Registry Modification With Real Time Response
Mitre Registry Modification At Louise Costa Blog In this video, we will demonstrate how crowdstrike's real time response feature can modify the registry after changes made during an attack. more. Modify registry adversaries may interact with the windows registry as part of a variety of other techniques to aid in defense evasion, persistence, and execution. access to specific areas of the registry depends on account permissions, with some keys requiring administrator level access.
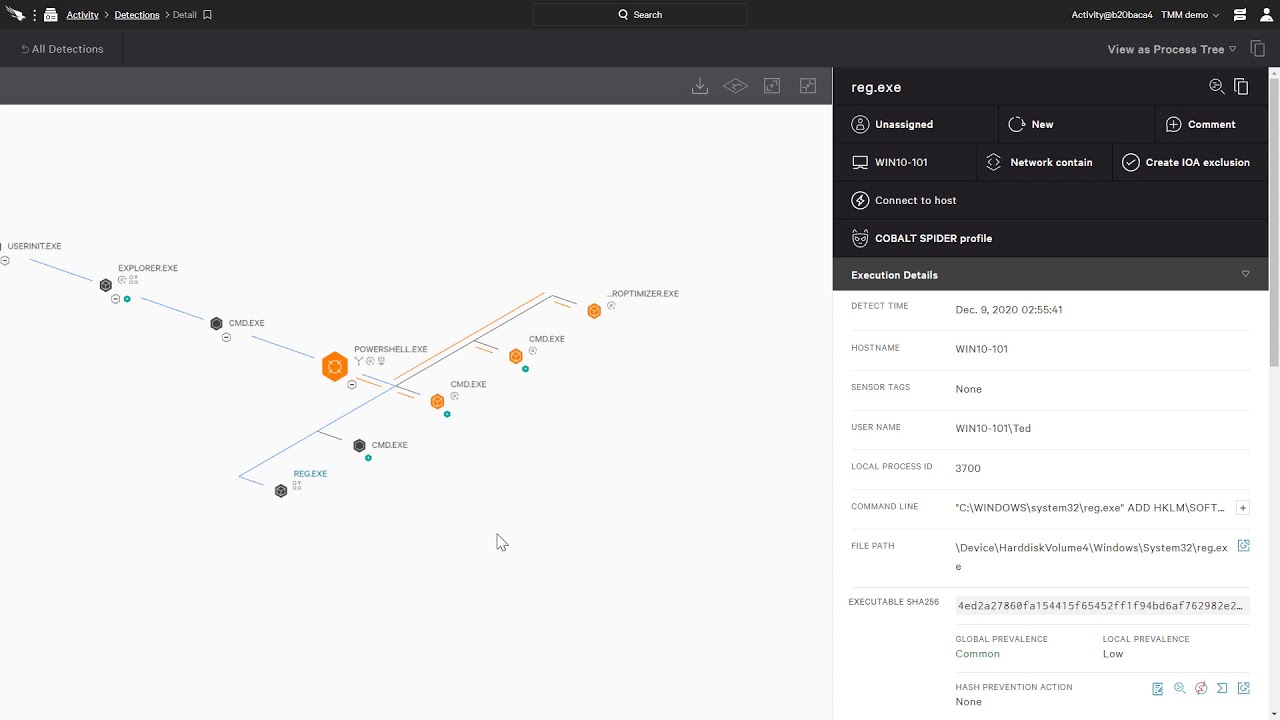
Mitre Registry Modification At Louise Costa Blog Set real time triggers looking for changes to file system or registry in your security tools. tune end point monitoring or hips to look for telltale signs of file replacement and registry modification. want to try it yourself? download the latest version of crowdresponse here. In those 11 minutes they quietly modified 6 registry keys disabling windows defender real time protection, turning off tamper protection, clearing the event log maximum size, and disabling. Mitre tracks windows registry (ds0024) as a data source for observing registry modification. windows supports native registry monitoring through the application of system access control lists (sacl), which will log registry modification events as event id 4657. The script essentially turns your powershell session into a registry change detector that’s both efficient and responsive, exactly what event driven architecture is all about!.
