Red Teaming Explained In 8 Minutes

Red Teaming Ciberon Stop playing wow and join tryhackme: tryhackme ?utm source= &utm medium=social&utm campaign=madhat ia 21febpatreon if you wanna click stuff. This content offers a realistic deep dive into red teaming, clarifying that it is adversary emulation, not just penetration testing. learn the technical chaos, from reconnaissance and c2 frameworks to defense evasion and physical red teaming.
Red Teaming Ciberon When we talk about cybersecurity, it’s easy to throw around terms like “pentesting,” “vulnerability scans,” or “red teaming” as if they mean the same thing. but in reality, each represents a. Red teaming is something that takes a bit of experience to actually nail. it's not something you expect to walk into after doing a four year uni course or something to pick up with little to no actual security experience. Learn everything you need to know about red teaming or red team hacking in our guide made for absolute beginners. read now. What is red teaming? red teaming in the context of cybersecurity is the process through which an organization assesses its cybersecurity stances using techniques and methods that mimic real life adversaries.
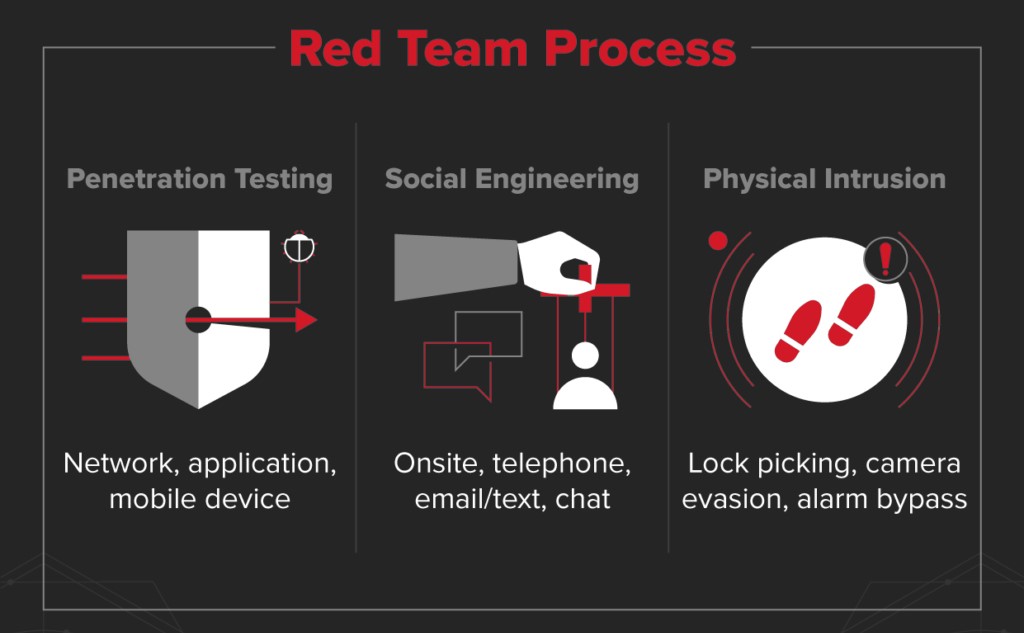
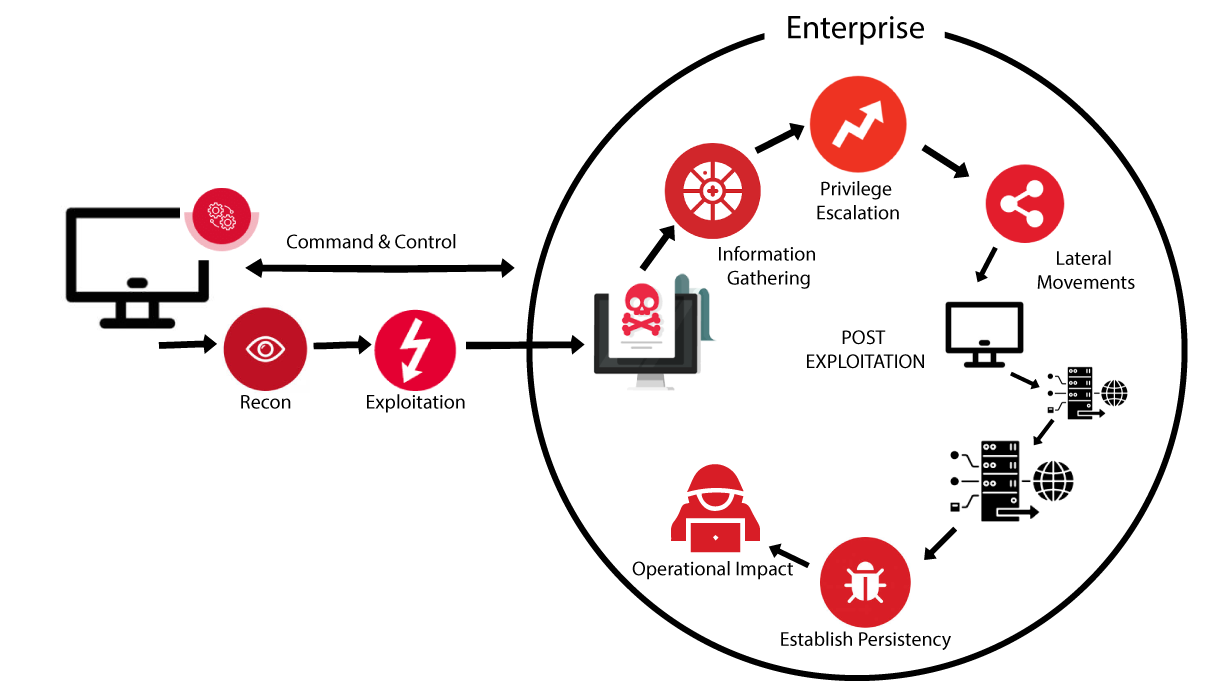
Red Teaming Isec Services And Products Learn everything you need to know about red teaming or red team hacking in our guide made for absolute beginners. read now. What is red teaming? red teaming in the context of cybersecurity is the process through which an organization assesses its cybersecurity stances using techniques and methods that mimic real life adversaries. Red teaming relies on a structured methodology to deliver outcomes that reflect real world threats and business impact. when organizations follow a defined process, they move beyond one off checks