Ransomware Protection Guide Pdf Ransomware Security

Ransomware Response Guide Pdf Pdf Ransomware Malware This playbook provides a clear roadmap to prepare for, respond to, and recover from ransomware so your business can stay resilient no matter what comes your way. These ransomware best practices and recommendations are based on operational insight from the cybersecurity and infrastructure security agency (cisa) and the multi state information sharing and analysis center (ms isac).
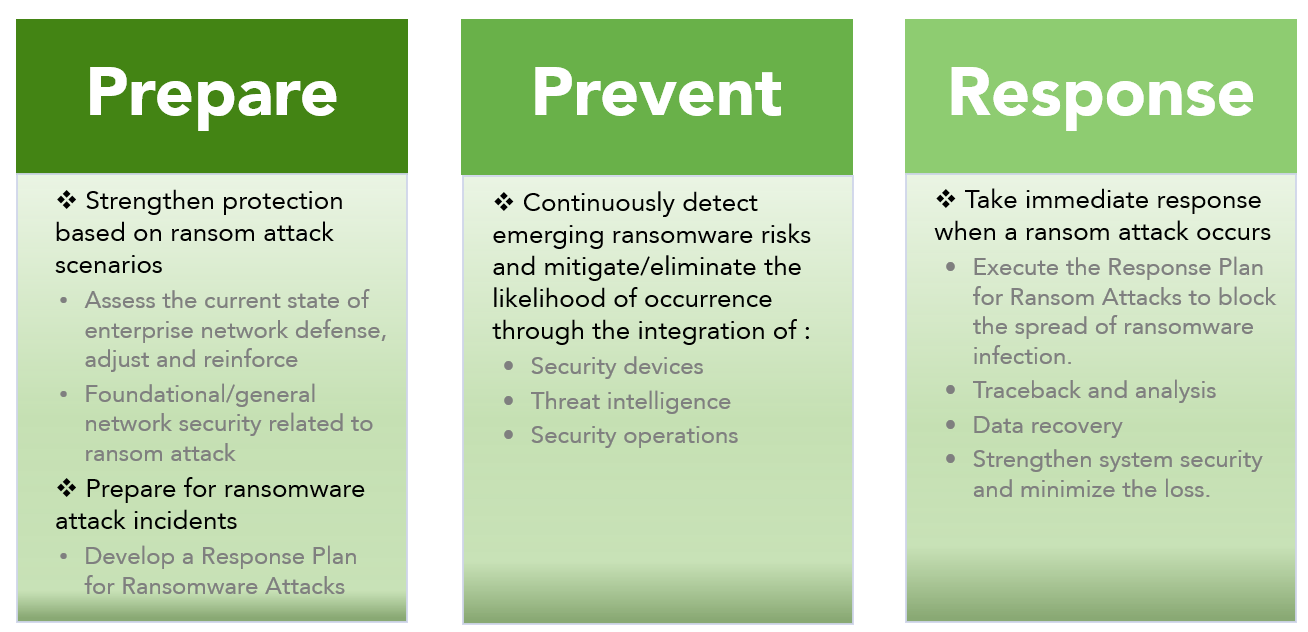
Prepare Prevent And Response A Comprehensive Ransomware Protection Ransomware tactics may change over time, but the security posture required to protect the network will not, so this book outlines some best practices for keeping the network safe. This ransomware profile identifies the cybersecurity framework version 1.1 security objectives that support identifying, protecting against, detecting, responding to, and recovering from ransomware events. the profile can be used as a guide to managing the risk of ransomware events. These configurations can be enforced via the previously mentioned “microsoft security guide” group policy template from the microsoft security compliance toolkit. Ransomware, as the name suggests, is a type of malicious software (malware) that infects your system and encrypts your data. once affected, you are denied access to your data until you pay a “ransom” to buy the decryption key.
Ransomware Protection Threatdown By Malwarebytes These configurations can be enforced via the previously mentioned “microsoft security guide” group policy template from the microsoft security compliance toolkit. Ransomware, as the name suggests, is a type of malicious software (malware) that infects your system and encrypts your data. once affected, you are denied access to your data until you pay a “ransom” to buy the decryption key. This article provides a comprehensive guide to ransomware defense, offering best practices that enterprises can implement to mitigate the risks associated with these increasingly. Ransomware attacks are designed to stop your business operating so you feel you have no choice but to pay an exorbitant ransom. typically, attackers will try to steal important company data, and run malware that encrypts your computers, making them unusable. The kela ransomware protection suite combines advanced threat intelligence, real time identity monitoring, and automated defense capabilities to deliver a powerful, technical solution against the #1 cyber threat—ransomware. Criminals plant ransomware on websites and take advantage of software vulnerabilities to launch attacks on visitors using outdated software (browser, browser plugin).
Ransomware Pdf Pdf This article provides a comprehensive guide to ransomware defense, offering best practices that enterprises can implement to mitigate the risks associated with these increasingly. Ransomware attacks are designed to stop your business operating so you feel you have no choice but to pay an exorbitant ransom. typically, attackers will try to steal important company data, and run malware that encrypts your computers, making them unusable. The kela ransomware protection suite combines advanced threat intelligence, real time identity monitoring, and automated defense capabilities to deliver a powerful, technical solution against the #1 cyber threat—ransomware. Criminals plant ransomware on websites and take advantage of software vulnerabilities to launch attacks on visitors using outdated software (browser, browser plugin).

Ransomware Detection And Protection Anonymous Pdf The kela ransomware protection suite combines advanced threat intelligence, real time identity monitoring, and automated defense capabilities to deliver a powerful, technical solution against the #1 cyber threat—ransomware. Criminals plant ransomware on websites and take advantage of software vulnerabilities to launch attacks on visitors using outdated software (browser, browser plugin).
Comments are closed.