Rdp Security Risks How To Detect Attacks
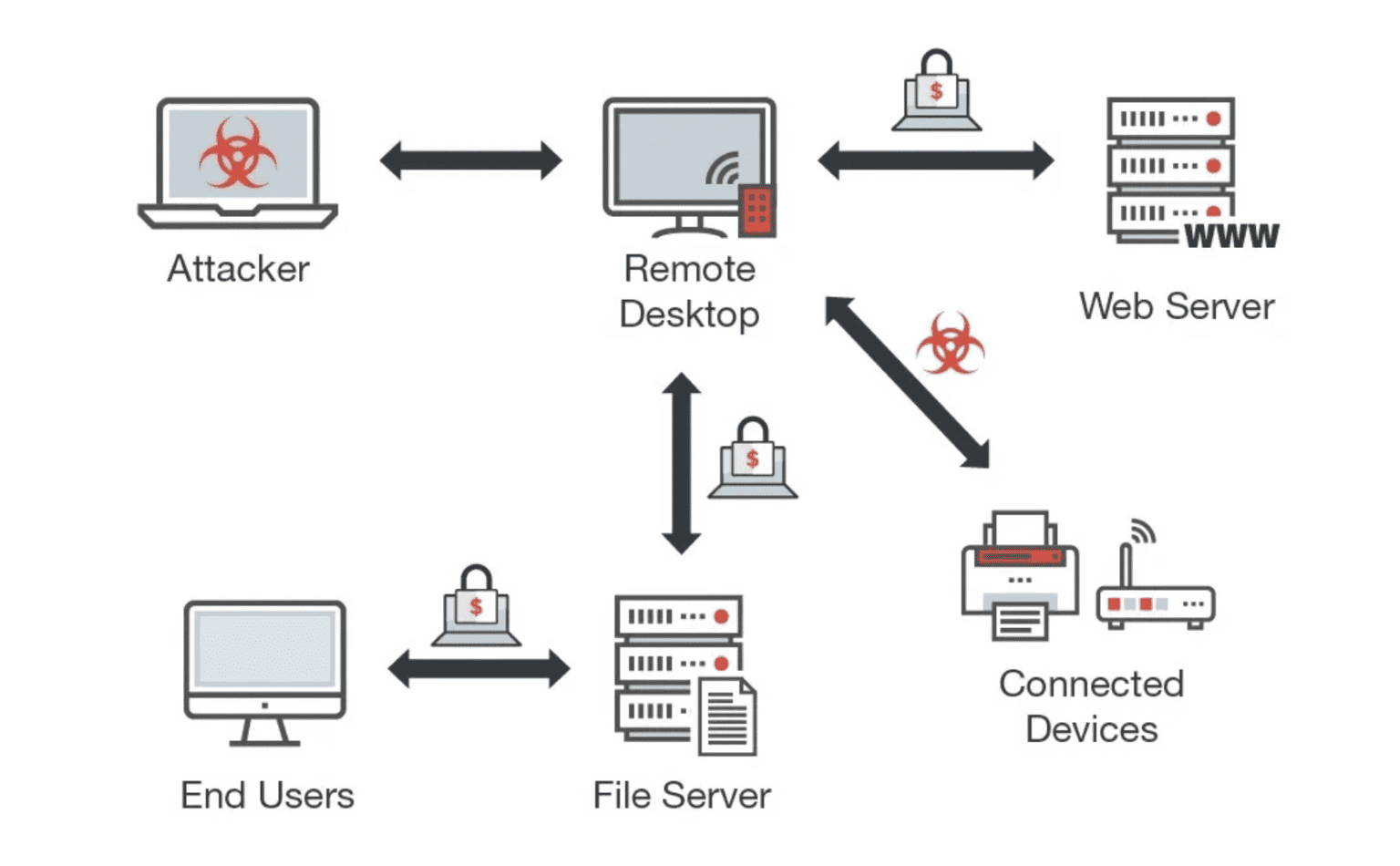
Addressing Remote Desktop Attacks And Security Esecurity Planet The remote desktop protocol (rdp) is a powerful tool, but it opens the door to attackers. learn the signs of an rdp attack and how to detect them. Remote desktop protocol attacks (rdp) can limit access and lock out users from systems. learn how to prevent rdp attacks in this guide.

Rdp Server Security Risks And The Best Practices For Addressing Them Rdp security is a crucial area of concern for companies with remote workforces. learn how to defend against rdp vulnerability exploits and secure remote access. Learn the top remote desktop protocol (rdp) security risks and how to prevent attacks with best practices, tools, and expert cybersecurity strategies. In this guide, we break down the most common remote access vulnerabilities, how attackers exploit them, and the specific steps you can take to secure your environment and prevent rdp based ransomware attacks. Cybercriminals are increasingly targeting remote desktop protocols (rdp), leading to data breaches, ransomware attacks, and unauthorized access to sensitive information. to protect against these threats, organizations must adopt secure remote access practices.

Rdp Attacks Decline 89 In Eight Months Infosecurity Magazine In this guide, we break down the most common remote access vulnerabilities, how attackers exploit them, and the specific steps you can take to secure your environment and prevent rdp based ransomware attacks. Cybercriminals are increasingly targeting remote desktop protocols (rdp), leading to data breaches, ransomware attacks, and unauthorized access to sensitive information. to protect against these threats, organizations must adopt secure remote access practices. In this comprehensive rdp security guide, you’ll discover the most effective ways to secure your rdp sessions, prevent unauthorized access, and reduce rdp vulnerabilities—whether you’re working from the cloud, on premises, or a hybrid environment. Learn the risks of internet exposed remote desktop protocol (rdp), steps to provide secure remote access, and what coalition scan data shows about the risk. Cis guide explains how best to secure remote desktop protocol (rdp) to protect and defend against the most pervasive cyber threats that are faced today. Learn how to prevent rdp brute force attacks with vpn, mfa, nla, account lockouts, and monitoring. secure your rdp access in 8 steps.

Hackers Leverage Red Team Tools In Rdp Attacks Via Tor Vpn For Data In this comprehensive rdp security guide, you’ll discover the most effective ways to secure your rdp sessions, prevent unauthorized access, and reduce rdp vulnerabilities—whether you’re working from the cloud, on premises, or a hybrid environment. Learn the risks of internet exposed remote desktop protocol (rdp), steps to provide secure remote access, and what coalition scan data shows about the risk. Cis guide explains how best to secure remote desktop protocol (rdp) to protect and defend against the most pervasive cyber threats that are faced today. Learn how to prevent rdp brute force attacks with vpn, mfa, nla, account lockouts, and monitoring. secure your rdp access in 8 steps.
Comments are closed.