Quantum Vs Classical Cryptography Pdf Cryptography Public Key

Module89105 7122 4690301 Group 5 Classical Cryptography And Unlike classical encryption, qkd provides information theoretic security, making it resistant to both classical and quantum adversaries. this paper provides a literature review of the qkd, protocols like bb84 and modern qkd systems like the di qkd system. To provide a unified overview of the cryptographic landscape under the lens of quantum computing, we present a comparative analysis between widely deployed classical algorithms and emerging post quantum candidates.

Quantum Cryptography Thesis Pdf Pdf Cryptography Public Key In quantum cryptography, quantum key distribution (qkd) is used for generating a secret key shared between two parties using two channels as a quantum channel and an authenticated classical channel. This paper provides the comparative analysis on classical and quantum cryptography using various cryptographic algorithms to identify the best algorithm in classical or quantum. While classical cryptography relies on mathematical computation, quantum cryptography is based on the laws of quantum mechanics. in this paper, we will discuss the di erent cryptography algorithms as well as comparing the advantages and disadvantages of both schemes. Quantum cryptography (qc) offers a theoretically secure alternative to classical cryptography (cc), which relies on mathematical complexity. classical cryptography faces vulnerabilities due to computational assumptions and requires secure key distribution.
Quantum Cryptography Pdf While classical cryptography relies on mathematical computation, quantum cryptography is based on the laws of quantum mechanics. in this paper, we will discuss the di erent cryptography algorithms as well as comparing the advantages and disadvantages of both schemes. Quantum cryptography (qc) offers a theoretically secure alternative to classical cryptography (cc), which relies on mathematical complexity. classical cryptography faces vulnerabilities due to computational assumptions and requires secure key distribution. General problems in classical cryptography we do not know if there exists an algorithm that breaks the encryption (classical or quantum) — encryption can be broken anytime “store now, decrypt later” attacks make quantum computers already a security. This paper seeks to create a new scheme in qkd that will communicate between two parties and will give them a high level of security against any well known attacks while handling both of parties in a manner that will reduce their dependency on both classic communication and the classical channel. Post quantum cryptography aims to develop cryptographic algorithms that are secure against both classical and quantum computers, in response to potential weaknesses in classical cryptographic algorithms from advances in computing power and quantum computers. But here we are going to concentrate on the two types of cryptography techniques namely classical cryptography and quantum cryptography. what is classical cryptography? classical cryptography is based on mathematics and it relies on the computational difficulty of factorizing large numbers.
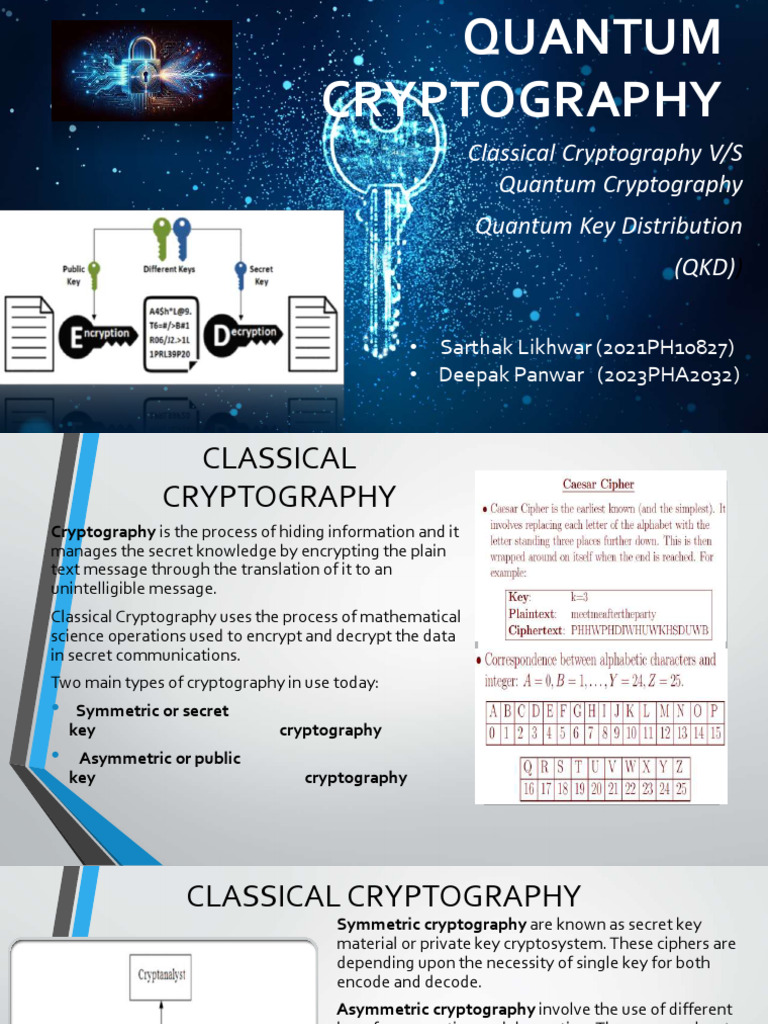
Quantum Cryptography Pdf Cryptography Key Cryptography General problems in classical cryptography we do not know if there exists an algorithm that breaks the encryption (classical or quantum) — encryption can be broken anytime “store now, decrypt later” attacks make quantum computers already a security. This paper seeks to create a new scheme in qkd that will communicate between two parties and will give them a high level of security against any well known attacks while handling both of parties in a manner that will reduce their dependency on both classic communication and the classical channel. Post quantum cryptography aims to develop cryptographic algorithms that are secure against both classical and quantum computers, in response to potential weaknesses in classical cryptographic algorithms from advances in computing power and quantum computers. But here we are going to concentrate on the two types of cryptography techniques namely classical cryptography and quantum cryptography. what is classical cryptography? classical cryptography is based on mathematics and it relies on the computational difficulty of factorizing large numbers.

Classical Cryptography Pdf Cipher Encryption Post quantum cryptography aims to develop cryptographic algorithms that are secure against both classical and quantum computers, in response to potential weaknesses in classical cryptographic algorithms from advances in computing power and quantum computers. But here we are going to concentrate on the two types of cryptography techniques namely classical cryptography and quantum cryptography. what is classical cryptography? classical cryptography is based on mathematics and it relies on the computational difficulty of factorizing large numbers.
Comments are closed.