Reverse Engineering Code With Ida Pro Ultrashutter

Reverse Engineering Code With Ida Pro 2 2 Vangelis Ida hub manages multiple ida pro instances centrally. agents interact with ida remotely via http api for reverse engineering tasks. Reverse engineering code with ida pro.pdf google drive 10 11.
Reverse Engineering Code With Ida Pro Glowlula In this article, we’ll dive into deep, hands on static analysis with ida pro—the go to disassembler for hackers and security professionals. from its earliest releases, it has held a well earned lead in the market. If you want to learn how to build a repeatable ida pro workflow that generates real artifacts—call graphs, mmio reports, failure paths—and do it in a way you can scale, my ebook is designed to be the shortest path from “i’m curious about re” to “i can run a pipeline and get answers.”. Uncover the good, the bad, and the ugly code with ida pro! reverse engineering code with ida pro. reviews cannot be added to this item. Ida pro's interactive interface and programmable development language provide you with complete control over code disassembly and debugging. this is the only book which focuses exclusively on the world's most powerful and popular took for reverse engineering code.
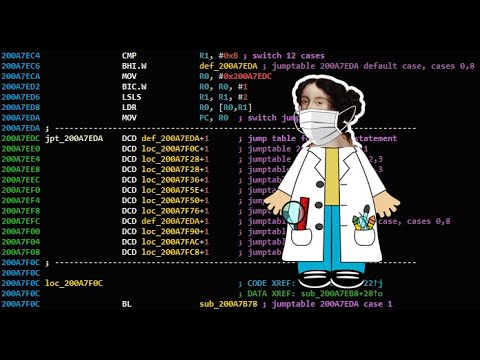
Reverse Engineering Code With Ida Pro Glowlula Uncover the good, the bad, and the ugly code with ida pro! reverse engineering code with ida pro. reviews cannot be added to this item. Ida pro's interactive interface and programmable development language provide you with complete control over code disassembly and debugging. this is the only book which focuses exclusively on the world's most powerful and popular took for reverse engineering code. What will i learn in part 1? you will learn how to use ida pro, and learn the early stages of reverse engineering. but how? reing is a massive field. yes it is a massive field, but the goal of these tutorials are to help you understand what to do, not how to do it. reverse engineering has been around for 100's of years, believe it or not. This document provides an overview of the reverse engineering approaches and methodologies used throughout the ida pro idb database repository. it covers fundamental concepts, workflows, and practical techniques that form the backbone of game hacking and binary analysis work. In this article you will learn live binary sample target, target analysis with ida pro, cracking the target and an alternative way of tracing. Anti reverse engineering techniques attempt to obfuscate code paths allows automated unpacking decrypting of "protected" binaries upx, burneye, shiva, telock, aspack,.

Reverse Engineering Code With Ida Pro Auctionsadams What will i learn in part 1? you will learn how to use ida pro, and learn the early stages of reverse engineering. but how? reing is a massive field. yes it is a massive field, but the goal of these tutorials are to help you understand what to do, not how to do it. reverse engineering has been around for 100's of years, believe it or not. This document provides an overview of the reverse engineering approaches and methodologies used throughout the ida pro idb database repository. it covers fundamental concepts, workflows, and practical techniques that form the backbone of game hacking and binary analysis work. In this article you will learn live binary sample target, target analysis with ida pro, cracking the target and an alternative way of tracing. Anti reverse engineering techniques attempt to obfuscate code paths allows automated unpacking decrypting of "protected" binaries upx, burneye, shiva, telock, aspack,.
Comments are closed.