Rest Api Configure Authentication For A Rest Api Source
Rest Api Authentication Download Free Pdf Hypertext Transfer For apis that require authentication to access their endpoints, the rest api source supports various authentication methods, including token based authentication, query parameters, basic authentication, and custom authentication. Amazon cognito user pools let you create customizable authentication and authorization solutions for your rest apis. amazon cognito user pools are used to control who can invoke rest api methods.
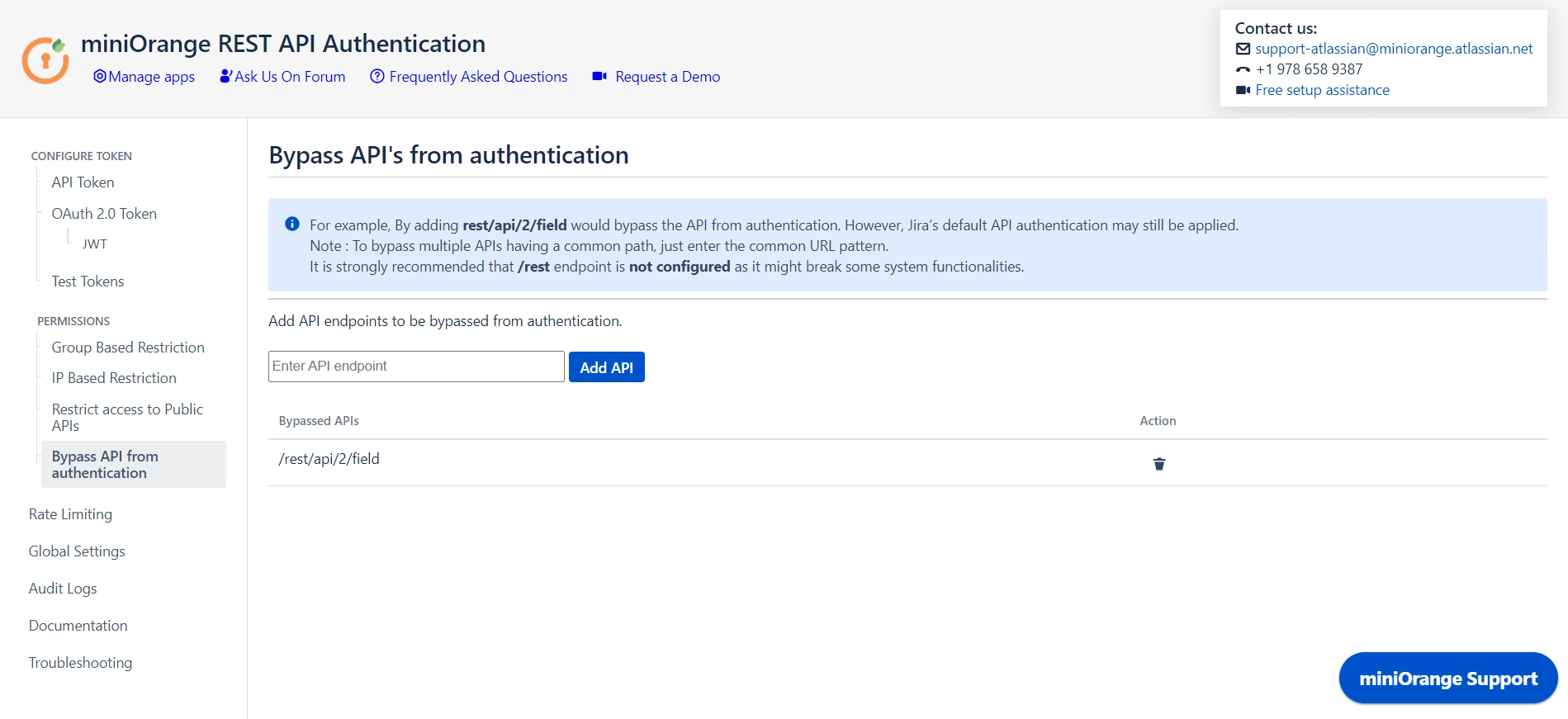
Api Key Authentication For Jira Rest Api Rest Api Key Auth This page describes how to authenticate when you make a rest request to a google api. for information about how to authenticate when you use google client libraries, see authenticate. We'll explain how rest api authentication works by breaking down popular authentication methods and by covering a few real world examples. Setting up oauth 2.0 for your rest api involves several important steps to ensure a secure and efficient authentication system. below, we break down the key components you’ll need to implement. Therefore, a clear understanding of the available rest api authentication methods is essential for developers, founders, and product teams alike. this guide provides a comprehensive breakdown of seven primary authentication methods, designed to help you make an informed choice.
