Public Key Cryptography Pdf Cryptography Public Key Cryptography

Public Key Cryptography Pdf Public Key Cryptography Encryption With a public key cryptosystem, the key used to encipher a message can be made public without compromising the secrecy of a different key needed to decipher that message. Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair.
Principles Of Public Key Cryptography Pdf Public Key Cryptography Public key encryption means the algorithm has two keys: one public and one private. in this section, we explore public key encryption and the rsa encryption algorithm, named after the algorithm's inventors ron rivest, adi shamir, and len adleman. Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key. Pdf | public key cryptography or asymmetric key cryptography, is a cryptographic system that uses two pairs of keys, public and private to encrypt data, | find, read and cite all. 8.1 principles of public key cryptosystems evelopment of digital signatures. in 1976 whitfield diffie and martin hell man achieved great success in de eloping the conceptual framework. for conventional encryption the same key is u ed for encryption and decryption.
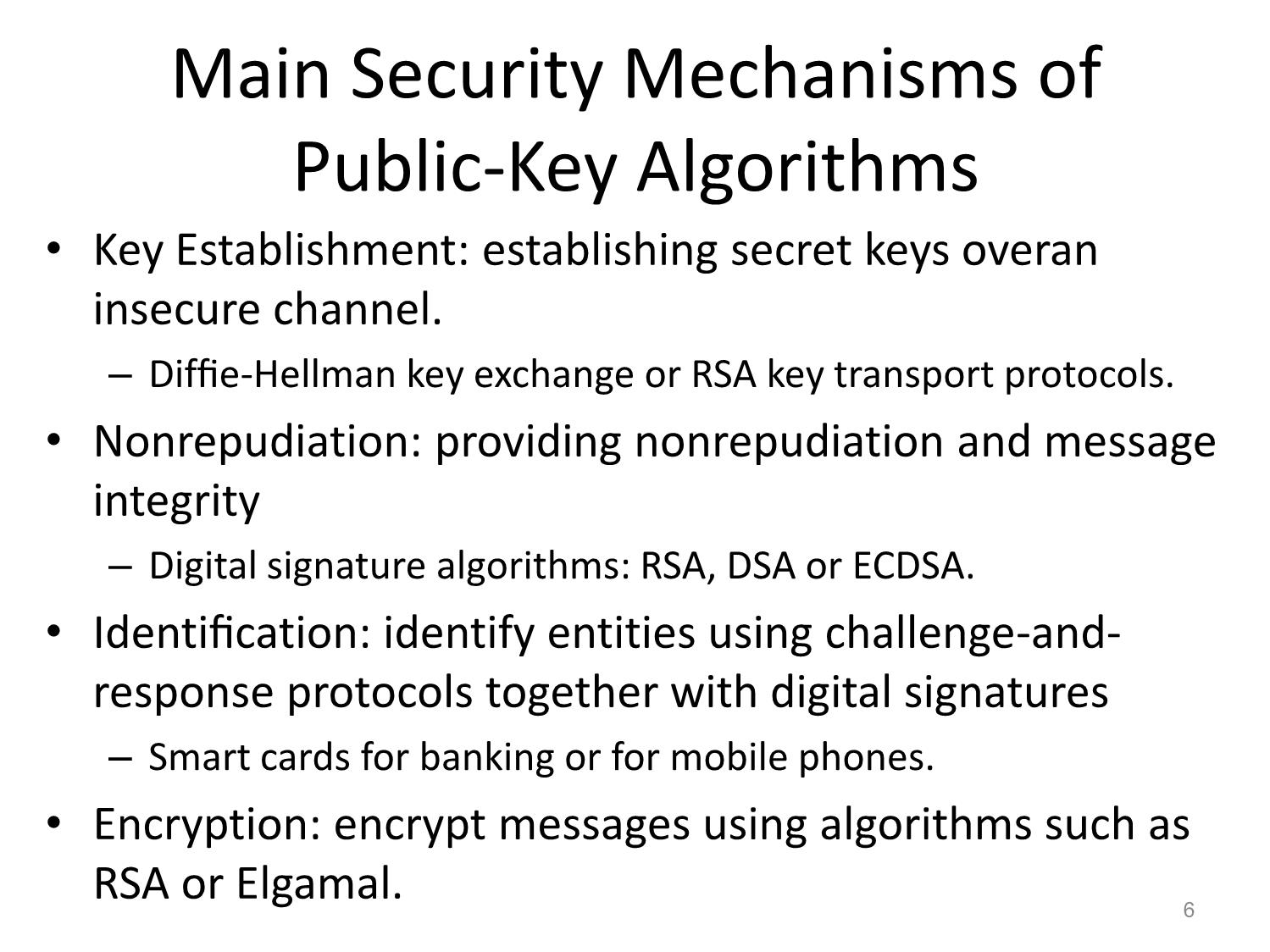
Public Key Cryptography Pdf | public key cryptography or asymmetric key cryptography, is a cryptographic system that uses two pairs of keys, public and private to encrypt data, | find, read and cite all. 8.1 principles of public key cryptosystems evelopment of digital signatures. in 1976 whitfield diffie and martin hell man achieved great success in de eloping the conceptual framework. for conventional encryption the same key is u ed for encryption and decryption. Public key algorithms rely on one key for encryption and a different but related key for decryption. these algorithms have the following important characteristics:. In particular, public key encryption is most commonly used to transmit keys (the functionality is often called key transport or key encapsulation), rather than to encrypt data. However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Hal is a multi disciplinary open access archive for the deposit and dissemination of sci entific research documents, whether they are pub lished or not. the documents may come from teaching and research institutions in france or abroad, or from public or private research centers.
