Quantum Cryptography Reviewing Post Quantum Cryptography Computer

Quantum Cryptography Vs Post Quantum Cryptography Synopsys The core of cryptography is to transform data into unreadable format. with the introduction of quantum systems, it has been proved that many traditional cryptographic schemes are unsecure and can be broken with quantum computers. this chapter presents a brief review of pre and post quantum systems. This chapter will argue that post quantum cryptography is more practical and trusted for most real world systems than quantum key distribution (qkd).
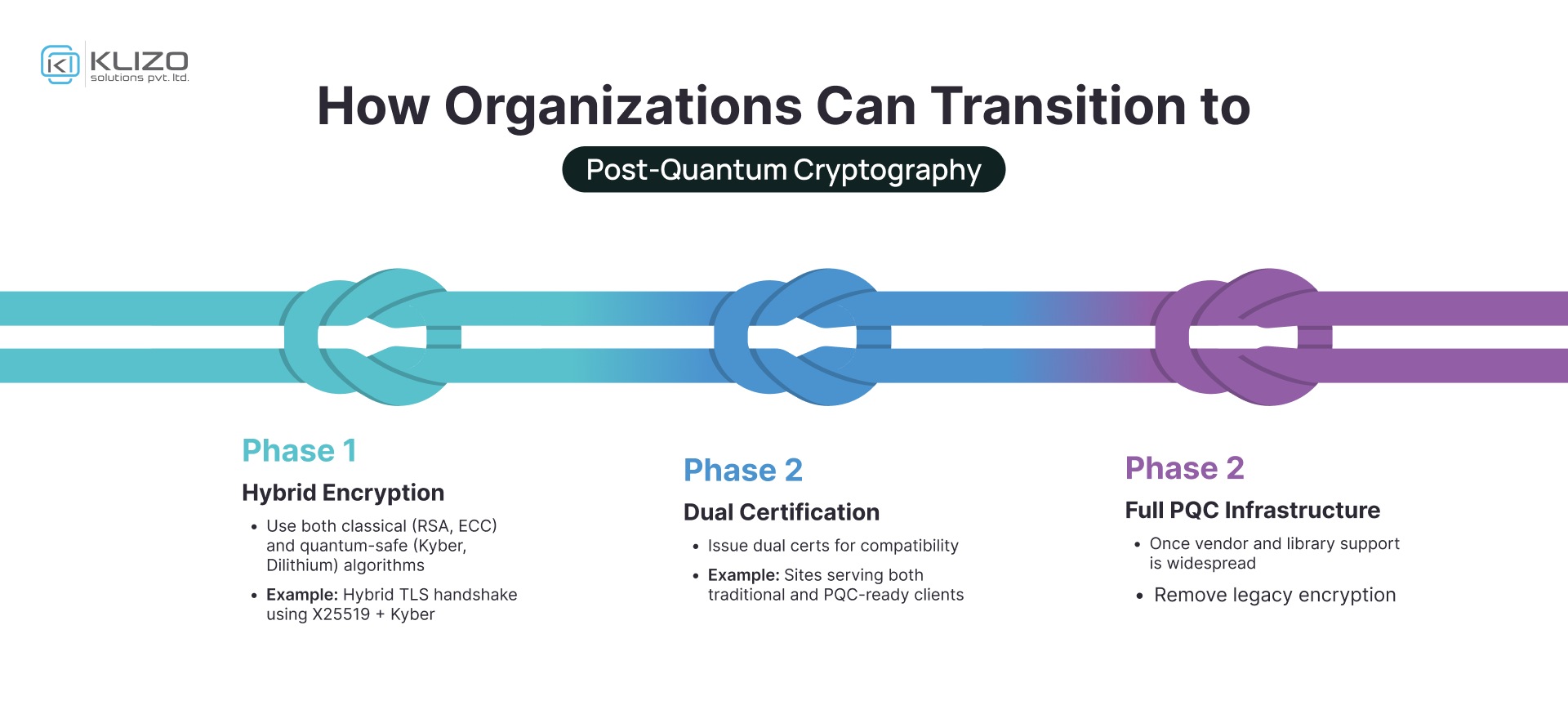
Post Quantum Cryptography The Future Of Secure Computing Klizos This white paper explains the urgency of the quantum threat, explores the emerging field of post quantum cryptography (pqc), and provides guidance on how organizations can prepare. We are in a race against time to deploy post quantum cryptography before quantum computers arrive. this review surveys what cryptography does and the damage done by quantum. With the advent of quantum computing, the security of traditional pki systems is at risk, prompting a need for post quantum pki solutions that can withstand quantum attacks while maintaining compatibility with existing infrastructure. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems.
Post Quantum Cryptography Webnic With the advent of quantum computing, the security of traditional pki systems is at risk, prompting a need for post quantum pki solutions that can withstand quantum attacks while maintaining compatibility with existing infrastructure. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems. The paper provides an in depth overview of cryptography in the quantum era, including a detailed examination of various post quantum cryptographic approaches such as lattice based,. The threat posed by quantum computing has prompted a major change in cryptographic security known as post quantum cryptography. even though nist's standardization initiatives have sped up development, issues with performance, key sizes, and practical implementation still exist. Post quantum cryptography (pqc) has become the primary defense against the vulnerabilities that large scale quantum computing introduces to traditional cryptographic systems. This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. we analyze current readiness, standardization initiatives, hybrid cryptographic approaches, and deployment challenges across multiple layers of the protocol stack, including tls, ssh, vpns, certificate.
Post Quantum Cryptography Webnic The paper provides an in depth overview of cryptography in the quantum era, including a detailed examination of various post quantum cryptographic approaches such as lattice based,. The threat posed by quantum computing has prompted a major change in cryptographic security known as post quantum cryptography. even though nist's standardization initiatives have sped up development, issues with performance, key sizes, and practical implementation still exist. Post quantum cryptography (pqc) has become the primary defense against the vulnerabilities that large scale quantum computing introduces to traditional cryptographic systems. This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. we analyze current readiness, standardization initiatives, hybrid cryptographic approaches, and deployment challenges across multiple layers of the protocol stack, including tls, ssh, vpns, certificate.
Comments are closed.