Retaliating Against Metamask Scammers With Python Nelson Figueroa
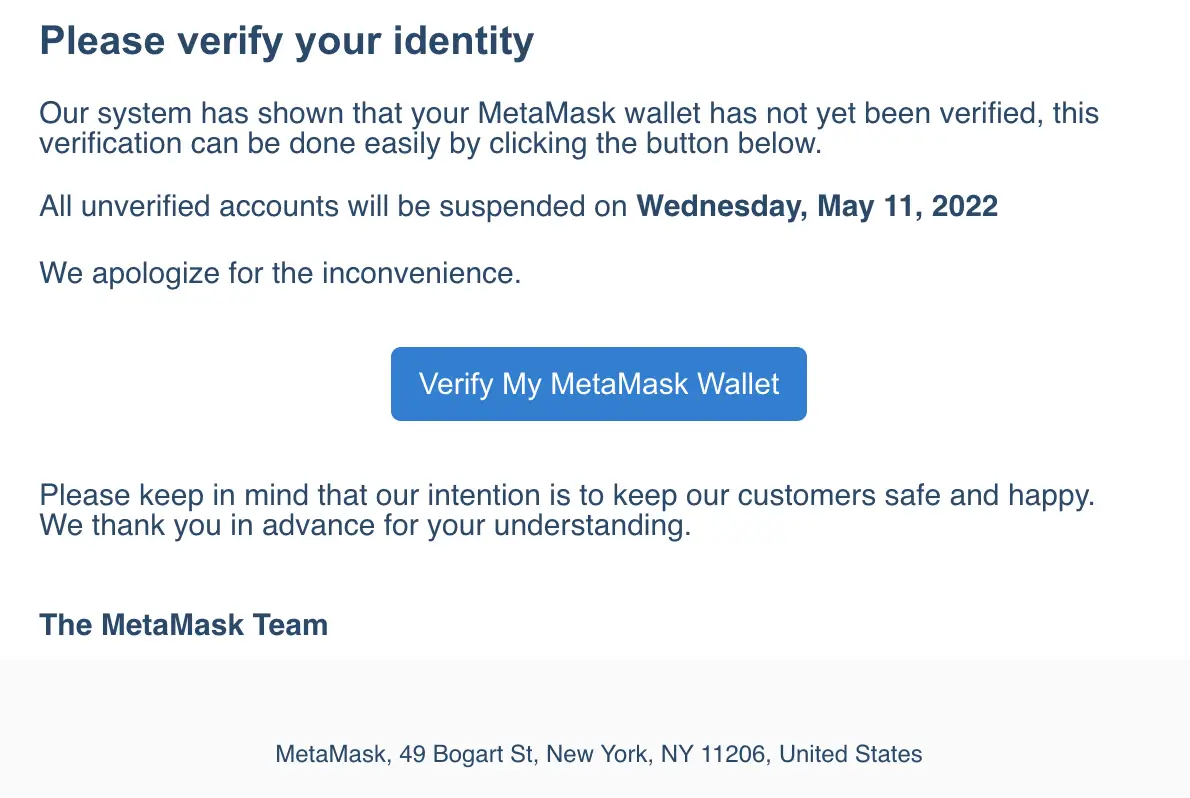
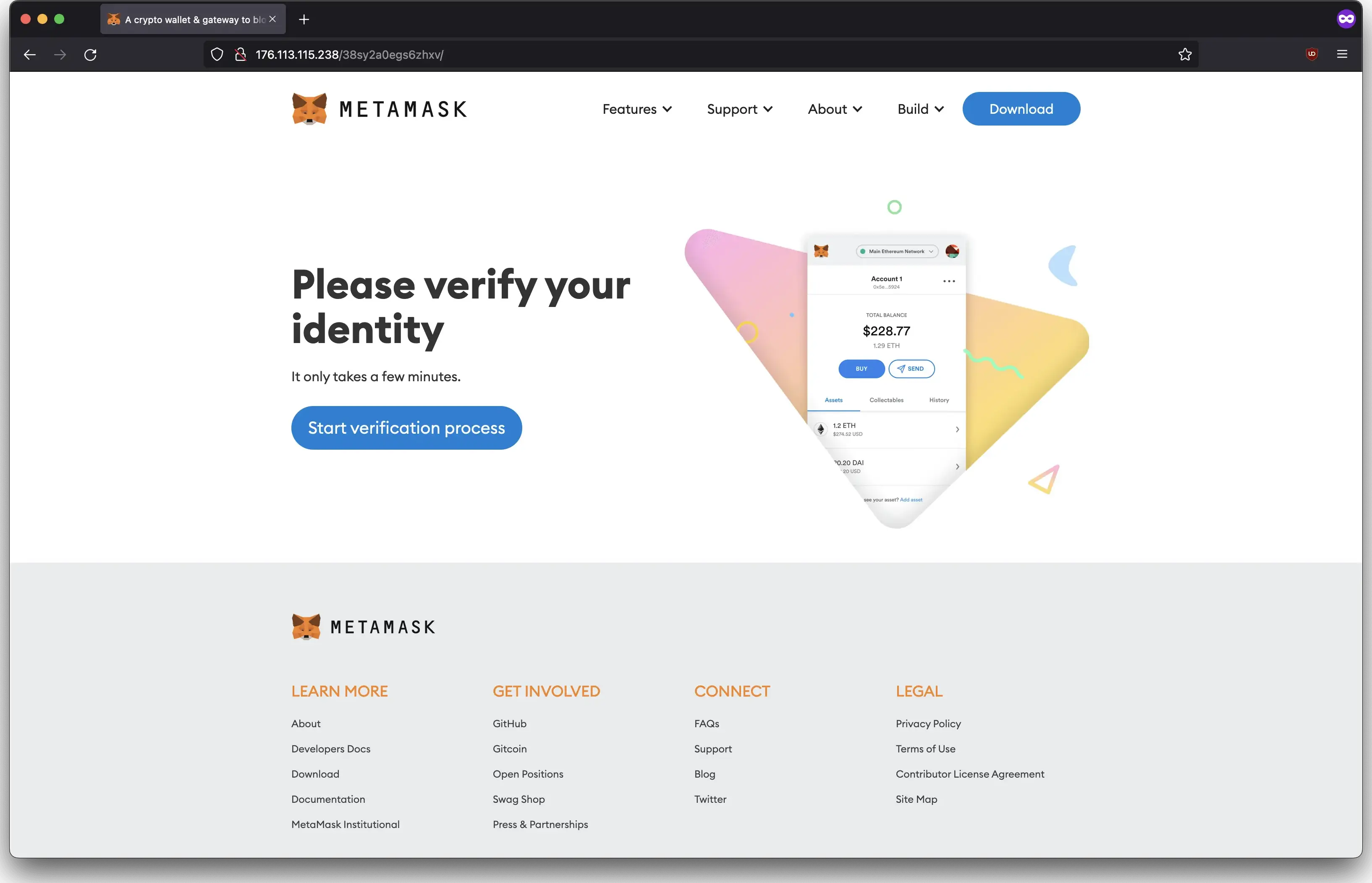
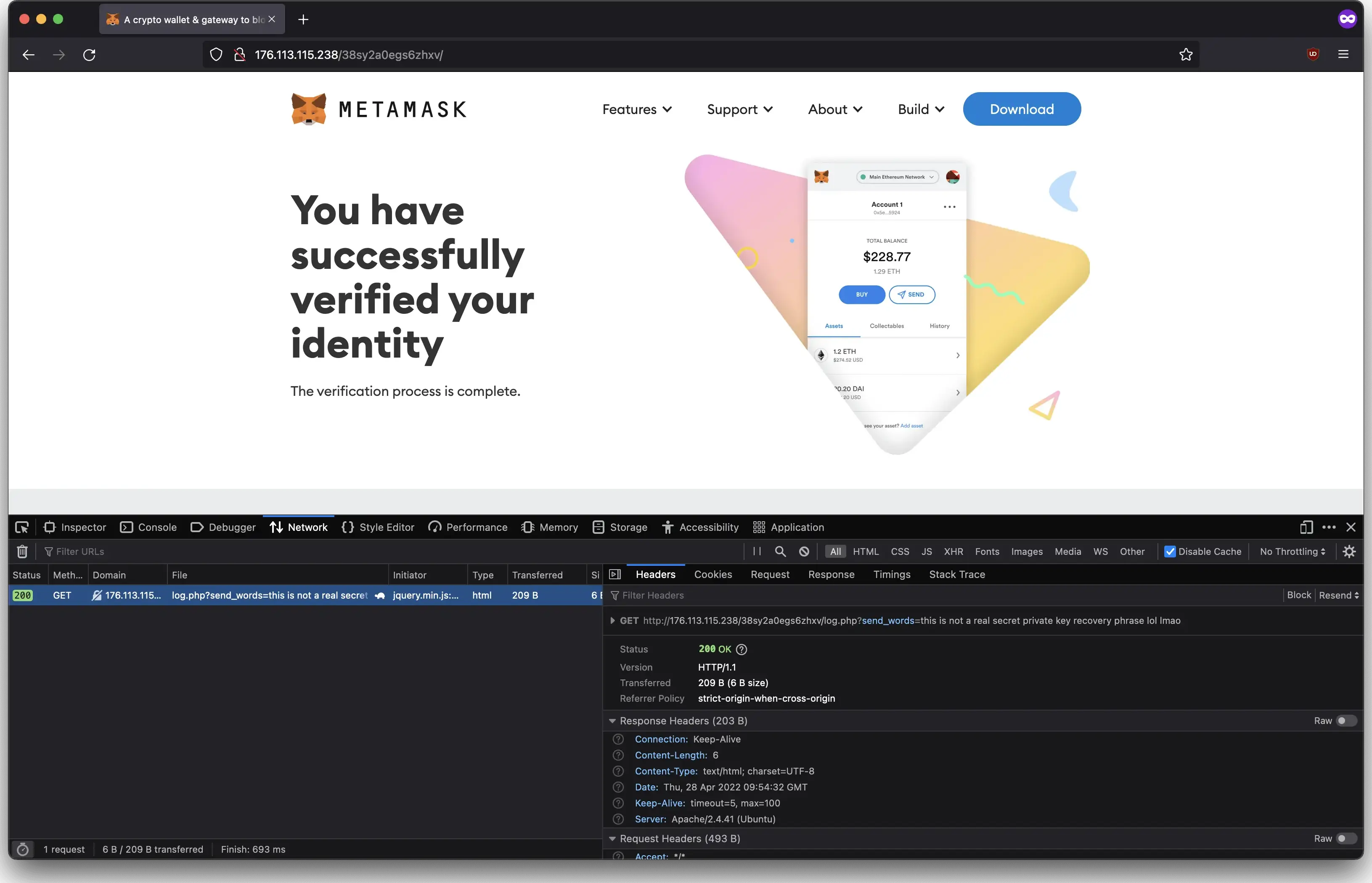
Retaliating Against Metamask Scammers With Python Nelson Figueroa Recently, i received this email: i have never used metamask. it was pretty obvious this was a scam. i decided to check it out anyway out of curiosity. it led me to this site which looked legit but had a major flaw: there is no domain and i’m accessing an insecure ip address. Using python to send fake seed phrases to a metamask scam site.

