Reflected Xss In Facebook Twitter Google Training Platforms Bug Bounty Case Study
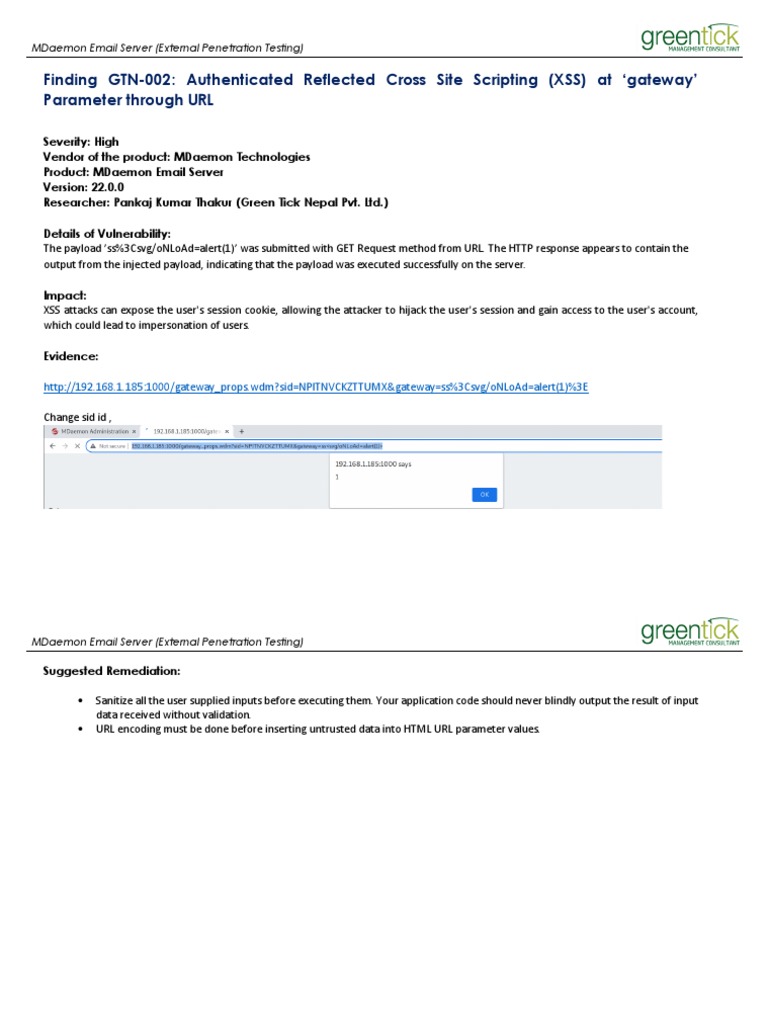
Authenticated Reflected Cross Site Scripting Xss At Gateway Pdf In this article, we analyze a reflected cross site scripting (xss) vulnerability discovered in the training platforms of major technology companies including facebook blueprint,. In this video, we explore a real bug bounty case where a reflected cross site scripting (xss) vulnerability was discovered in the training platforms of major.
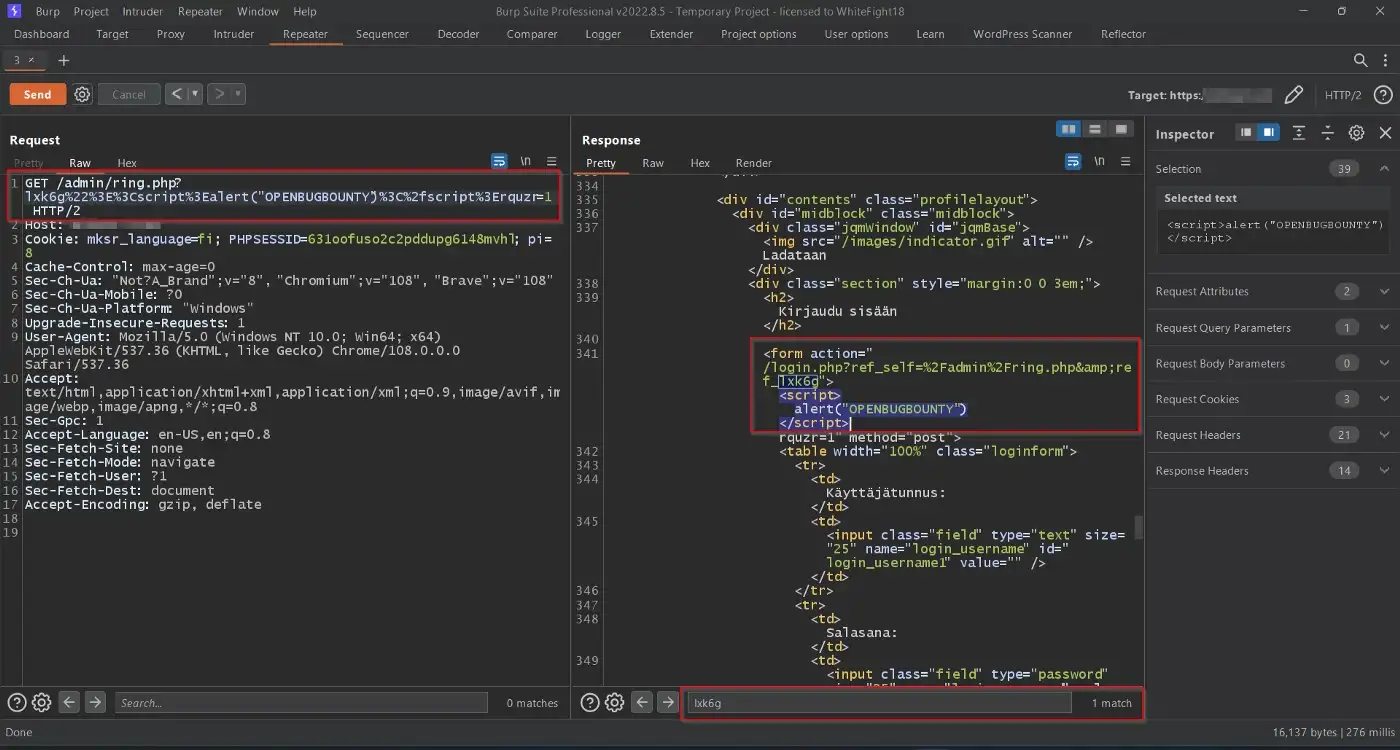
How I Got My First Reflected Xss Bug Bounty Hacklido 🚨 new video reflected xss vulnerability discovered in facebook, twitter & google training platforms. I would like to thanks twitter security team for rewarding me with that bounty, thank you guys for your generosity. also a special thanks to facebook security team for rewarding me with that great bounty, thank you guys ;). In this video, we explore a real bug bounty case where a reflected cross site scripting (xss) vulnerability was discovered in the training platforms of major. Reflected xss in facebook, twitter & google training platforms | bug bounty case study 536 views 1 day ago 14:07.
