Public Key Cryptography Cryptography And Network
Public Key Cryptography Network Encyclopedia There are many kinds of public key cryptosystems, with different security goals, including digital signature, diffie–hellman key exchange, public key key encapsulation, and public key encryption. Public key cryptography provides a secure way to exchange information and authenticate users by using pairs of keys. the public key is used for encryption and signature verification, while the private key is used for decryption and signing.
Public Key Cryptography The development of public key cryptography is the greatest and perhaps the only true revolution in the entire history of cryptography. it is asymmetric, involving the use of two separate keys, in contrast to symmetric encryption, which uses only one key. Public key infrastructure (pki) refers to a way used to support the secured exchange of data as well as information on the internet. pki relies on public key cryptography, digital signatures, and certificates to guarantee the integrity of data through networks. Asymmetric algorithms, also called public key algorithms, are designed so that the key that is used for encryption is different from the key that is used for decryption. However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc.

Cryptography Public Key Concept Stable Diffusion Online Asymmetric algorithms, also called public key algorithms, are designed so that the key that is used for encryption is different from the key that is used for decryption. However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Public key cryptography uses a pair of keys to secure communications: a private key that is kept secret and a public key that can be widely distributed. some examples of public key cryptography algorithms include rsa, dh, and elgamal. Network security measures are needed to protect data during transmission. but keep in mind that, it is the information and our ability to access that information that we are really trying to protect and not the computers and networks. Whereas secret key cryptography uses a single key shared by two (or more) parties, public key cryptography uses a pair of keys for each party. one of the keys of the pair is "public" and the other is "private.". Public key cryptography, also called asymmetric cryptography, uses a public key and private key for encrypting communications transmitted across the internet.

What Is Public Key Cryptography Fortris Public key cryptography uses a pair of keys to secure communications: a private key that is kept secret and a public key that can be widely distributed. some examples of public key cryptography algorithms include rsa, dh, and elgamal. Network security measures are needed to protect data during transmission. but keep in mind that, it is the information and our ability to access that information that we are really trying to protect and not the computers and networks. Whereas secret key cryptography uses a single key shared by two (or more) parties, public key cryptography uses a pair of keys for each party. one of the keys of the pair is "public" and the other is "private.". Public key cryptography, also called asymmetric cryptography, uses a public key and private key for encrypting communications transmitted across the internet.
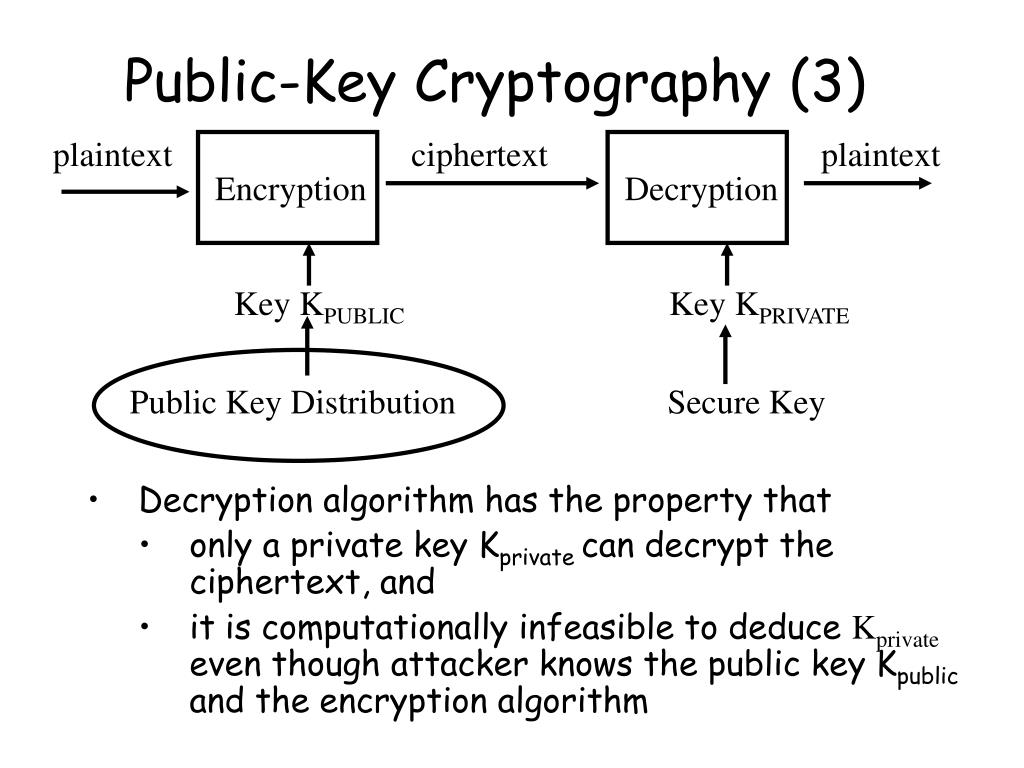
Ppt Network Security Principles Symmetric Key Cryptography Public Whereas secret key cryptography uses a single key shared by two (or more) parties, public key cryptography uses a pair of keys for each party. one of the keys of the pair is "public" and the other is "private.". Public key cryptography, also called asymmetric cryptography, uses a public key and private key for encrypting communications transmitted across the internet.

An Introduction To Public Key Cryptography 101 Blockchains
Comments are closed.