and create a security assessment that maps closely to actual attacker behavior. Discover how cybersecurity teams can mimic real cyber threats with a proper red team strategy. What is red teaming? definition: red teaming is the process of using tactics, techniques, and procedures (ttps) to emulate a real world threat with the goals of training and measuring the effectiveness of the people, processes, and technology used to defend an environment. Discover the essentials of red teaming, its importance, methodologies, and how it strengthens your cybersecurity defenses effectively.

Red Teaming Devoteam Cyber Trust Red teaming relies on a structured methodology to deliver outcomes that reflect real world threats and business impact. when organizations follow a defined process, they move beyond one off checks and create a security assessment that maps closely to actual attacker behavior. Discover how cybersecurity teams can mimic real cyber threats with a proper red team strategy. What is red teaming? definition: red teaming is the process of using tactics, techniques, and procedures (ttps) to emulate a real world threat with the goals of training and measuring the effectiveness of the people, processes, and technology used to defend an environment. Discover the essentials of red teaming, its importance, methodologies, and how it strengthens your cybersecurity defenses effectively.

Red Teaming Services Pentesys What is red teaming? definition: red teaming is the process of using tactics, techniques, and procedures (ttps) to emulate a real world threat with the goals of training and measuring the effectiveness of the people, processes, and technology used to defend an environment. Discover the essentials of red teaming, its importance, methodologies, and how it strengthens your cybersecurity defenses effectively.
Comments are closed.