Purdue Model Segmentation Details Techyengineer
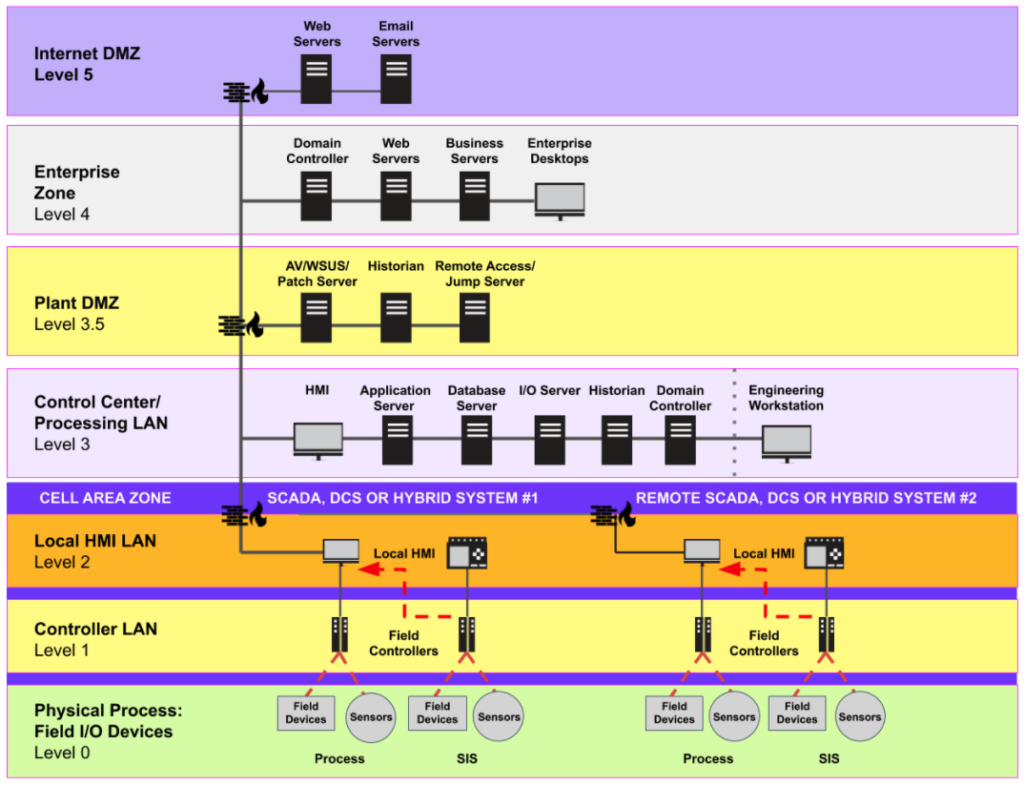
Purdue Model Segmentation Details Techyengineer The purdue model ensures defense in depth, prioritizing ot availability safety while enabling secure data flows for mining 4.0 analytics and digital twins. implementation starts with visibility, then macro segmentation (it ot split idmz), progressing to micro. By clearly defining and segmenting the different layers of ics and it systems, the purdue model offers a structured approach to managing both operational efficiency and cybersecurity.
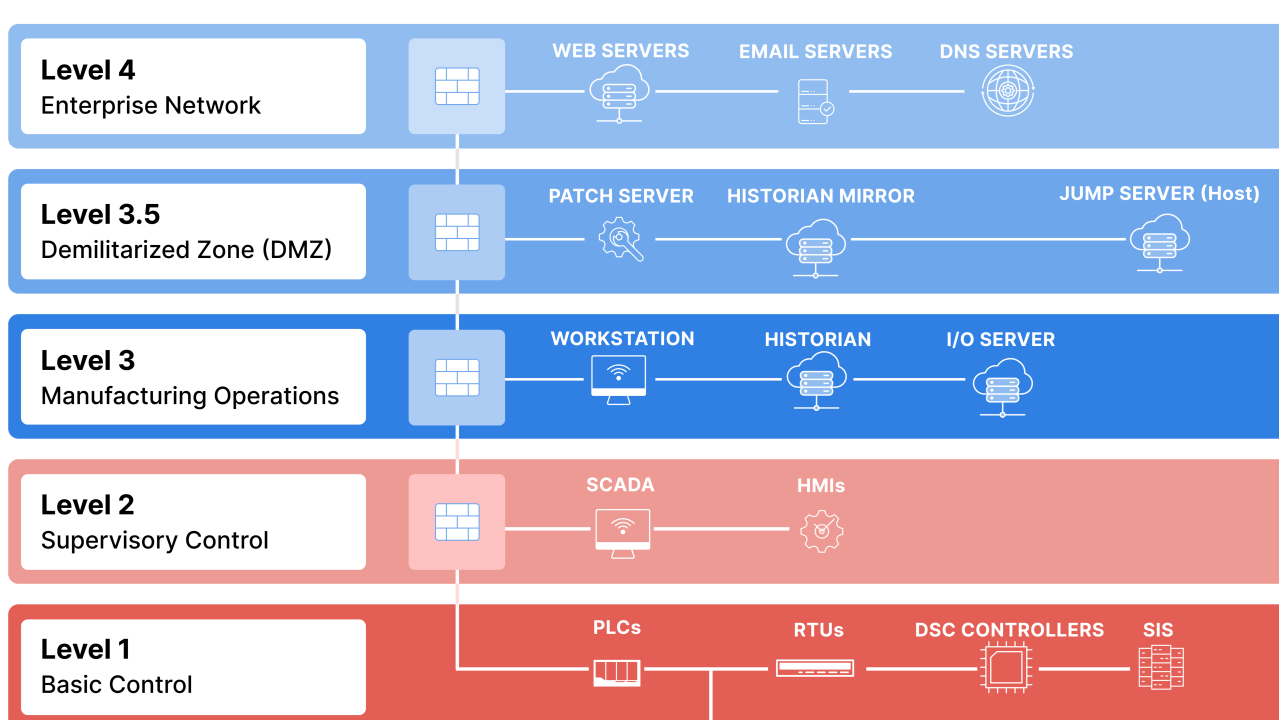
Purdue Model Segmentation Details Techyengineer Network segmentation is fundamental to ics security and the purdue model creates distinct security zones within the ics environment. this approach provides a defense in depth strategy, limiting the impact of a breach, and hindering the lateral movement of attackers within the network. In this article, we will discuss three ways that the purdue model can help organizations limit the scope of what an adversary can do or access within their converged enterprise and how they can enable industrial operational resilience. The purdue model essentially divides an industrial network into layers, each with its own purpose, responsibilities, and communication flow. understanding this model helps both security. The purdue model is a layered way to describe industrial systems, from physical devices on the shop floor up to business systems. it is useful for understanding the environment, but it is not enough on its own for modern segmentation planning.
Purdue Model For Ics Security Segmentation Emberot The purdue model essentially divides an industrial network into layers, each with its own purpose, responsibilities, and communication flow. understanding this model helps both security. The purdue model is a layered way to describe industrial systems, from physical devices on the shop floor up to business systems. it is useful for understanding the environment, but it is not enough on its own for modern segmentation planning. The purdue model of cybersecurity provides a framework for understanding the complex layers of security required to protect ot environments. in this article, we will delve into the purdue model