Quickstart Cybersecurity Project 2 Vulnerability Assessment Risk Analysis

Week 2 Risk Assessment Download Free Pdf Security Computer Security This project demonstrates hands on experience in vulnerability assessment, risk analysis, and securing both internal and externally exposed systems. show less. This project documents a cybersecurity assessment for a client's production server (internal network) and web server (dmz). the goal was to identify vulnerabilities, demonstrate exploitation, create persistence, locate sensitive information, and crack passwords (bonus).

Cybersecurity Risk Assessment Guide Pdf A good cybersecurity risk assessment template includes sections for asset inventory, threat identification, vulnerability documentation, risk analysis, and treatment planning. Learn how to conduct a security risk assessment to identify vulnerabilities and take action to safeguard your systems against cyber threats. The steps involved in conducting a cybersecurity risk assessment include identifying assets, assessing vulnerabilities, evaluating threats, determining the potential impact, and implementing risk mitigation strategies. This draft explains how to find, filter, and apply informative references using nist tools. review and submit comments here. the final version of nist cybersecurity framework 2.0: cybersecurity, enterprise risk management, and workforce management quick start guide.

Guide To Conducting Cybersecurity Risk Assessment For Cii Pdf The steps involved in conducting a cybersecurity risk assessment include identifying assets, assessing vulnerabilities, evaluating threats, determining the potential impact, and implementing risk mitigation strategies. This draft explains how to find, filter, and apply informative references using nist tools. review and submit comments here. the final version of nist cybersecurity framework 2.0: cybersecurity, enterprise risk management, and workforce management quick start guide. Simulate a small business network setup. perform a vulnerability scan using nessus openvas. identify and categorize threats and vulnerabilities. In this post, learn what the seven key steps for conducting a comprehensive cybersecurity risk assessment are and why it's important to perform one. Management of secret authentication information of users defined policy for. rmation of users? 9.2.5 review of user acces. rights? 9.2.6 removal or adjustment of access rights . ilities 9.3.1 use of secret authentication information de. n access control 9.4.1 information access restric. ccess restrictions? 9.4.2 secure log o. Learn how to perform a cyber security risk assessment with 7 essential steps to identify threats, reduce exposure and protect your organisation.
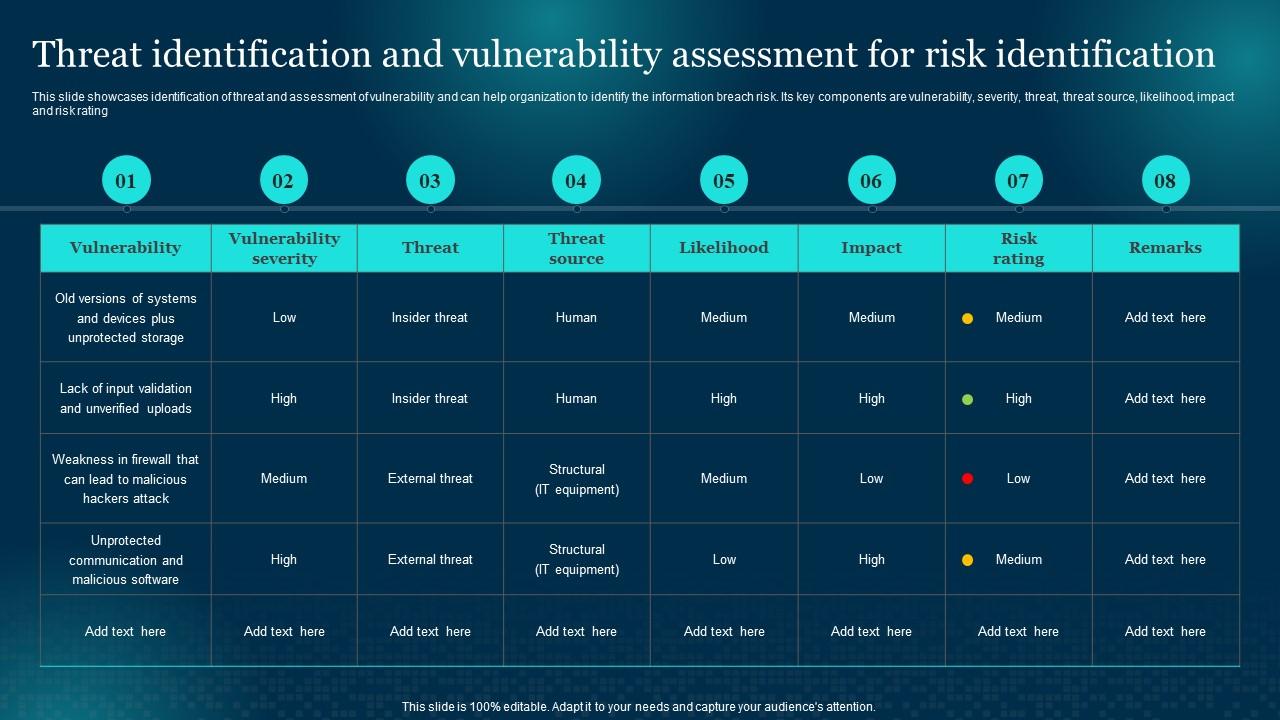
Threat Identification And Vulnerability Assessment For Cybersecurity Simulate a small business network setup. perform a vulnerability scan using nessus openvas. identify and categorize threats and vulnerabilities. In this post, learn what the seven key steps for conducting a comprehensive cybersecurity risk assessment are and why it's important to perform one. Management of secret authentication information of users defined policy for. rmation of users? 9.2.5 review of user acces. rights? 9.2.6 removal or adjustment of access rights . ilities 9.3.1 use of secret authentication information de. n access control 9.4.1 information access restric. ccess restrictions? 9.4.2 secure log o. Learn how to perform a cyber security risk assessment with 7 essential steps to identify threats, reduce exposure and protect your organisation.
Comments are closed.