Remote Access Trojan Definition And Risks

Remote Access Trojan Rat Cyberhoot A remote access trojan (rat) provides the perpetrator remote access and control of the infected computer. discover how to detect and protect from rat infection. A remote access trojan (rat) is a type of trojan cyberattack that gives a hacker remote access to your device. disguised as a harmless file or application, a rat opens a backdoor to your device via a network, putting your data, security, and identity at risk.

What Is A Remote Access Trojan Definition Examples Vade Learn what a remote access trojan is, how rats work, the risks they pose, and how to protect against infections. we cover the basics, examine real incidents where websites spread rat infections, and provide practical advice for securing your devices against a rat. In this guide, we’ll explore how a remote access trojan works, the types of criminal activity that they’re used for, and what you can do to prevent remote hacking and rat malware from affecting your devices and data. What is a remote access trojan (rat)? a remote access trojan is malware that hides itself as a legitimate program or file to fool users into downloading it. after installation, it provides the attackers with remote access to the infected machine. Criminals can control your computer or phone using a program called remote access trojans, but you can prevent, detect, and come back from rat attacks.

Remote Access Trojan What is a remote access trojan (rat)? a remote access trojan is malware that hides itself as a legitimate program or file to fool users into downloading it. after installation, it provides the attackers with remote access to the infected machine. Criminals can control your computer or phone using a program called remote access trojans, but you can prevent, detect, and come back from rat attacks. Get everything you need to know about remote access trojans (rat) from what are they, the history of rat, common infection methods, how to remove them & much more. Learn what a remote access trojan (rat) is, how it works, why it’s dangerous, and how to protect your digital life. In this blog post, we'll dive into everything you need to know about rats – what is remote access trojan (rat) in cybersecurity, their functionality, risks and dangers, common uses, and targets, as well as how to detect and prevent them from infecting your device. What is a remote access trojan (rat)? a remote access trojan (rat) is malicious software that gives attackers complete control over a victim's computer system. these malware programs often enter systems through email attachments, infected downloads, or fake software updates.
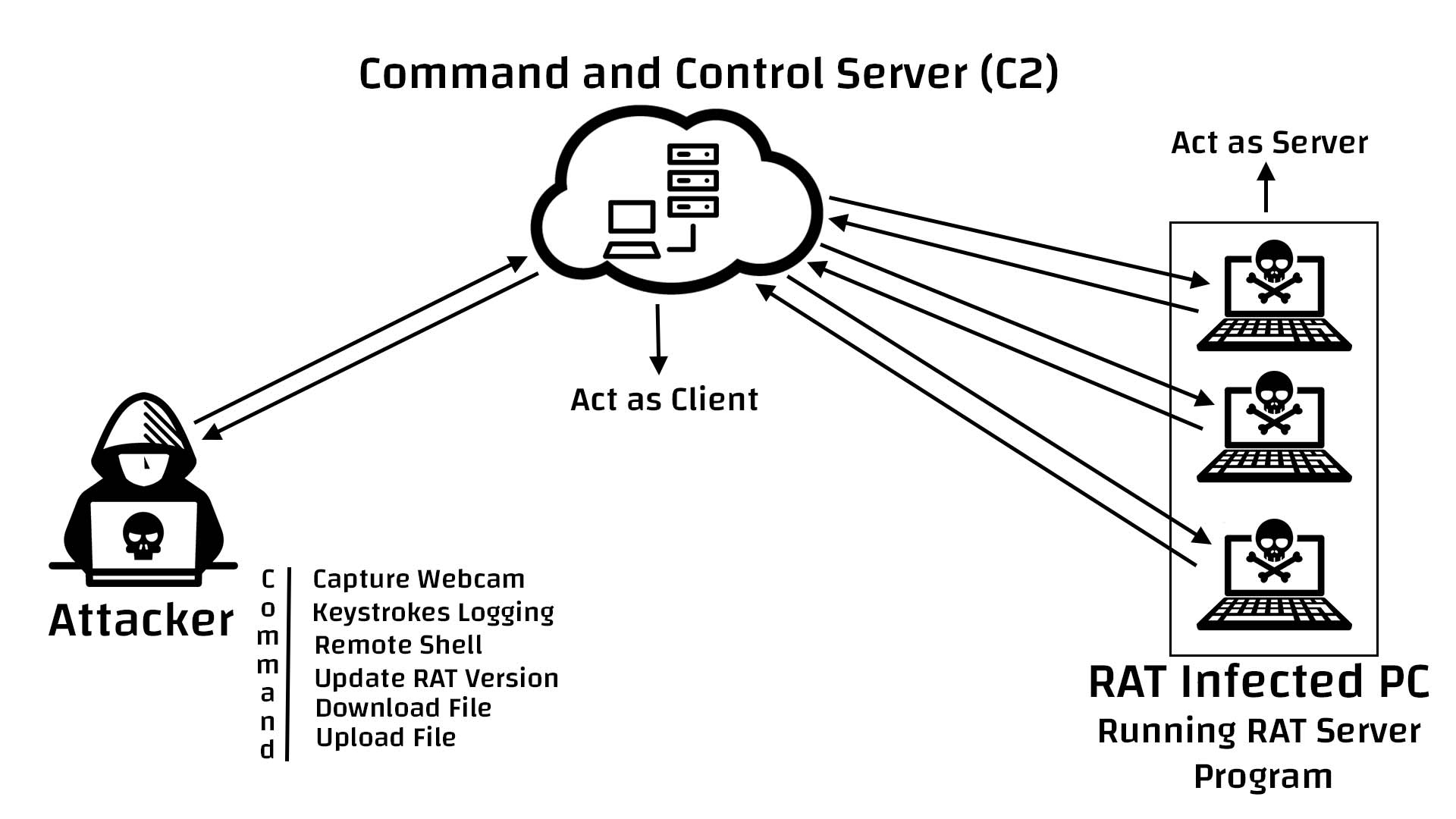
What Is Remote Access Trojan Hackers Terminal Get everything you need to know about remote access trojans (rat) from what are they, the history of rat, common infection methods, how to remove them & much more. Learn what a remote access trojan (rat) is, how it works, why it’s dangerous, and how to protect your digital life. In this blog post, we'll dive into everything you need to know about rats – what is remote access trojan (rat) in cybersecurity, their functionality, risks and dangers, common uses, and targets, as well as how to detect and prevent them from infecting your device. What is a remote access trojan (rat)? a remote access trojan (rat) is malicious software that gives attackers complete control over a victim's computer system. these malware programs often enter systems through email attachments, infected downloads, or fake software updates.
Remote Access Trojan Rat Rat Malware Rat Trojans Gridinsoft Blog In this blog post, we'll dive into everything you need to know about rats – what is remote access trojan (rat) in cybersecurity, their functionality, risks and dangers, common uses, and targets, as well as how to detect and prevent them from infecting your device. What is a remote access trojan (rat)? a remote access trojan (rat) is malicious software that gives attackers complete control over a victim's computer system. these malware programs often enter systems through email attachments, infected downloads, or fake software updates.
Comments are closed.