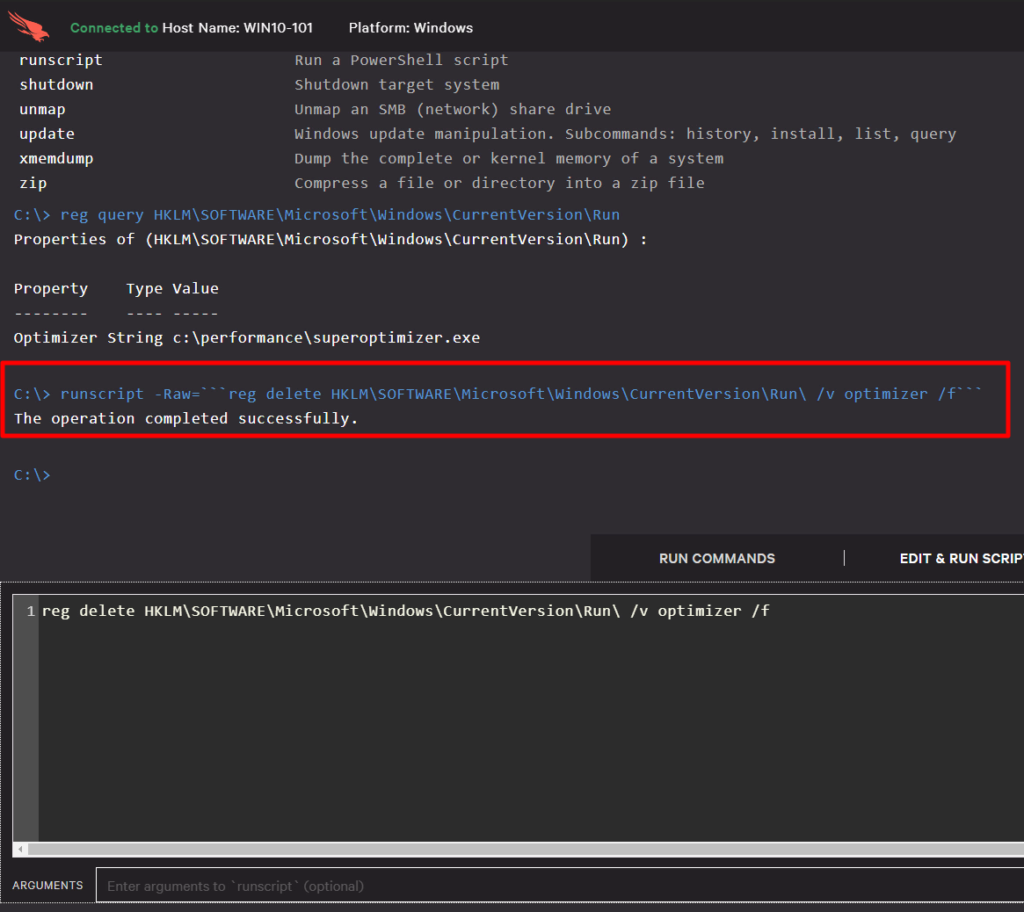
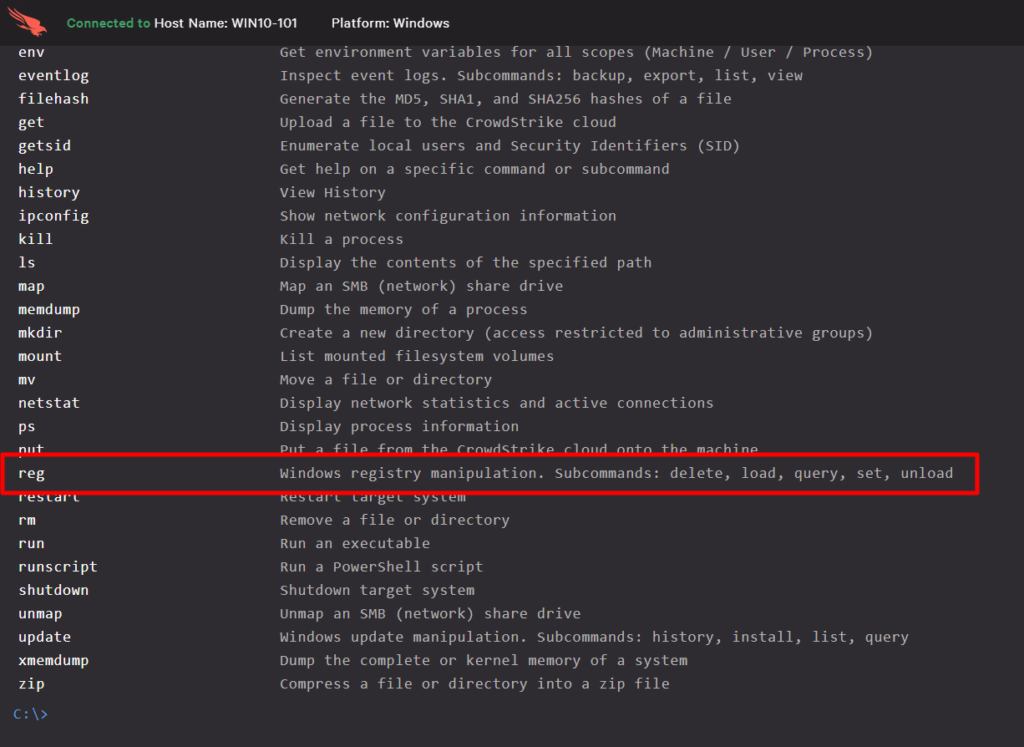
Mitre Registry Modification At Louise Costa Blog Mitre tracks windows registry (ds0024) as a data source for observing registry modification. windows supports native registry monitoring through the application of system access control lists (sacl), which will log registry modification events as event id 4657. The script essentially turns your powershell session into a registry change detector that’s both efficient and responsive, exactly what event driven architecture is all about!. Adversaries may interact with the windows registry to hide configuration information within registry keys, remove information as part of cleaning up, or as part of other techniques to aid in persistence and execution. If you're worked in dfir or threat intel for any amount of time, you've likely either seen or heard how threat actors modify systems to meet their own needs, configuring systems to provide data or hide their activities, as they make their way through an infrastructure. Learn about common commands used in live response and see examples on how they're typically used. depending on the role you have, you can run basic or advanced live response commands. Welcome to the crowdstrike subreddit. crowdstrike falcon offers cloud