Retaliating Against Metamask Scammers With Python Nelson Figueroa 2022 07 02 · updated 2026 01 24 · 3 min · 555 words cybersecurity python retaliating against metamask scammers with python. With this information, i could create a python script to flood the scammers with fake credentials. this way, they won’t know what credentials are valid when using them themselves. Euchre 350 facebook 351 facebook 352 fall 353 fight 354 folder 355 foundation 356 free 357 fund 358 gaana 359 gallery 360 game 361 games 362 garden 363 gmail 364 go.cps.edu 365 go90 366 google 367 greatest 368 guitar 369 hangouts 370 hear 371 heart 372 hey 373 hike 374 hip hop 375 hits 376 hotmail 377 house 378 houses 379 identify 380 impeach 381 install 382 kick 383 kik 384. New metamask phishing scam mimics 2fa verification to steal user seed phrases. attackers use near identical domains and branded emails for convincing social engineering. the scam resurfaces as crypto activity and retail interest rebound.

Retaliating Against Metamask Scammers With Python Nelson Figueroa Euchre 350 facebook 351 facebook 352 fall 353 fight 354 folder 355 foundation 356 free 357 fund 358 gaana 359 gallery 360 game 361 games 362 garden 363 gmail 364 go.cps.edu 365 go90 366 google 367 greatest 368 guitar 369 hangouts 370 hear 371 heart 372 hey 373 hike 374 hip hop 375 hits 376 hotmail 377 house 378 houses 379 identify 380 impeach 381 install 382 kick 383 kik 384. New metamask phishing scam mimics 2fa verification to steal user seed phrases. attackers use near identical domains and branded emails for convincing social engineering. the scam resurfaces as crypto activity and retail interest rebound. This repository includes both a standalone python script and a flask rest api for detecting suspicious or malicious urls. it leverages metamask ’s eth phishing detect lists, fuzzy domain matching, whois lookups, punycode checks, and more. Checkmarx researchers discovered pypi malware posing as crypto wallet tools. these malicious packages stole private keys and recovery phrases, targeting wallets like metamask, trust wallet, and exodus. This article will provide an in depth look at how the metamask wallet verification scam works, including a step by step breakdown of the process used by scammers. we’ll also explore what you should do if you receive one of these fraudulent emails or accidentally provide sensitive information. On september 22nd, multiple packages were published to the pypi platform, targeting a wide range of crypto wallets including atomic, trust wallet, metamask, ronin, tronlink, and exodus. the malicious packages distributed their code across dependencies, making detection more challenging.
Retaliating Against Metamask Scammers With Python Nelson Figueroa This repository includes both a standalone python script and a flask rest api for detecting suspicious or malicious urls. it leverages metamask ’s eth phishing detect lists, fuzzy domain matching, whois lookups, punycode checks, and more. Checkmarx researchers discovered pypi malware posing as crypto wallet tools. these malicious packages stole private keys and recovery phrases, targeting wallets like metamask, trust wallet, and exodus. This article will provide an in depth look at how the metamask wallet verification scam works, including a step by step breakdown of the process used by scammers. we’ll also explore what you should do if you receive one of these fraudulent emails or accidentally provide sensitive information. On september 22nd, multiple packages were published to the pypi platform, targeting a wide range of crypto wallets including atomic, trust wallet, metamask, ronin, tronlink, and exodus. the malicious packages distributed their code across dependencies, making detection more challenging.
Retaliating Against Metamask Scammers With Python Nelson Figueroa This article will provide an in depth look at how the metamask wallet verification scam works, including a step by step breakdown of the process used by scammers. we’ll also explore what you should do if you receive one of these fraudulent emails or accidentally provide sensitive information. On september 22nd, multiple packages were published to the pypi platform, targeting a wide range of crypto wallets including atomic, trust wallet, metamask, ronin, tronlink, and exodus. the malicious packages distributed their code across dependencies, making detection more challenging.
Comments are closed.