Reverse Engineering Malware In Pdf Files
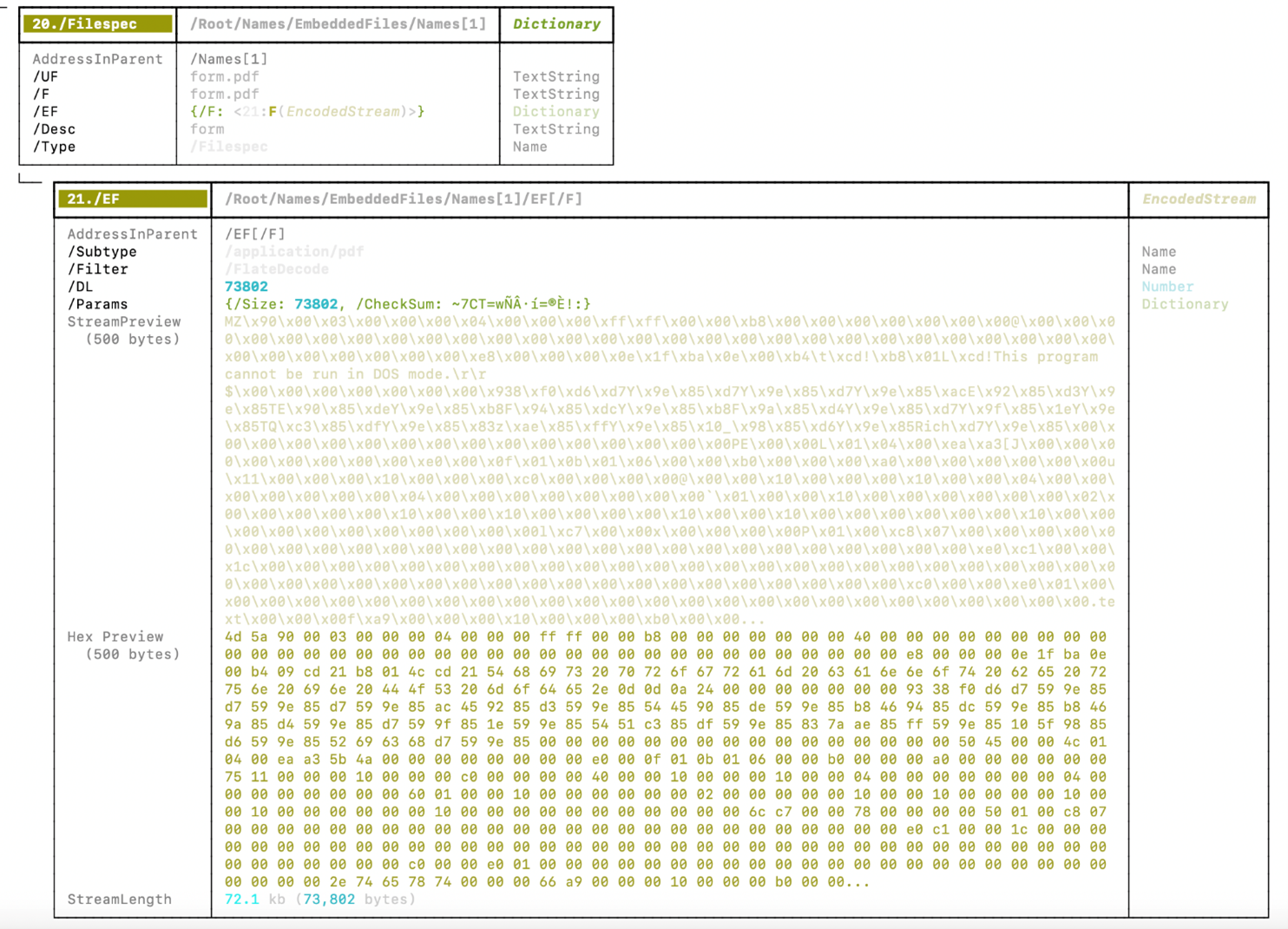
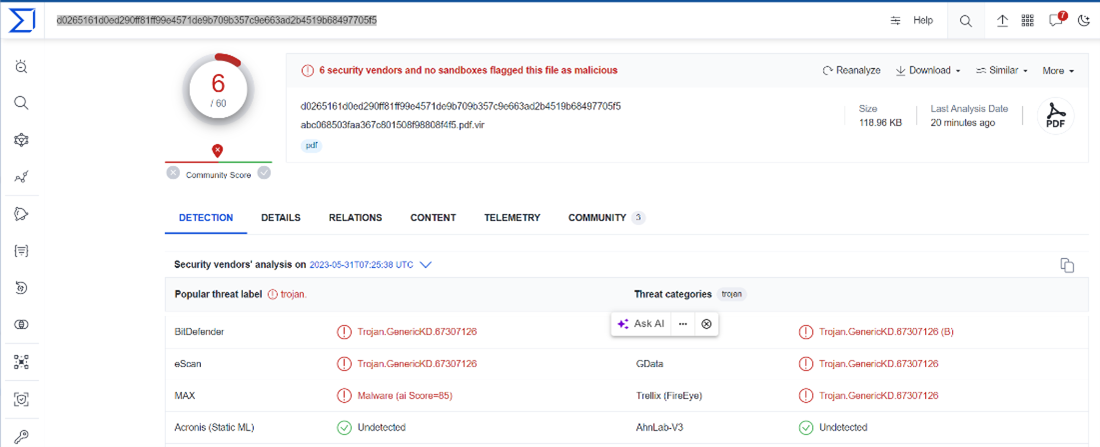
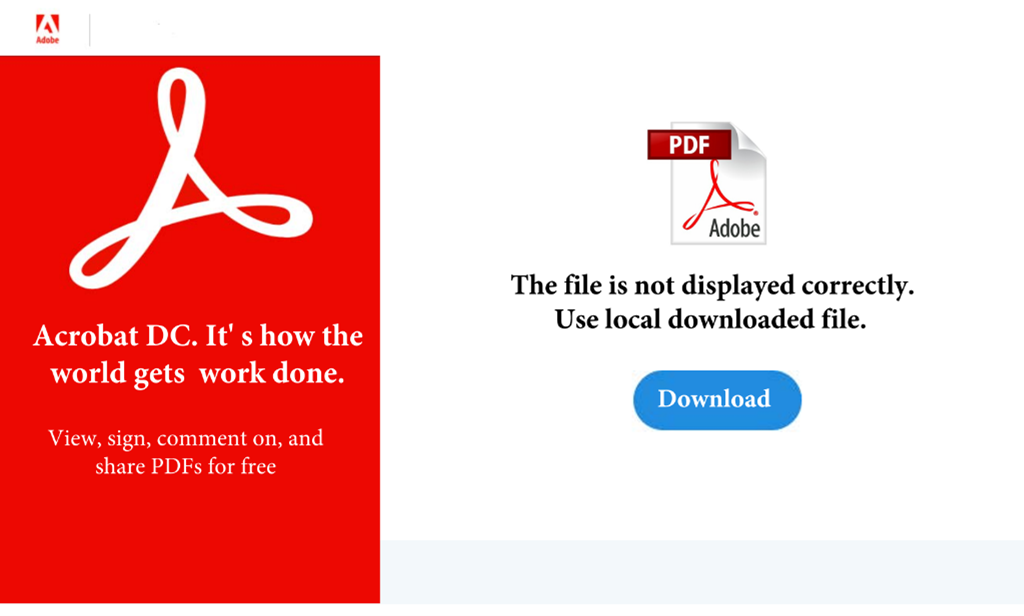
The Beginners Guide To Adobe Pdf Malware Reverse Engineering Part 2 The objective of this research is to present the fundamentals of malware reverse engineering, the tools, and techniques needed to properly analyze malicious programs to determine their. In this blog, we will fetch a potentially suspicious file from malwarebazaar and examine the pdf file jointly (remember to operate within a virtual machine). utilizing the “file type:pdf” filter, we will obtain the most recently uploaded pdf files within the framework.
The Beginners Guide To Adobe Pdf Malware Reverse Engineering Part 1 Art of cracking and hacking. he started his professional caree back in 2003 at trend micro. from then, he has shared his knowledge in reverse engineering and developed relevant malware related systems with big companies such as esoft, sunbelt gfi threattrack, nss. While specific measures need to be taken for particular cases, this handbook gives an overview of how to analyse malware samples in a closed environment by reverse engineering using static or dynamic malware analysis techniques. To answer all these questions, you have to carry out a malware analysis using the reverse engineering (re) technique. in this chapter, we are not going to focus on how to find the malware (forensic analysis), but on how to analyze it once it has been found. ng on the ana machines. In simple terms, reverse engineering malware can be defined as engineering malware to obtain information about malware behavior. several tools such as a disassembler, debugger, pe viewer, and network analyzer are required to reverse engineer malware.
The Beginners Guide To Adobe Pdf Malware Reverse Engineering Part 1 To answer all these questions, you have to carry out a malware analysis using the reverse engineering (re) technique. in this chapter, we are not going to focus on how to find the malware (forensic analysis), but on how to analyze it once it has been found. ng on the ana machines. In simple terms, reverse engineering malware can be defined as engineering malware to obtain information about malware behavior. several tools such as a disassembler, debugger, pe viewer, and network analyzer are required to reverse engineer malware. Malware reverse engineering handbook free download as pdf file (.pdf), text file (.txt) or read online for free. this document provides an overview of malware reverse engineering techniques for analyzing and mitigating malware threats. The goal of this research is to comprehensively study the complex world of analyzing malware and reverse engineering. generally, there will be a look at different malware types, different analysis methods, the reverse engineering process, present some case studies, and discuss some of the challenges being faced, as well as ethics.[2]. Today we’re going to show how to create a malicious executable that looks like a pdf, word doc, or web browser executable with the functionality of the normal file program, but also our. Will demonstrate how to create the “alert (1)” of pdf injection and how to improve it to inject javascript that can steal credentials and open a malicious link. we can inject code in pdf like xss injection inside the javascript function call.
Comments are closed.