Protocols Internetprotocol Networksecurity Thesecmaster

02 Network Security Protocols Pdf Transport Layer Security Used mainly for testing and legacy systems. 3. network security these protocols secure the data in passage over a network. these protocols also determine how the network secures data from any unauthorized attempts to extract or review data. these protocols make sure that no unauthorized devices, users, or services can access the network data. What is internet protocols and it's types? 4 types of internet protocol 1 application layer 2 trasport layer 3 network layer 4 data link layer ♻️….
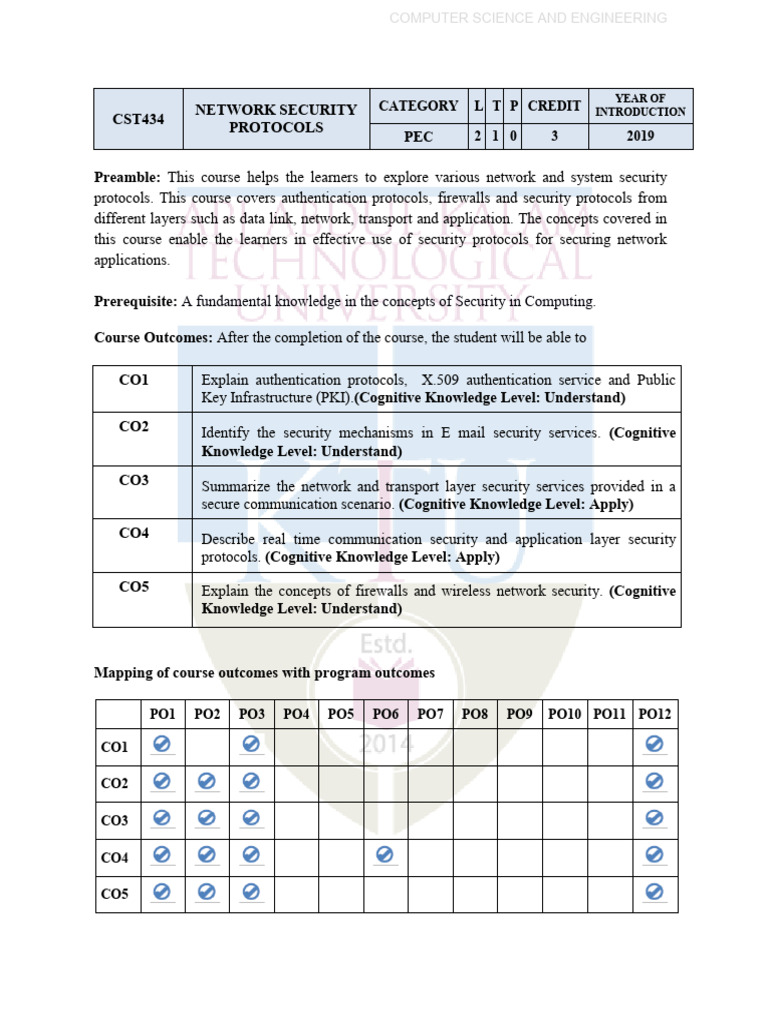
Network Security Protocols S8 Cse 2019 Scheme Syllabus Pdf Explore various types of network security protocols from basic tcp ip to advanced kerberos and tacacs to strengthen your organization's cybersecurity. Thesecmaster, a cyber security nexus, was founded in 2020 by arun kl, a security professional. thesecmaster was started with a vision of spreading awareness about the growing cyber threats across the globe and helping all communities learn how to be secured from emerging cyber threats. Network security protocols generally implement cryptography and encryption techniques to secure the data so that it can only be decrypted. Network protocols are sets of rules that define how data is transmitted and received across a network. they ensure reliable communication between devices.

Protocols Network Protection Threats Network Security Prevention Network security protocols generally implement cryptography and encryption techniques to secure the data so that it can only be decrypted. Network protocols are sets of rules that define how data is transmitted and received across a network. they ensure reliable communication between devices. Routing (bgp) bgp (border gateway protocol): protocol that allows routers to exchange information about their routing tables each router announces what it can route to all of its neighbors. every router maintains a global table of routes. Both ipsec (internet protocol security) and vpns (virtual private networks) rely on a group of security protocols that work together to encrypt communication between devices, keeping data safe when you connect to public networks, such as unsecured wi fis. Chapter 19 covers ip security, including ipsec protocols (ah, esp), transport tunnel modes, key management (ikev2), and security services for network communications. Learn about the network security protocols that are used to augment or replace insecure network protocols, lacking encryption, authentication, and more.

Top 7 Network Security Protocols For Internet Safety 2025 Routing (bgp) bgp (border gateway protocol): protocol that allows routers to exchange information about their routing tables each router announces what it can route to all of its neighbors. every router maintains a global table of routes. Both ipsec (internet protocol security) and vpns (virtual private networks) rely on a group of security protocols that work together to encrypt communication between devices, keeping data safe when you connect to public networks, such as unsecured wi fis. Chapter 19 covers ip security, including ipsec protocols (ah, esp), transport tunnel modes, key management (ikev2), and security services for network communications. Learn about the network security protocols that are used to augment or replace insecure network protocols, lacking encryption, authentication, and more.
Top 10 Network Security Protocols Techy20 Chapter 19 covers ip security, including ipsec protocols (ah, esp), transport tunnel modes, key management (ikev2), and security services for network communications. Learn about the network security protocols that are used to augment or replace insecure network protocols, lacking encryption, authentication, and more.
Comments are closed.