and explore its application to safeguarding ot systems. Learn about the purdue model for industrial network architecture. understand ot security zones, network segmentation, and best practices for protecting industrial control systems. The purdue model is widely used in industrial control systems (ics) and cybersecurity to segment and secure networks. it helps in creating a defensible environment by segmenting industrial control system networks from corporate enterprise networks and the internet. Agent.py top file metadata and controls code blame 213 lines (179 loc) · 7.53 kb raw download raw file audits ot ics network segmentation against the purdue enterprise reference architecture by testing connectivity between network zones, import argparse.

Purdue Model Alpha Ot Solution The purdue model of cybersecurity provides a framework for understanding the complex layers of security required to protect ot environments. in this article, we will delve into the purdue model and explore its application to safeguarding ot systems. Learn about the purdue model for industrial network architecture. understand ot security zones, network segmentation, and best practices for protecting industrial control systems. The purdue model is widely used in industrial control systems (ics) and cybersecurity to segment and secure networks. it helps in creating a defensible environment by segmenting industrial control system networks from corporate enterprise networks and the internet. Agent.py top file metadata and controls code blame 213 lines (179 loc) · 7.53 kb raw download raw file audits ot ics network segmentation against the purdue enterprise reference architecture by testing connectivity between network zones, import argparse.

Purdue Model The purdue model is widely used in industrial control systems (ics) and cybersecurity to segment and secure networks. it helps in creating a defensible environment by segmenting industrial control system networks from corporate enterprise networks and the internet. Agent.py top file metadata and controls code blame 213 lines (179 loc) · 7.53 kb raw download raw file audits ot ics network segmentation against the purdue enterprise reference architecture by testing connectivity between network zones, import argparse.
Comments are closed.