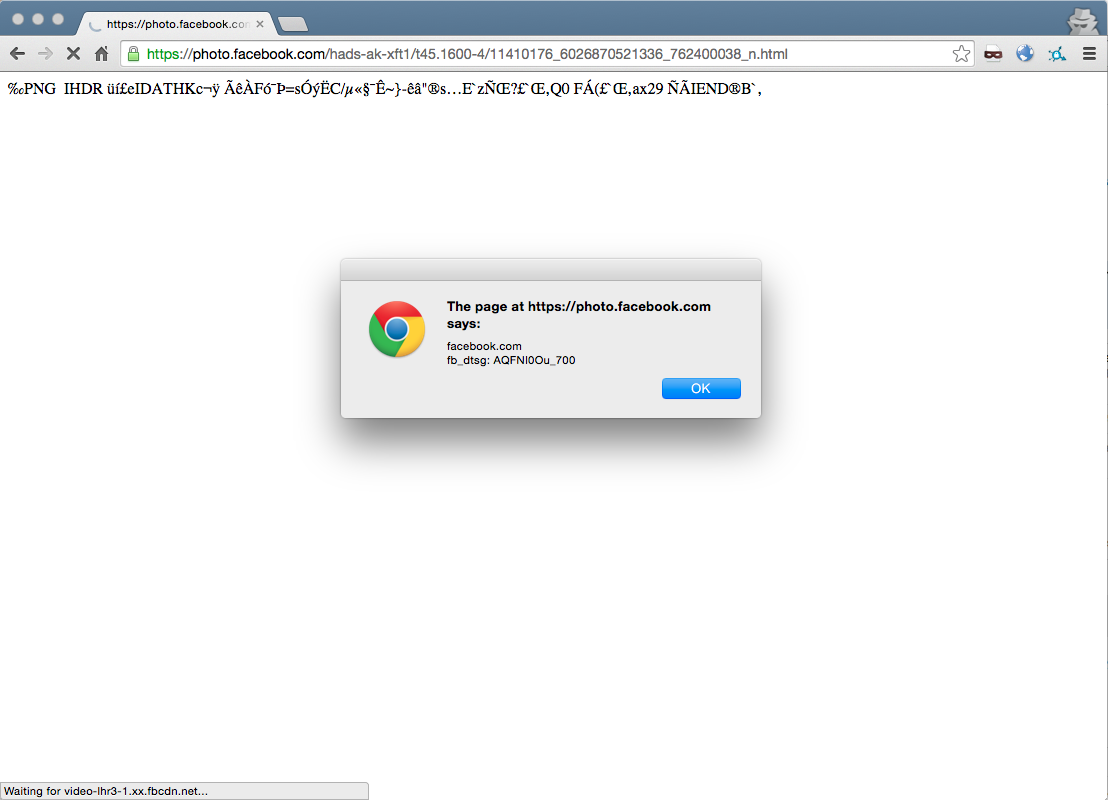
Facebook Patches Critical Xss Bug That Led To Total Account Compromise In this video, we explore a real bug bounty case where a reflected cross site scripting (xss) vulnerability was discovered in the training platforms of major. Reflected xss in facebook, twitter & google training platforms | bug bounty case study 536 views 1 day ago 14:07. Collection of facebook bug bounty writeups. contribute to jaiswalakshansh facebook bugbounty writeups development by creating an account on github. In this article, we dissect a real world xss bug bounty case where a security researcher discovered a flaw with a minimal payout—highlighting the challenges and automation techniques in modern bug hunting. Owasp description: cross site scripting (xss) attacks are a type of injection and malicious scripts are injected into otherwise benign and trusted websites. Each one breaks down a disclosed bug bounty writeup focused on a specific bug class. you’ll see how top hackers approach targets, chain bugs, and write reports that get rewarded.
Comments are closed.