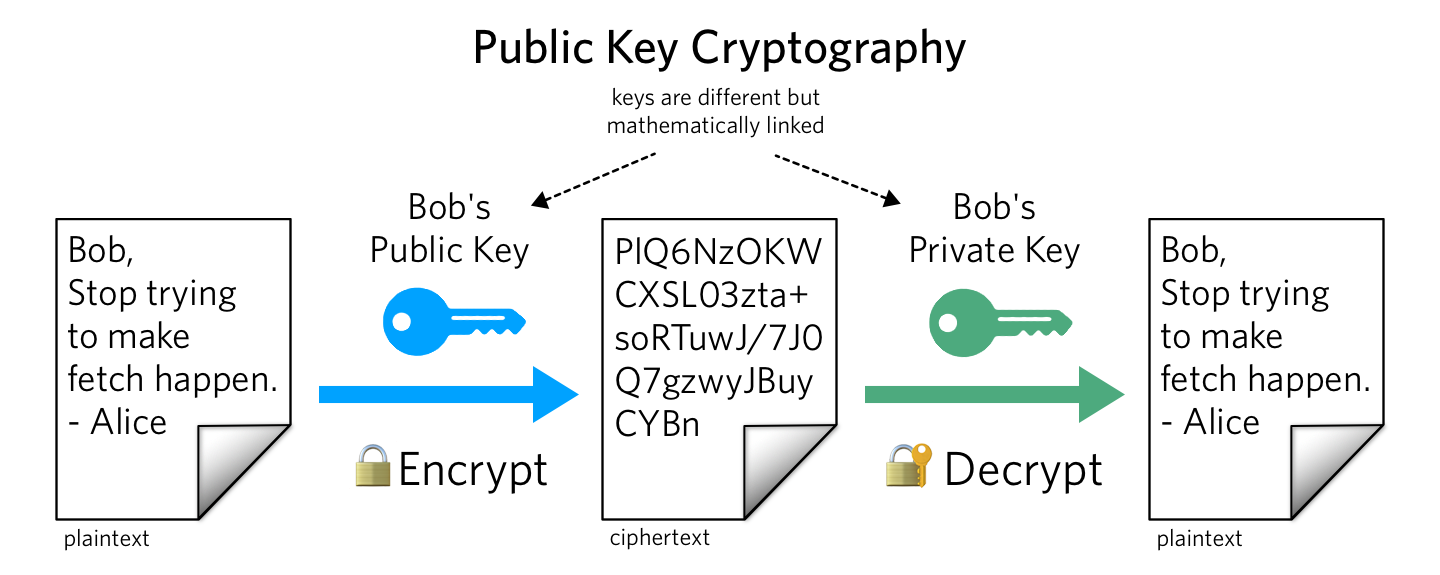
What Is Public Key Cryptography Twilio Public key algorithms rely on one key for encryption and a different but related key for decryption. these algorithms have the following important characteristics:. In particular, public key encryption is most commonly used to transmit keys (the functionality is often called key transport or key encapsulation), rather than to encrypt data. However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Hal is a multi disciplinary open access archive for the deposit and dissemination of sci entific research documents, whether they are pub lished or not. the documents may come from teaching and research institutions in france or abroad, or from public or private research centers.
Public Key Cryptography A Comprehensive Guide 2025 However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Hal is a multi disciplinary open access archive for the deposit and dissemination of sci entific research documents, whether they are pub lished or not. the documents may come from teaching and research institutions in france or abroad, or from public or private research centers.
Comments are closed.