Python Microservices Securing Ai Applications Explained
Securing Your Python Applications Best Practices Microservices offer flexibility and scalability, making them ideal for ai applications, which often require robust infrastructure to handle complex computations and large datasets. this article explores how microservices can enhance ai applications, promoting scalability, flexibility, and efficiency. ai and microservices architecture. 🤖 are your ai applications as secure as they should be? ⚡ discover the pivotal strategies to protect your python microservices in this engaging guide! 🚀 in this video, we delve into the.
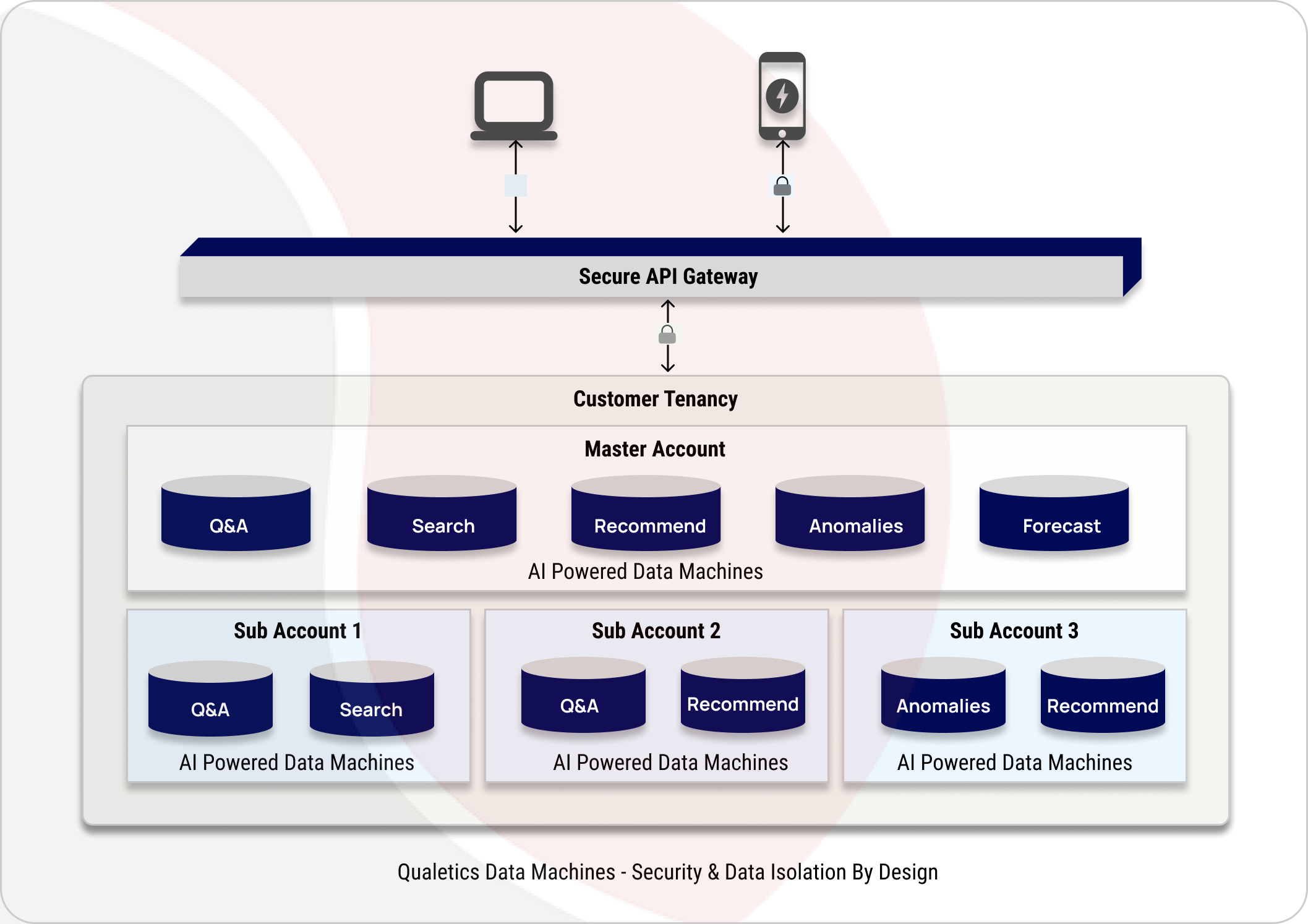
How To Build Secure Ai Applications Adopting a microservices architecture means breaking these tasks into independent services that communicate over apis. why do this for ai? the primary benefits are scalability, maintainability,. In this tutorial, you’ll learn how to leverage cloving’s command line capabilities to streamline the development of python microservices while maintaining top notch security standards. Discover the top python security best practices for apis and microservices. learn how to secure authentication, encryption, and deployments for safer, scalable backend systems. Prompt injection, rogue agents, shadow apis — ai expands your attack surface fast. learn 5 security best practices for ai integrated microservices at scale.

Python Security A Comprehensive Guide To Securing Code And Applications Discover the top python security best practices for apis and microservices. learn how to secure authentication, encryption, and deployments for safer, scalable backend systems. Prompt injection, rogue agents, shadow apis — ai expands your attack surface fast. learn 5 security best practices for ai integrated microservices at scale. This walkthrough helps you build ai microservices that are easier to maintain, scale, and ship with confidence. from folder structure to deployment basics, the reasons why each boundary exists. these choices directly affect scalability, deployment speed, and system reliability. This article demonstrates how to implement a comprehensive ai powered defense in depth security architecture for serverless microservices on amazon web services (aws). There are many security challenges that need to be addressed in the application design and implementation phases. the fundamental security requirements that have to be addressed during design phase are authentication and authorization. From foundational ideas like least privilege and defense in depth to real world practices including zero trust, encryption, observability, and service meshes, it guides you through making security decisions in microservice environments.
Comments are closed.