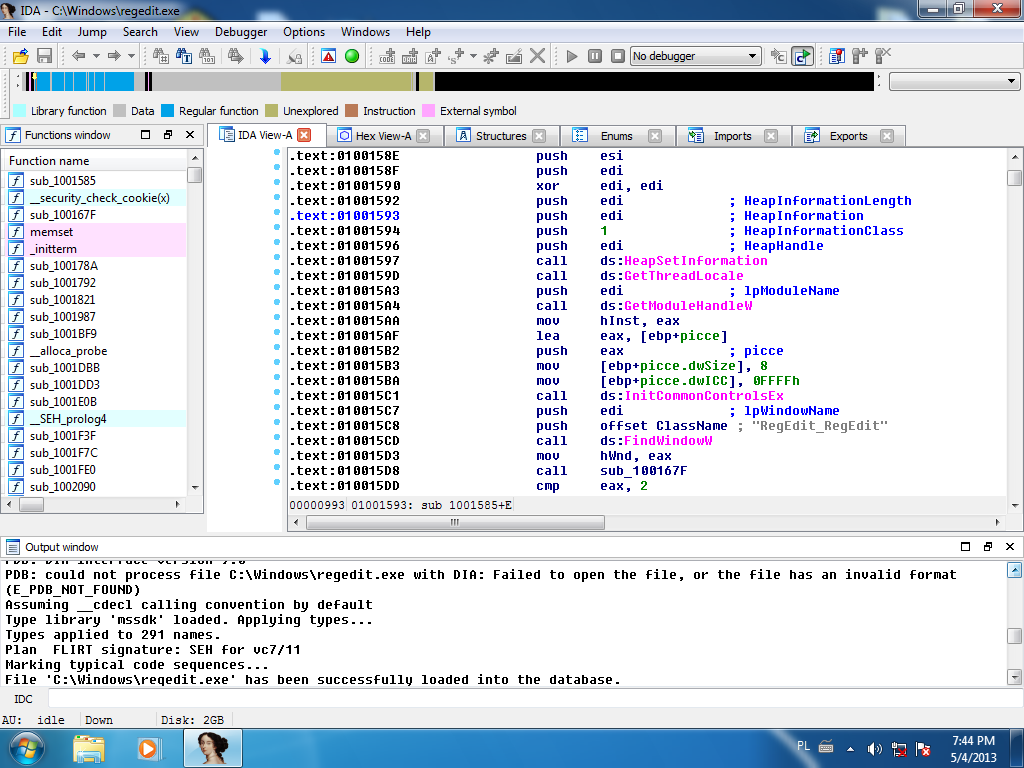
Beginner S Guide To Malware Analysis And Reverse Engineering Intezer In this blog post we’ll lay down the foundations of analyzing and reverse engineering windows malicious files. we’ll see various mechanisms malware uses to achieve their main objectives, and emphasize main key points to keep in mind for future investigations. This class picks up where the introduction to reverse engineering software course left off, exploring how static reverse engineering techniques can be used to understand what a piece of malware does and how it can be removed. Let’s do the dissassembly of the assembly code that we examined in ida:. In this course by matt briggs, we will explore what drives people to reverse engineer software and the methodology and tools used to do it. during the course students will complete many hands on exercises. I am about to embark upon probably the most technically demanding tutorial series, reverse engineering malware. before i do so, i thought i would take a few moments to explain why you should study and invest your time into reverse engineering. If you are a beginner to reverse engineering and want to learn how to use ida pro to reverse engineer and analyze linux and windows programs, then this is the course for you.
Unveiling The Art Of Cracking Byte Patching With Ida Pro Infosec Let’s do the dissassembly of the assembly code that we examined in ida:. In this course by matt briggs, we will explore what drives people to reverse engineer software and the methodology and tools used to do it. during the course students will complete many hands on exercises. I am about to embark upon probably the most technically demanding tutorial series, reverse engineering malware. before i do so, i thought i would take a few moments to explain why you should study and invest your time into reverse engineering. If you are a beginner to reverse engineering and want to learn how to use ida pro to reverse engineer and analyze linux and windows programs, then this is the course for you.
Comments are closed.