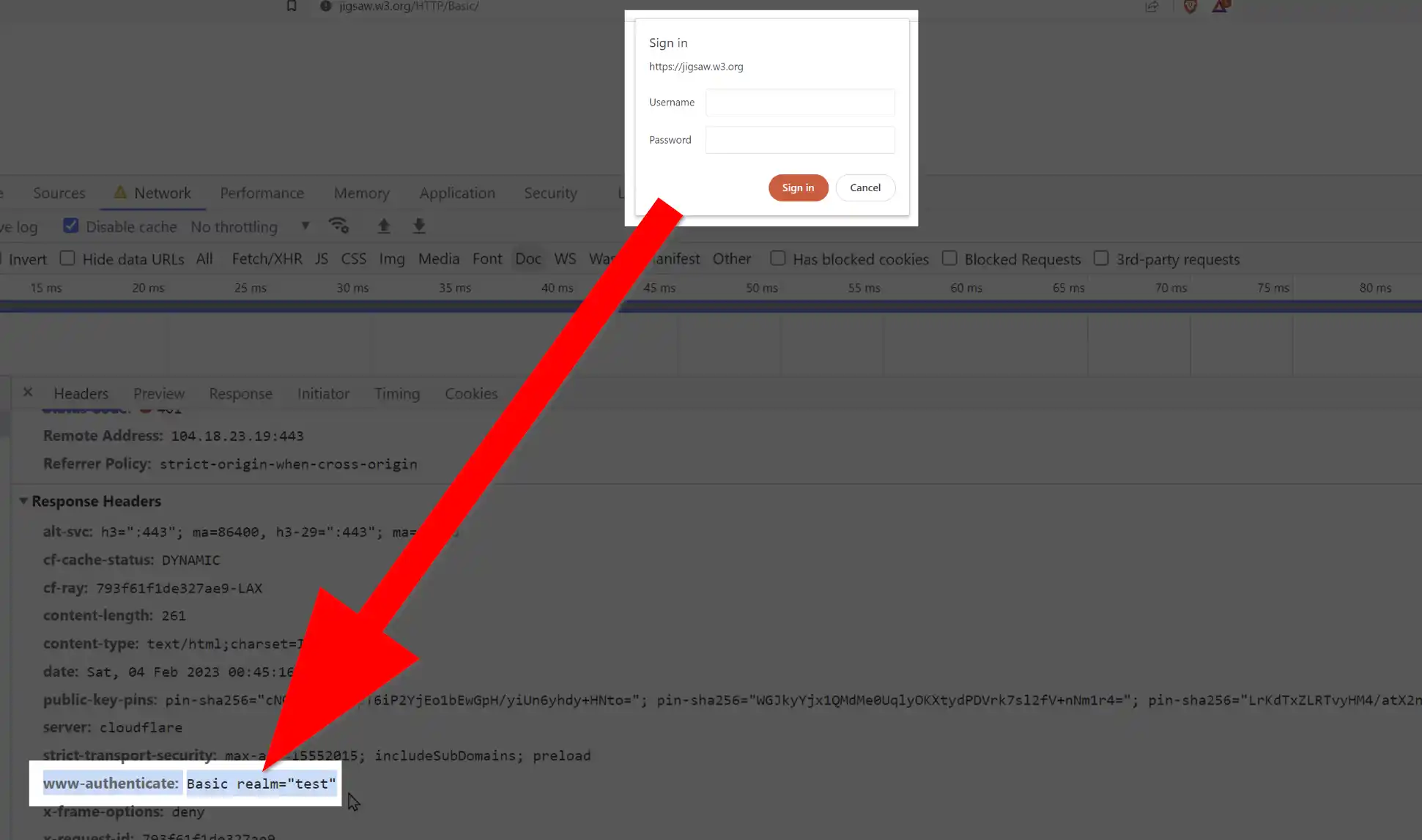
Rest Api Authentication 9 Proven Methods Setting up oauth 2.0 for your rest api involves several important steps to ensure a secure and efficient authentication system. below, we break down the key components you’ll need to implement. Therefore, a clear understanding of the available rest api authentication methods is essential for developers, founders, and product teams alike. this guide provides a comprehensive breakdown of seven primary authentication methods, designed to help you make an informed choice. In this article, we'll show you our best practices for implementing authorization in rest apis. every web api should use tls (transport layer security). tls protects the information your api sends (and the information that users send to your api) by encrypting your messages while they're in transit. Today, we’re going to cover everything you need to know about working with the most common rest api authentication methods. specfically, we're going to see how we can authenticate rest requests in budibase using: api keys in headers. api keys as query parameters. basic auth. bearer tokens. After creating a token, you can authenticate your request by sending the token in the authorization header of your request. for example, in the following request, replace your token with a reference to your token:. This lesson explains rest api authentication with basic authentication, api key authentication, and token based authentication (jwt).
