Rest Api Authentication Using External Identity Provider Api
Rest Api Authentication Using External Identity Provider Drupal Book Visual studio 2017 and asp 4.7.2 expand the security options for single page applications (spa) and web api services to integrate with external authentication services, which include several oauth openid and social media authentication services: microsoft accounts, twitter, facebook, and google. Drupal api authentication using an external identity provider involves the use of tokens received from third party providers like google, azure ad, keycloak, okta, gitlab, etc. for accessing drupal rest apis securely.
Rest Api Authentication Using External Identity Provider Drupal Book Entra authenticates the user and returns an access token. the frontend sends the token to the backend api in the authorization header. the backend validates the token using entra’s jwks. To create an external auth identity provider, you must also use the post method with the named credentials external auth identity provider credentials fullname resource to populate the identity provider's credentials. Api center integrates with external identity providers, such as okta or azure active directory (aad) to verify users' identities and grant them access to protected resources. To use the rest api, you'll need an identity platform api key. to obtain a key: go to the identity providers page in the google cloud console. click application setup details. copy.
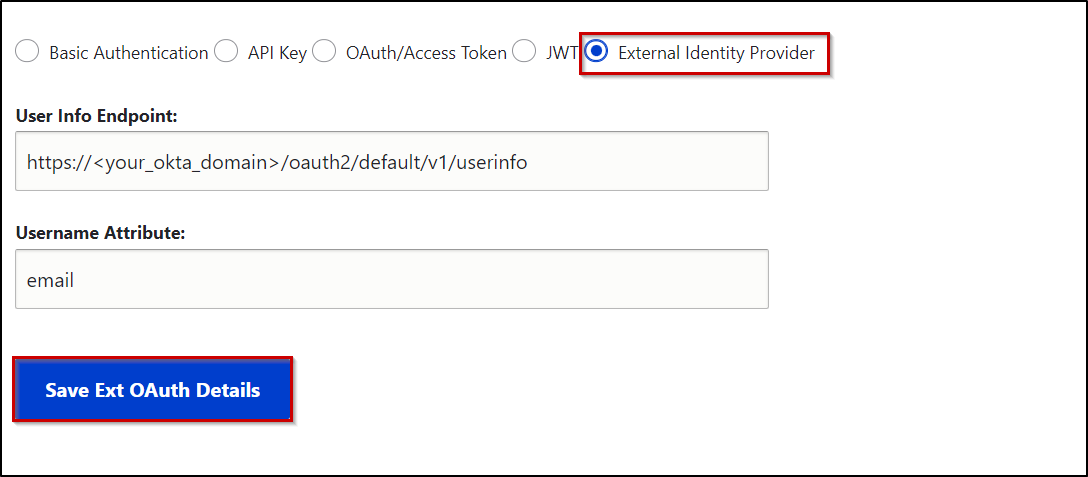
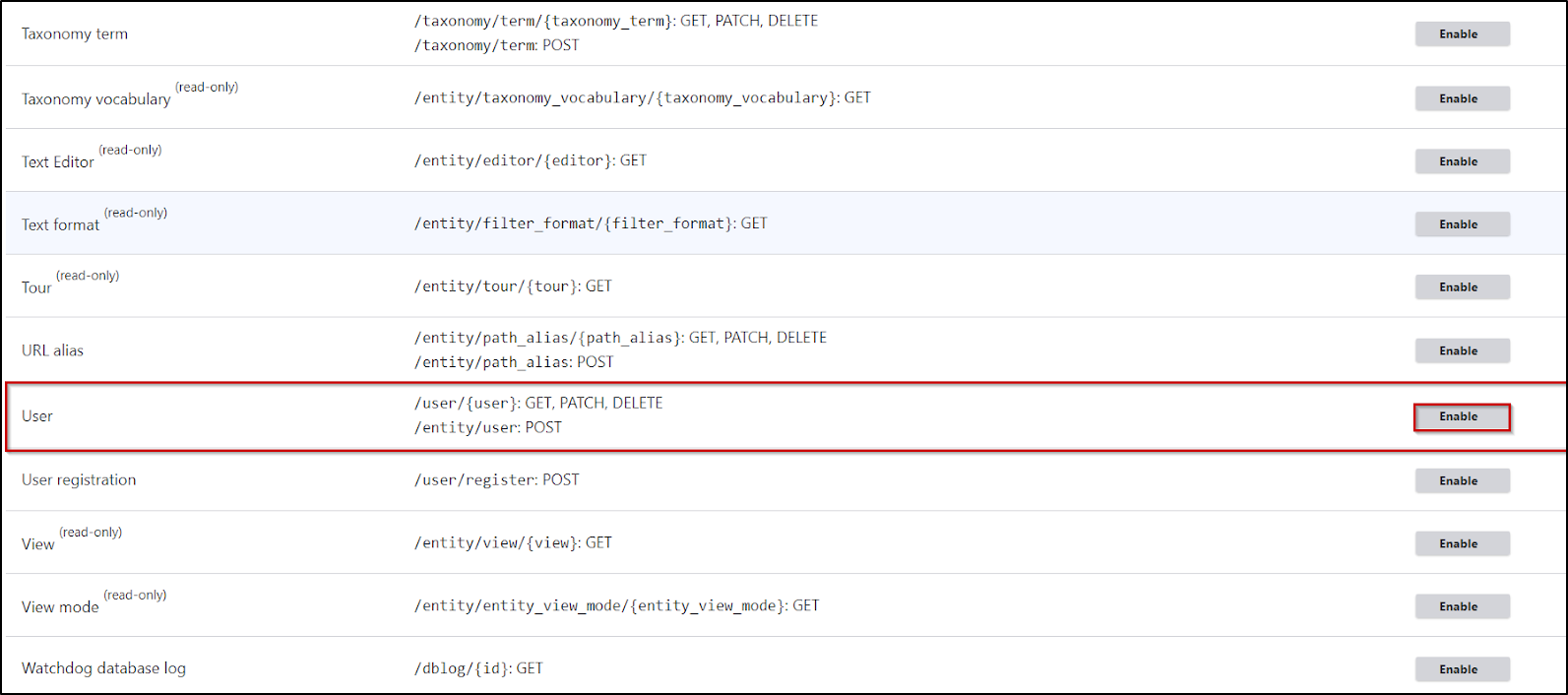
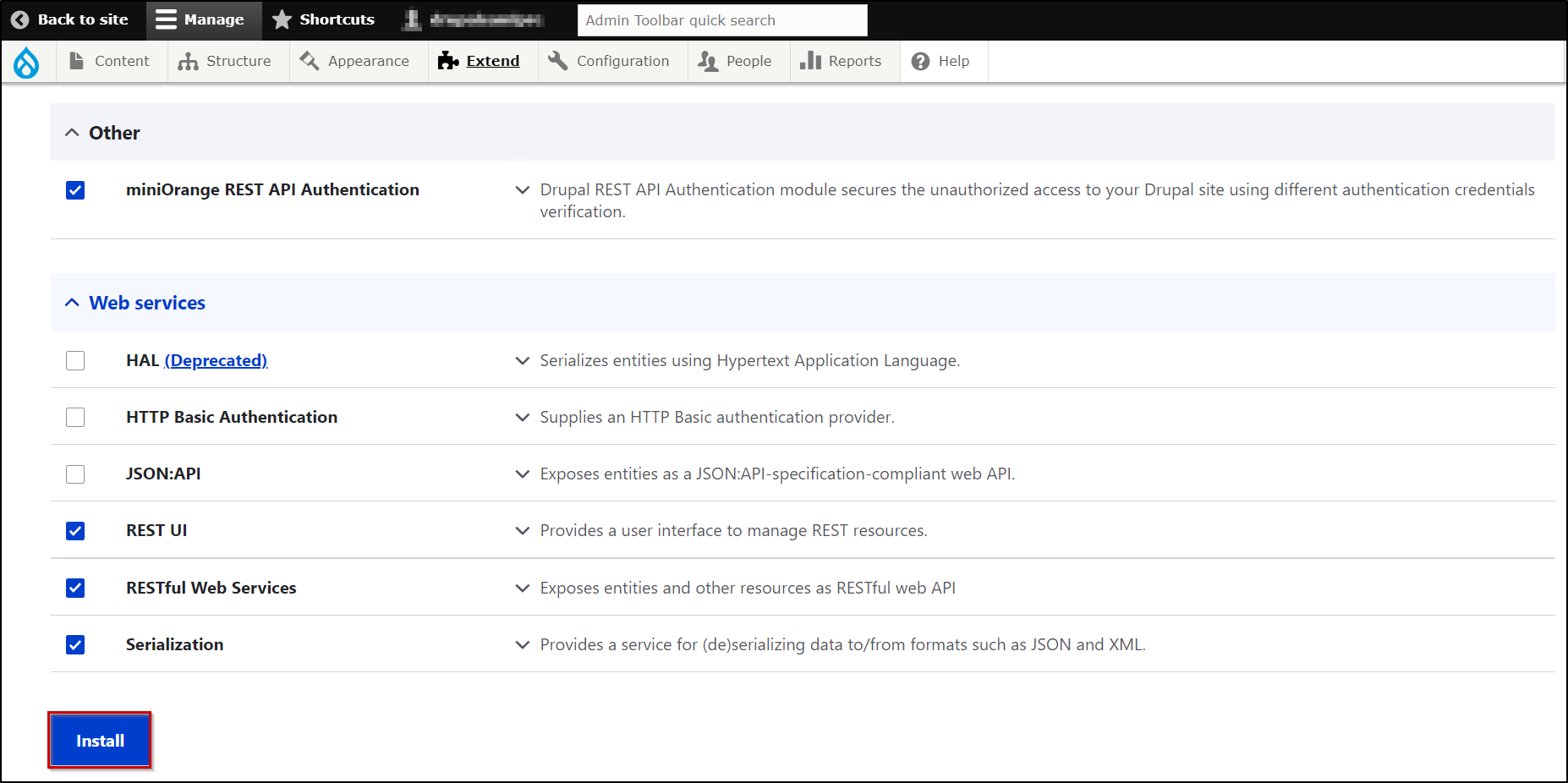
Rest Api Authentication Using External Identity Provider Drupal Book Api center integrates with external identity providers, such as okta or azure active directory (aad) to verify users' identities and grant them access to protected resources. To use the rest api, you'll need an identity platform api key. to obtain a key: go to the identity providers page in the google cloud console. click application setup details. copy. I'll still take a closer look on how to handle external authentication with it, it may be worth it in the end. what's the main reason behind not recommending the api to handle external auth?. In my java web app, i know that i can retrieve access token directly from the external oidc provider, then use the access token to go with subsequent rest api calls to servicenow. The external identity provider authentication method allows you to secure and restrict access to your drupal rest apis using tokens from third party providers such as google, azure ad, keycloak, okta, or gitlab. For your implementation, you can either extract the user id from the sub claim in the id token, or call the userinfo endpoint of the authentication api and extract it from the user id response property.
