Recognizing And Combating Mobile Phishing Attacks

Combating Phishing Attacks Through Awareness And Simulation Cybernews Learn how to spot and avoid mobile phishing scams with expert tips. protect your personal data and stay safe from online threats. Briefly, the results of the study show that the mitigation strategies against phishing attacks can be classified mainly into three categories namely, (1) anti phishing systems, (2) models and frameworks, and (3) human centric mitigation strategies.

Protecting Your Company From Mobile Phishing Attacks These phishing protection tips will help you stay safer online, teach you the signs of phishing, and what to do if you see it. We'll discuss best practices for preventing phishing attacks, including user awareness training, implementing mfa, and conducting periodic phishing attack tests. Scammers use email or text messages to trick you into giving them your personal and financial information. but there are several ways to protect yourself. scammers use email or text messages to try to steal your passwords, account numbers, or social security numbers. Learn all about the rise of mobile phishing attacks and expert tips to safeguard your devices. stay ahead of mobile phishing with our prevention guide.
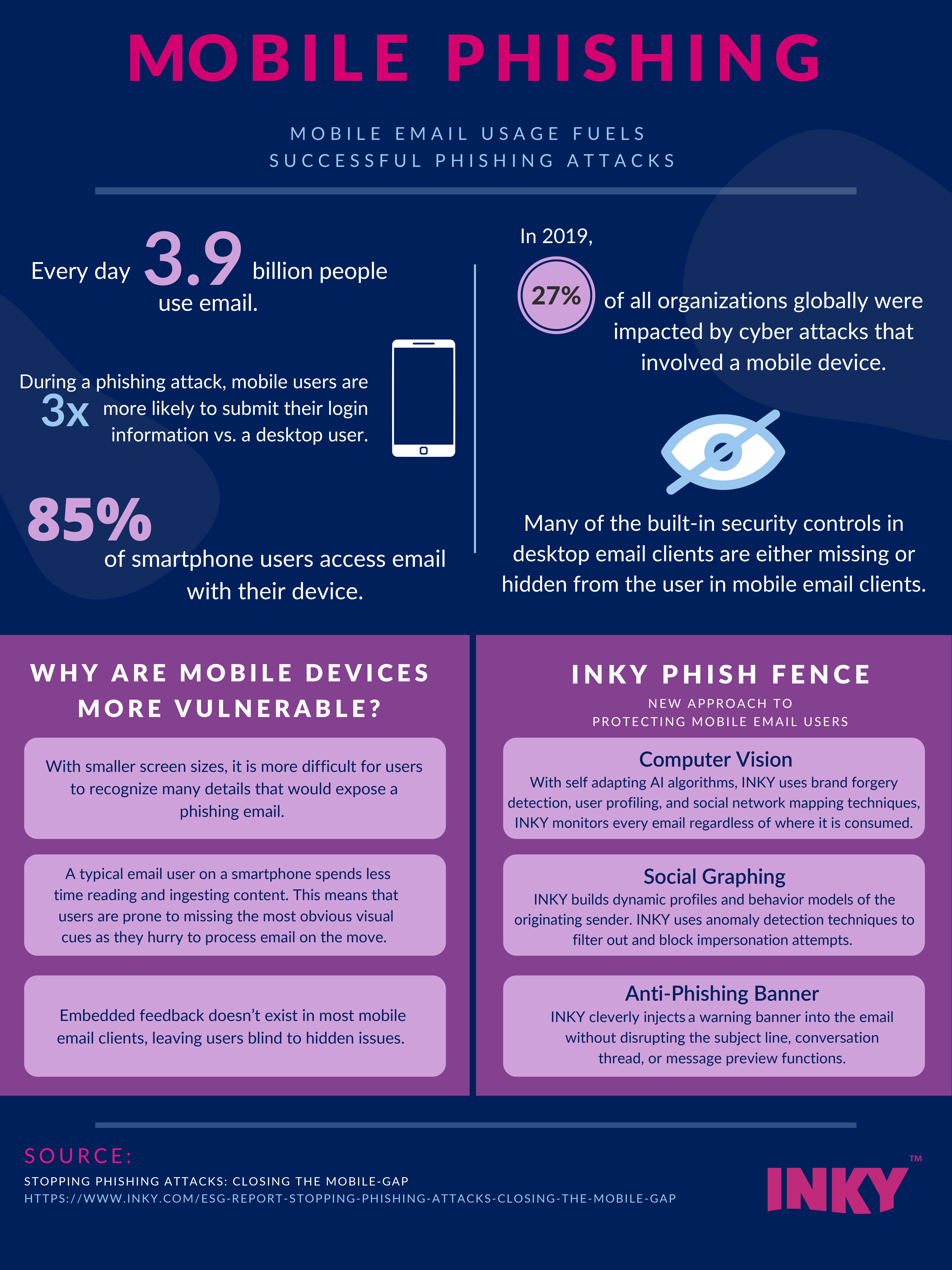
Infographic Mobile Phishing Attacks Scammers use email or text messages to trick you into giving them your personal and financial information. but there are several ways to protect yourself. scammers use email or text messages to try to steal your passwords, account numbers, or social security numbers. Learn all about the rise of mobile phishing attacks and expert tips to safeguard your devices. stay ahead of mobile phishing with our prevention guide. How to identify phishing attacks and how to prevent them? this blog provides 10 different ways to avoid phishing attacks. The phishing attack landscape continues to evolve in 2025, with cybercriminals using more sophisticated techniques to bypass security measures, emphasizing the need for phishing attack prevention. Phishing occurs when criminals try to get us to open harmful links, emails or attachments that could request our personal information or infect our devices. phishing messages or “bait” usually come in the form of an email, text, direct message on social media or phone call. Phishing attacks can be delivered in many ways, but they all play on trust, urgency and other aspects of human psychology. fear, excitement, authority, curiosity and trust could all be reactions to a phishing message.

Phishing Attacks Are Evolving Is Your Mobile Phone Safe Techynerd How to identify phishing attacks and how to prevent them? this blog provides 10 different ways to avoid phishing attacks. The phishing attack landscape continues to evolve in 2025, with cybercriminals using more sophisticated techniques to bypass security measures, emphasizing the need for phishing attack prevention. Phishing occurs when criminals try to get us to open harmful links, emails or attachments that could request our personal information or infect our devices. phishing messages or “bait” usually come in the form of an email, text, direct message on social media or phone call. Phishing attacks can be delivered in many ways, but they all play on trust, urgency and other aspects of human psychology. fear, excitement, authority, curiosity and trust could all be reactions to a phishing message.
Comments are closed.