Reverse Engineering Code With Ida Pro Auctionsadams

Reverse Engineering Code With Ida Pro 2 2 Vangelis With this challenge in mind, our intermediate level course is built around analysis of 10 targeted malware cases used in the wild by powerful apt actors recently. In the example function we can use "invalid percentage of enemies killed\n"⁴ string that's inside the devmsg () call. after you locate the string go to ida and open the strings window⁵, then search⁶ for the string you found, then double click on it. make sure you select the exact string.
Reverse Engineering Code With Ida Pro Glowlula In this article, we’ll dive into deep, hands on static analysis with ida pro—the go to disassembler for hackers and security professionals. from its earliest releases, it has held a well earned lead in the market. In this tutorial i will explore the basic concepts of reverse engineering by reversing a simple crackme. the crackme used in this tutorial is from binary auditing course. i will use static approach to solve the problem as it clearly demonstrates the power of reverse engineering. Ms’ computer. one of the few offenses we can deploy in order to understand and predict the impact of these malicious software programs is through employment of advanced reverse engineering techniques, leveraging industry standard tools from companies like data resc. Anti reverse engineering techniques attempt to obfuscate code paths allows automated unpacking decrypting of "protected" binaries upx, burneye, shiva, telock, aspack,.
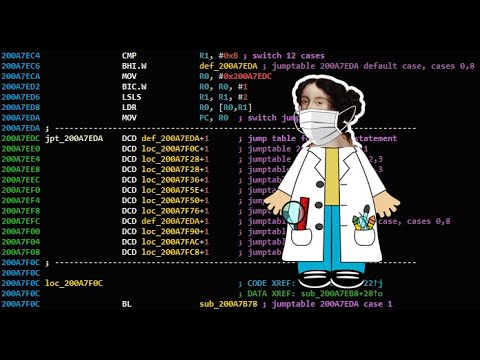
Reverse Engineering Code With Ida Pro Glowlula Ms’ computer. one of the few offenses we can deploy in order to understand and predict the impact of these malicious software programs is through employment of advanced reverse engineering techniques, leveraging industry standard tools from companies like data resc. Anti reverse engineering techniques attempt to obfuscate code paths allows automated unpacking decrypting of "protected" binaries upx, burneye, shiva, telock, aspack,. Reverse engineering code with ida pro.pdf google drive 10 11. Ida pro is a static and dynamic analysis tool that allows reversing in 32 and 64 bits, unlike ollydbg which only works in 32 bits. this guide introduces ida pro by opening the cruehead crackme to demonstrate basic functions such as code navigation and the different views available. In this article you will learn live binary sample target, target analysis with ida pro, cracking the target and an alternative way of tracing. On april 3, 2026, the authors publish sighthouse, an open source tool that helps reverse engineers retrieve metadata and identify similar functions across libraries, binaries, and source code. they benchmarked algorithms on a dataset of 9,775 programs (379,822 functions, 782 mb), conclude bsim is robust for production, and ship plugins for ida pro, ghidra, and binary ninja plus a rest frontend.

Reverse Engineering Code With Ida Pro Auctionsadams Reverse engineering code with ida pro.pdf google drive 10 11. Ida pro is a static and dynamic analysis tool that allows reversing in 32 and 64 bits, unlike ollydbg which only works in 32 bits. this guide introduces ida pro by opening the cruehead crackme to demonstrate basic functions such as code navigation and the different views available. In this article you will learn live binary sample target, target analysis with ida pro, cracking the target and an alternative way of tracing. On april 3, 2026, the authors publish sighthouse, an open source tool that helps reverse engineers retrieve metadata and identify similar functions across libraries, binaries, and source code. they benchmarked algorithms on a dataset of 9,775 programs (379,822 functions, 782 mb), conclude bsim is robust for production, and ship plugins for ida pro, ghidra, and binary ninja plus a rest frontend.

4 Reversing With Ida Pro From Scratch Pdf Pdf String Computer In this article you will learn live binary sample target, target analysis with ida pro, cracking the target and an alternative way of tracing. On april 3, 2026, the authors publish sighthouse, an open source tool that helps reverse engineers retrieve metadata and identify similar functions across libraries, binaries, and source code. they benchmarked algorithms on a dataset of 9,775 programs (379,822 functions, 782 mb), conclude bsim is robust for production, and ship plugins for ida pro, ghidra, and binary ninja plus a rest frontend.
Comments are closed.