delivered solutions across endpoints, cloud workloads, identity and data; providing responders remote visibility across the enterprise and enabling instant access to the "who, what, when, where, and how" of a cyber attack.
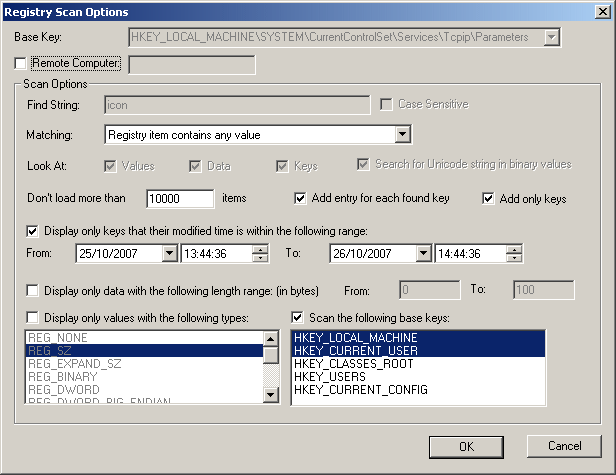
Viewing The List Of Registry Keys Modified In The Last Hours Days Adversaries may interact with the windows registry to hide configuration information within registry keys, remove information as part of cleaning up, or as part of other techniques to aid in persistence and execution. If you're worked in dfir or threat intel for any amount of time, you've likely either seen or heard how threat actors modify systems to meet their own needs, configuring systems to provide data or hide their activities, as they make their way through an infrastructure. Learn about common commands used in live response and see examples on how they're typically used. depending on the role you have, you can run basic or advanced live response commands. Welcome to the crowdstrike subreddit. crowdstrike falcon offers cloud delivered solutions across endpoints, cloud workloads, identity and data; providing responders remote visibility across the enterprise and enabling instant access to the "who, what, when, where, and how" of a cyber attack.
Comments are closed.