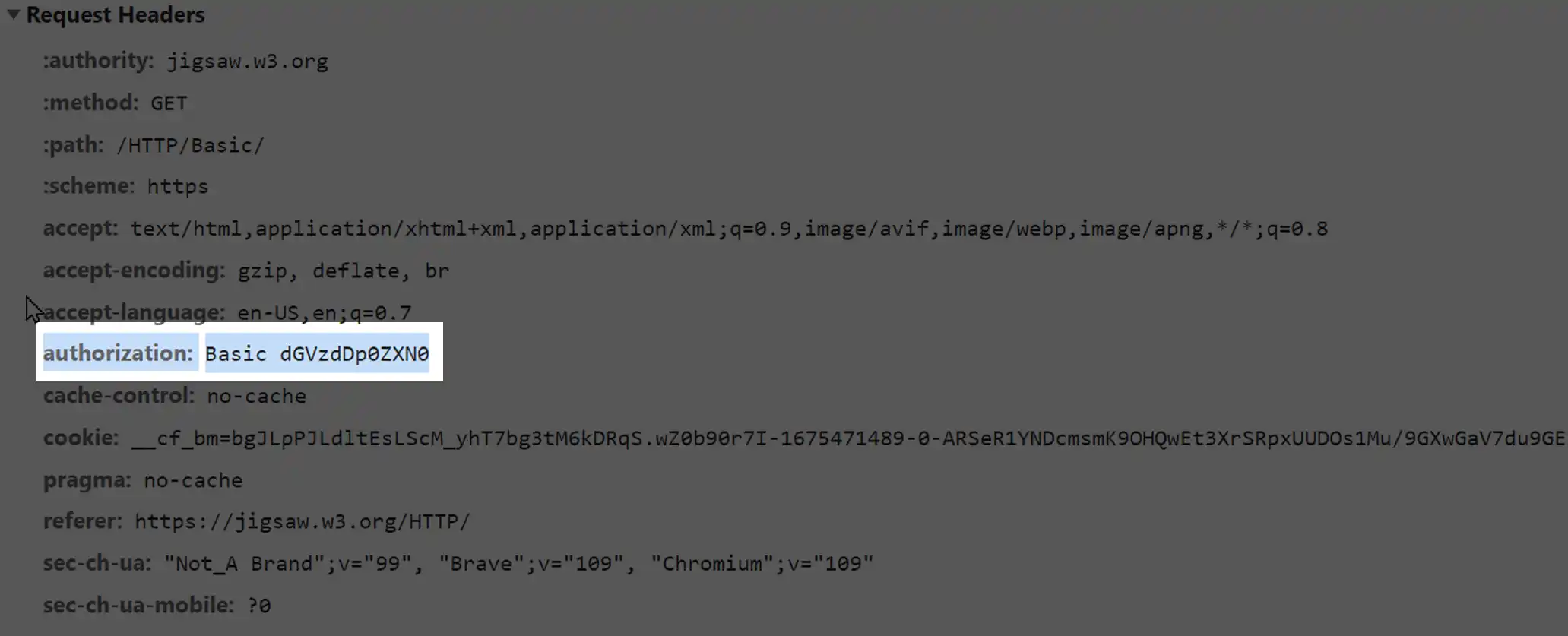
Rest Api Authentication 9 Proven Methods In this article, we'll show you our best practices for implementing authorization in rest apis. every web api should use tls (transport layer security). tls protects the information your api sends (and the information that users send to your api) by encrypting your messages while they're in transit. Today, we’re going to cover everything you need to know about working with the most common rest api authentication methods. specfically, we're going to see how we can authenticate rest requests in budibase using: api keys in headers. api keys as query parameters. basic auth. bearer tokens. After creating a token, you can authenticate your request by sending the token in the authorization header of your request. for example, in the following request, replace your token with a reference to your token:. This lesson explains rest api authentication with basic authentication, api key authentication, and token based authentication (jwt).

Rest Api Authentication Methods Figma After creating a token, you can authenticate your request by sending the token in the authorization header of your request. for example, in the following request, replace your token with a reference to your token:. This lesson explains rest api authentication with basic authentication, api key authentication, and token based authentication (jwt).
Comments are closed.