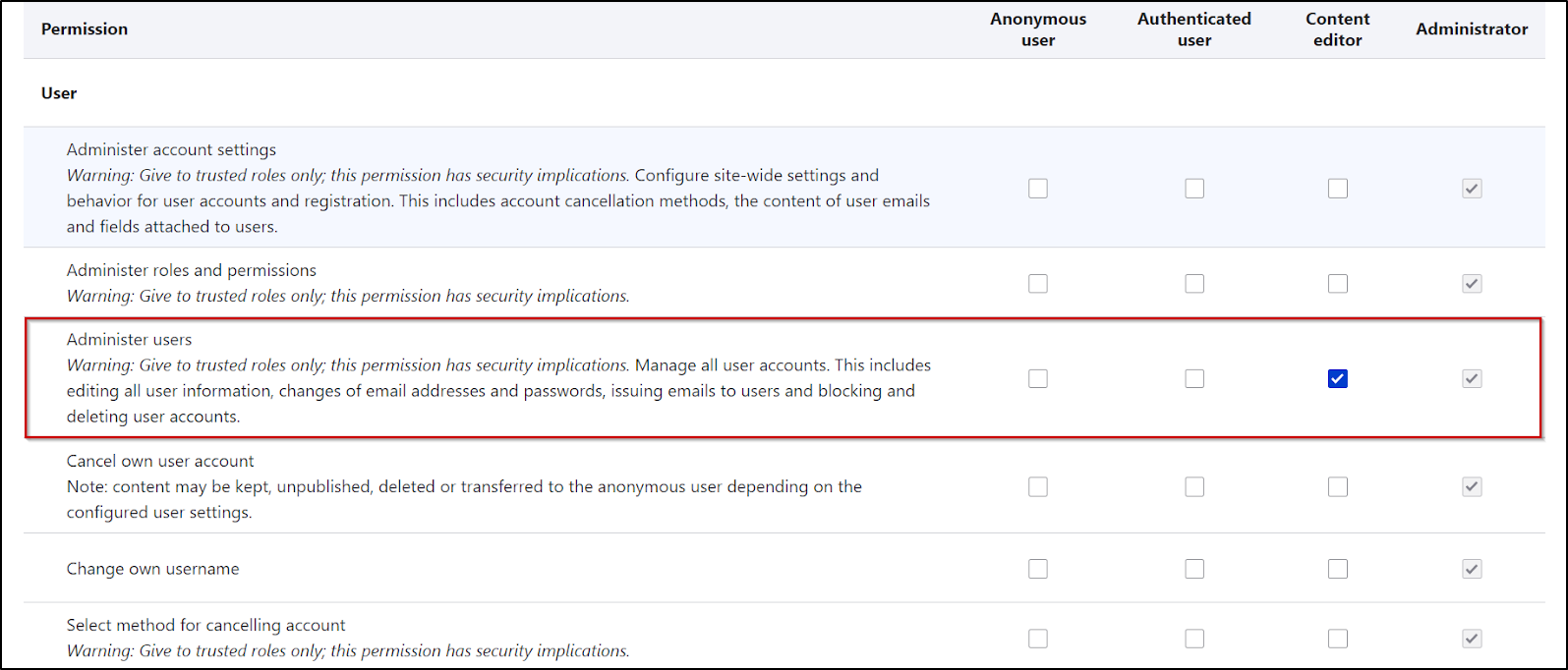
Rest Api Authentication Using External Identity Provider Drupal Book I'll still take a closer look on how to handle external authentication with it, it may be worth it in the end. what's the main reason behind not recommending the api to handle external auth?. In my java web app, i know that i can retrieve access token directly from the external oidc provider, then use the access token to go with subsequent rest api calls to servicenow. The external identity provider authentication method allows you to secure and restrict access to your drupal rest apis using tokens from third party providers such as google, azure ad, keycloak, okta, or gitlab. For your implementation, you can either extract the user id from the sub claim in the id token, or call the userinfo endpoint of the authentication api and extract it from the user id response property.

Rest Api Authentication Using External Identity Provider Api The external identity provider authentication method allows you to secure and restrict access to your drupal rest apis using tokens from third party providers such as google, azure ad, keycloak, okta, or gitlab. For your implementation, you can either extract the user id from the sub claim in the id token, or call the userinfo endpoint of the authentication api and extract it from the user id response property.

Rest Api Authentication Using External Identity Provider Api
Comments are closed.